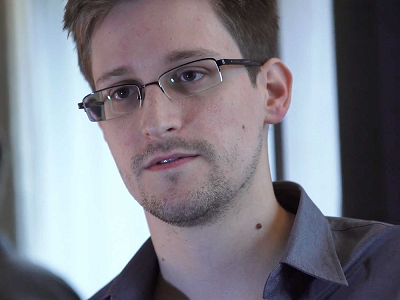
These Are Edward Snowden's Favorite Security Tools (That Anyone Can Use)
In a recent interview, Edward Snowden unveiled his top five security tools that he uses all the time to protect his communications and devices against surveillance and hacking. These include the Tor anonymizing network, the Signal private messenger, Off-The-Record (OTR) encryption protocol, TAILS, the portable anonymity-focused operating system, and Qubes OS, the operating system that offers security through compartmentalization.
Tor
Tor is an anonymizing network that can provide different IP addresses from around the world to anyone who wants to hide their location. The difference between Tor and a VPN is that Tor is more like a "chain VPN," because your data travels encrypted through multiple nodes situated in different locations of the world, making it difficult for most people, companies, or even countries to track you.
Although it's not an anonymity magic-bullet or immune to state-level targeting, Tor is by far the most privacy-friendly tool out there that anyone who doesn't like tracking can use, from regular people looking to escape the tracking of advertisers to journalists who want to hide their research or sources from the state.
In one of the leaked Snowden documents, the NSA classified Tor as "the king of high-secure, low-latency Internet anonymity" with "no contenders to the throne in waiting." As such, there's no surprise that this would be Edward Snowden's favorite tool to use to protect his privacy.
At its core, Tor is just a network, but multiple types of products have been built on top of it, including a browser, which is a fork of Firefox ESR with a few plugins meant to enhance security and privacy such as NoScript and HTTPS Everywhere.
There is also SecureDrop, which is another Tor-based tool first created by Aaron Swartz and Kevin Poulsen under the name DeadDrop to help whistleblowers and media entities communicate with each other securely. Organizations such as New Yorker, ProPublica, The Intercept, The Guardian and Washington Post use it.
One of the developers from The Intercept also created OnionShare, a Tor-based tool meant to facilitate anonymous sharing of files of any size.
Get Tom's Hardware's best news and in-depth reviews, straight to your inbox.
Recently, the Tor Project announced the Tor Messenger as well, which hides the location of those communicating and encrypts the data end-to-end using OTR.
Signal
Signal, which launched originally as TextSecure and RedPhone on the Android platform and then came to iOS, and more recently Android as well, is Snowden's and other security experts' end-to-end encrypted messenger of choice.
Thanks to its default end-to-end encryption, ease of use, asynchronous capabilities (which allows for messages to be sent even after the recipient goes offline), group end-to-end encryption, encrypted call support, and a well-respected team of cryptographers behind it, many believe it's the state-of-the-art in private communications right now.
Its text encryption protocol has already been adopted by Silent Circle in its Silent Phone app, and Whatsapp (although Whatsapp doesn't let users verify each other cryptographically, which means the encryption could be easily removed either by Whatsapp itself or a man-in-the-middle attack, without the users knowing about it).
Signal is also open source, unlike Silent Phone and Whatsapp, which makes it harder for potential backdoors to hide in the code. The app currently exists only on Android and iOS, but a Chrome extension will come soon, too.
OTR
Off-The-Record (OTR), not to be confused with Google Hangouts' own "Off The Record," which has nothing to do with the encryption mechanism employed by OTR here, and may or may not keep remnants of people's communications on Google's servers, has been the end-to-end encryption protocol of choice for the past decade, before Signal arrived.
OTR is one of the encryption protocols that also poses major problems to the NSA and law enforcement because they can't crack it, according to some leaked documents unveiled last year by Jacob Appelbaum from the Tor Project.
It was designed to be a more modular protocol that can be integrated as a plugin into many different instant messengers, both on desktop and mobile. Although this gives OTR great flexibility, in practice it also means that it could be supported by messengers that besides using OTR, have otherwise weak security and are vulnerable to attacks.
In other words, not all OTR clients are created equal, and if you use an IM that uses OTR, then you should pick one that's also serious about security in general. Apps that can use Tor include ChatSecure on mobile and Tor Messenger on the desktop.
TAILS
The Amnesic Incognito Live System (TAILS) is an OS built entirely around the idea of sending and receiving all the Internet traffic through the Tor network. It's designed to be portable, so you can boot it from a DVD, USB drive or an SD card.
The DVD option can also be used to enhance the security of the system, because no malware can persist inside the OS. Worse case scenario, the malware will reside in RAM until you reboot. However, this option also has a disadvantage. Bugs are often found in TAILS, just like in any other operating system. When that happens, you have to update the OS, unless you want to remain vulnerable to those bugs. That means you have to write a new DVD with the latest version every time.
That's why TAILS is suitable in more extreme situations where using it is more of a one-off thing, rather than it being your main operating system. For instance, it would be a good choice for a whistleblower looking to expose wrongdoing and send documents to the media.
Qubes OS
For those who want a highly secure operating system that they can use everyday that also comes with an option to "Torify" all traffic, there's Qubes OS. This OS can create secure virtual machines on the fly for work, banking, personal activities, or disposable VMs that you only use one time to open a risky file, and then completely wipe them from your system.
Qubes OS also comes with a Whonix template, which can be used as a Torified virtual machine that you can use whenever you want to hide your activities from tracking. You can also delete that VM and start a new one to give you much of the security you would get from using TAILS on a DVD. However, the advantage of Qubes OS is that you can also use it for more normal activities, while still protecting yourself against the daily dangers of malware infections.
These are the software tools that Edward Snowden, a former NSA contractor, and now a whistleblower on the run, uses. The best part is they are all tools anyone can use, too, to protect their daily privacy and security against all sorts of bad actors.
______________________________________________________________________
Lucian Armasu joined Tom’s Hardware in early 2014. He writes news stories on mobile, chipsets, security, privacy, and anything else that might be of interest to him from the technology world. Outside of Tom’s Hardware, he dreams of becoming an entrepreneur.
You can follow him at @lucian_armasu. Follow us on Facebook, Google+, RSS, Twitter and YouTube.
Lucian Armasu is a Contributing Writer for Tom's Hardware US. He covers software news and the issues surrounding privacy and security.
-
Spiderman1 Strange to choose signal, it is backed by a US government fund and is purported to have backdoors - I wouldn't use it.Reply -
septentriones Remember that when using an OS like Tails it is not safe against compromised hardware so you can't just pop it into any machine and assume you're safe. Use only hardware you trust.Reply -
Optimus_Toaster I fully understand that people don't want anyone to be able to see what they are doing. And stuff like this is great for them. You want more privacy - more power to you.Reply
But for me, I really don't care. I don't care that microsoft know that I use a mouse and keyboard and have steam running 24/7. I don't care that google knows I want directions to the train station and how to spell noticably. I don't care that the government knows that I watching youtube and twitch. -
fimbulvinter ReplyI fully understand that people don't want anyone to be able to see what they are doing. And stuff like this is great for them. You want more privacy - more power to you.
But for me, I really don't care. I don't care that microsoft know that I use a mouse and keyboard and have steam running 24/7. I don't care that google knows I want directions to the train station and how to spell noticably. I don't care that the government knows that I watching youtube and twitch.
I don't care that you don't care. -
dark_lord69 Yeah, I wouldn't use any of these...Reply
Why, because I don't give a sh*t what the government knows about me or the things I do. I'm not a person of interest for them. -
house70 Reply16918971 said:Yeah, I wouldn't use any of these...
Why, because I don't give a sh*t what the government knows about me or the things I do. I'm not a person of interest for them.
I am not advocating for anyone to start using these tools just because they read about them. However, your "not a person of interest status" may change at a whim, possibly because of name coincidence or some clerk inputting the wrong number/name in a database. There are quite a few people on the "no fly list" for instance that were added by mistake and had a time trying to clear their names up. Just FYI. -
allawash I posed a question the other day about the app markets and downloading Signal, what if the version uploaded to those app stores was swapped out with a "fixed" version to allow back doors? How would the average person be able to verify the open source version they viewed on the net was the same version they downloaded from Apple or Google?Reply -
milk_inc ReplyI fully understand that people don't want anyone to be able to see what they are doing. And stuff like this is great for them. You want more privacy - more power to you.
But for me, I really don't care. I don't care that microsoft know that I use a mouse and keyboard and have steam running 24/7. I don't care that google knows I want directions to the train station and how to spell noticably. I don't care that the government knows that I watching youtube and twitch.
You name everything goverment need about you, if you have steam that mean your credit card as microsoft already have it, they know where you live as which place you frequently go, a lot of information you already give to them access, now imagine someone hack the server of microsoft with all this info include it yourself, who know what the hacker can do with all you info can modify all the things you do or even so, those all info is owned by another person this mean can make steal of identity make crime as like it, because they had access to your info, id card, credit card, what places you visit practically anyone, what you like what you dislike, can use your identity and you lost it. Even is not you, but of course you believe privacy is not important of course it's, remember part of what identify you is your privacy, as not relevant you think the stuff you do, those things make your identity and define as person. -
hr_sto It's unfathomable the ridiculous overreaction to the Prism program. Only more incredible to this is the glorification of this clown of a traitor, who actually helped directly terrorists and just about any other criminal organizations that rely on IT for their operations. People that deal with stuff like human/drug/arms/... trafficking.Reply
After Edward, all the aforementioned scumbags will know how to better hide themselves. Victims of this modern hero will be the average citizen who will fall pray to whatever BS the sick minded are cooking right now.
Don't get me wrong, i'm not justifying blindly everything governments do. Nor do i hate whistleblowers. In fact, i think wikileaks is awesome, as it revealed lots of interesting info like reports about foreign political crooks from various embassies, which is or public interest to the citizens of those countries, and so many more...
But... try and rationalize what Edward did.