Windows 7 Can Be Hacked, No Fix
Earlier today at the Hack In The box Security Conference, security researchers showed how easy it is to hack into Windows 7. Ouch.
The question to ask first is this: can't every piece of software be hacked in some fashion? Quite frankly, yes. However, Microsoft (unfortunately) deals with hackers on a daily basis, patching security holes in the Windows operating system, Internet Explorer, and various programs in the Office suite. In some ways, hackers bring job stability to those who specialize in thwarting security intrusions, those who fill holes where perpetrators like to sneak in. But what if the problem can't be fixed? What if the window is wide open and there's not one thing Microsoft or any other company can do to shut it closed?
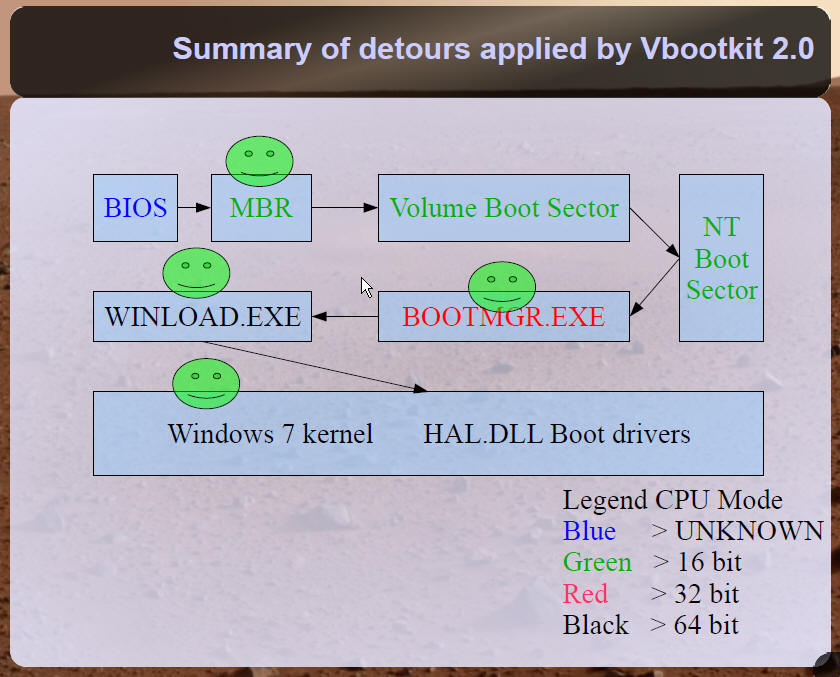
Earlier today, researchers Vipin Kumar and Nitin Kumar of NVlabs demonstrated how they could take control of a Windows 7 virtual machine using proof-of-concept code they developed called Vbootkit 2.0. The 3 KB program allows the "attacker" to take control of the computer by making changes to the operating system's files loading into the system memory during the boot process. According to Kumar and Kumar, Windows 7 cannot detect the malicious program because no files are changed on the hard disk.
"Basically, we follow a very simple algorithm for Vbootkit," the team explained during the demonstration, "Hook INT 13 for disk reads, keep patching files as they load, hook onto the next stage, and repeat the above process [until] we reach the kernel, then sit and watch the system carefully."
With that said, there's a positive and negative side to this kind of attack. The good news is that the hacker must by physically present to take control of the PC, making the threat somewhat minimal. Additionally, once the computer reboots, Vbootkit 2.0 will no longer have control since the data stored in memory is no longer available. The negative aspect is that, according to Vipin Kumar, the problem stems from Windows 7's assumption that the boot process is immune from attacks. He said that not only is there no current fix for the problem, but that it cannot ever be fixed.
The security researchers demonstrated the ability to take control of Windows 7 at the Hack in The Box Security Conference held in Dubai. The duo merely wanted to demonstrate how they could get Windows 7 (x64) running normally after implementing changes to the kernel. The demonstration was also meant to show how Vbootkit 2.0 could pass through all of the security features implemented in the kernel without being detected, and without leaving a footprint on the hard drive.
In addition to hacking into the kernel, Vbootkit 2.0 allows the attacker to control the victim's computer by remote after this initial physical invasion. The attacker can then increase the user privileges to the highest level, and remove the current user's password, allowing the attacker to gain access to all files stored on the PC. Once finished, the attacker can use Vbootkit 2.0 to restore the original password, and exit the system undetected.
So what does this mean for Windows 7? Can the problem be fixed? According to Kumar, no. However, perhaps Microsoft will take notice and figure out a workaround before the operating system eventually ships this year.
Get Tom's Hardware's best news and in-depth reviews, straight to your inbox.

Kevin Parrish has over a decade of experience as a writer, editor, and product tester. His work focused on computer hardware, networking equipment, smartphones, tablets, gaming consoles, and other internet-connected devices. His work has appeared in Tom's Hardware, Tom's Guide, Maximum PC, Digital Trends, Android Authority, How-To Geek, Lifewire, and others.
-
SuckRaven ReplyThe good news is that the hacker must by physically present to take control of the PC
That's not really good news, but at this point an intruder may as well just take the HDD and go... -
scryer_360 Considering (as was stated) that the hacker has to be present to make it work, I have no worries. Its remotely taking control that worries people, but if the hacker can physically plug in a flash drive or external drive to load his code before loading the OS, then we're all right.Reply
Seriously, it doesn't matter what security you have on your computer (or on a safe, for that matter). If the person looking to steal from you has in his/her possession the computer, he can get the data he wants anyway. I'd even suggest an easier method: take the hard drive out of the computer you want to hack and manually pull the data. There will be a password on it, but there are free password removal programs for that, even ones that run in portable executible mode. -
1raflo That wont happen if everybody uses Linux as main OS beacause the security features of...Reply
*Gets shot in the head* -
If they are taking over the VM hypervisor (or whatever you want to call it), it seems like this type of exploit is really applicable to any OS. It is a kind of "man in the middle" attach. If the OS accesses a resource, whether it is to talk to a disk controller, or make a packet request over the network hardware, and some agent can, at the lowest level, subvert the request and concoct a false response, there isn't a lot the OS can do.Reply
-
Hanin33 ppl that believe this hack is not as big as it is forget the frequency and prevalence of infected USB flash drives being passed around. this issue is not as benign as some would believe.Reply -
WinXP can be hacked within one minute (for a login password lower than 8 char.). Win Vista is more safe, but technically can be hacked in 15 minutes, and requires a secondary pc with lots of RAM.Reply
There's a reason MS discontinued support for Win 3.1 or 3.11 only recently.
Reason being for the longest time the military used win 3.x just because it's way more safe, and smaller. Sure you can't see flashfiles or play modern games on those old operating systems, but nearly nothing went automatic.
The reason why Windows is so hackable, is because there are so many programs running everywhere in the background. And the more that are running, the slower the OS, the less secure the OS gets.
I think a lot of IT professionals would want an OS that is less commercial, less nice looking, and much safer, by just not having these automatic soft or hardware recognition commands.
In WinXP I had to disable nearly half of the system services, to get it working fast. Most of them I don't need anyways! -
stradric I don't understand how this hack only applies to Windows 7... It seems like you could easily hack any OS if you had physical access to it and the right code.Reply -
kyeana please. If someone physically has access to your computer, they can fairly easily gain access to it regardless. This way may be faster, but im really not worried about itReply