EU Security Agency Says Cyber Security Critical To The Success Of Mobile Payments
Get Tom's Hardware's best news and in-depth reviews, straight to your inbox.
You are now subscribed
Your newsletter sign-up was successful
The European Union Agency for Network and Information Security (ENISA) published a new report in which it argues that for all citizens to adopt mobile payments the smartphone manufacturers will have to employ good security for all mobile payment systems. Without it, trust in the systems will erode, and adoption will slow down. The report also offers a set of minimum security recommendations for mobile payments providers, customers, and merchants.
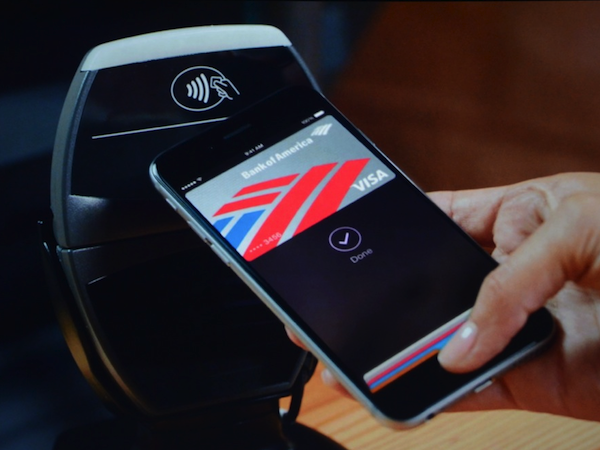
Smartphones As Digital Wallets
Mobile payments work on the principle of storing your credit card information on your smartphone and then using that information instead of your credit card to pay for products. This may make it a little more convenient for customers if they want to keep everything from their smart door authentication to credit card information on a single device instead of also carrying a wallet and keys.
However, because smartphones use essentially full operating systems, they’re also exposed to many of the same type of attacks and malware as computers. If the smartphone doesn’t store credit card information and other sensitive information in a highly secure way, it may make users much more vulnerable to hacking attempts.
Article continues belowThis situation isn’t helped by most smartphone makers, which often focus more on selling customers their next phones instead of patching the security flaws of the existing ones in a timely manner or supporting them and for a longer period of time.
A survey of 900 security experts discovered that only 23% of them believe that security for current mobile payments are sufficiently robust, while 47% believed that mobile payments systems offer no security, and 30% were unsure.
Threats Against Mobile Payments
ENISA identified a number of threats against mobile payments systems that include:
Mobile user threats - installation of rogue and malware applications, phishing and social engineeringMobile device threats - unauthorized access, lost or stolen deviceMobile payment application and wallet threats - reverse engineering, tampering with the payment application and the use of rootkitsMerchant threats - Point of Sale (POS) malware, Man-in-the-Middle (MiTM) and replay attacksPayment service providers’ and Acquirers threats - payment system compromise and data connectivity compromisePayment Network Providers Threats- token service compromise and denial of serviceIssuers Threats – payment authorization process compromise, token data compromiseMobile Payment Applications Providers threats – compromise of sensitive data, compromise of user profiles managed in the cloud, token compromise and denial of service attacks
Get Tom's Hardware's best news and in-depth reviews, straight to your inbox.
Due to all of these potential threats against all the mobile payments systems, which each come with varying degrees of security, ENISA aims to create some security guidelines as well as minimum security recommendations for companies that provide mobile payments in the European Union.
Customer Security Measures
ENISA believes that first, the mobile payment providers should make customers and merchants aware of the risks and consequences of conducting financial transactions with a mobile application.
To protect themselves against cybercrime, customers should ensure they update their mobile operating systems as soon as they receive an update from the device maker or the OS vendor (provided they send updates in the first place).
The network transport should be secure, and customers shouldn’t use open Wi-Fi hotspots to finish the transaction. Some mobile payment systems such as Apple Pay don’t require connection to the Internet, but others do. Authentication for the mobile payment should be enforced with a fingerprint or PIN, according to ENISA. This type of authentication is already a feature with most of the major mobile payment systems.
Customers should also be able to remotely wipe their information from the device in case the device is stolen.
Merchants Security Measures
ENISA recommended that merchants should update their POS software as soon as an update is released, as they are often a high-priority target for attackers. The POS makers should also make the merchants aware if there are hardware flaws they need to remediate in the POS equipment.
Mobile Payment App Security Measures
ENISA recommended the developers of mobile payment apps to develop them with security in mind from the beginning. The minimum security measures should include:
Avoiding hard-coded sensitive information such as passwords or keys.Employing anti-reversing techniques.When possible, verifying the integrity of the running code, to ensure that it has not been back-doored. This includes the importance of provisioning the application only through trusted application stores.When possible minimizing at all times potential man-in-the-middle attacks by implementing effective certificate pinning to ensure that the application is communicating the intended endpoints
Mobile OS Security
ENISA’s report concluded that mobile OS providers should regularly update and fix security issues for devices that use mobile payments. They should also provide mechanisms for storing confidential information in a secure manner.
The agency also said that vendors shouldn’t allow jailbroken or rooted devices to use mobile payments because they are too vulnerable. Google and Samsung have drawn some criticism over this policy, but it seems necessary to ensure malware can’t access sensitive information through root privileges.
ENISA’s role in the European Union is to cooperate with national governments and organizations to ensure that critical infrastructure and services, such as financial services, are well protected against cyber attacks. Its paper aims to offer a set of guidelines for mobile payments providers, as well as users of these services and the merchants that allow them in their stores.
If companies don’t take security seriously for these services, then mobile payment adoption could suffer. The economic gains that we could see from making payments easier for the European Union, as well as other nations, could vanish.
Lucian Armasu is a Contributing Writer for Tom's Hardware US. He covers software news and the issues surrounding privacy and security.
-
wifiburger hum... yeah mobile payments with your phone that way the phone developers get a piece of the pie from mastercard / visa,Reply
well why would I complicate my life and put effort into mobile payments when I can just take out my plastic cards that are already in my wallet and require 0 setup