Convicted Hacker Mitnick Educates Navy on Cyber Security
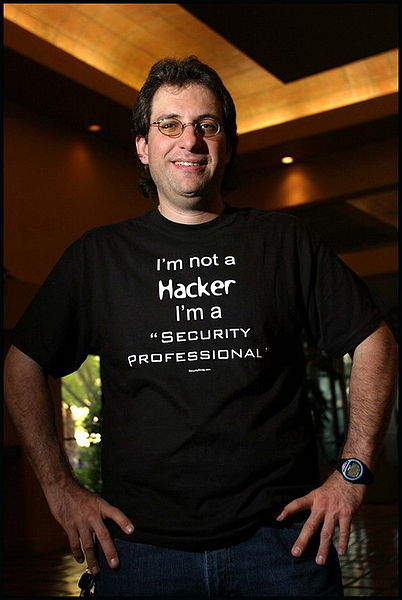
Kevin Mitnick has long been viewed as synonymous with computer hacking.
Released from prison in 2000, he served five years in prison for hacking into DEC, Fujitsu, Motorola, NEC, Nokia, and Sun. These days, Mitnick runs a security consultancy firm and was recently hired by the US government.
The Naval Academy said that Mitnick demonstrated that the military's computer security gates can be easily penetrated (even on fully patched systems), that malicious software can pass anti-malware protection systems, and that military personnel could benefit from extra computer security training. In his speech, he suggested that computer training should be taken just as seriously as other training. The conclusion of the Naval Institute?
"All hope is not lost. There’s plenty that can be done to preserve military networks and defend against data leakage both from the outside and from the inside. The weakest part of any computer security strategy is always the user, and we should be putting more emphasis on doing everything we can to strengthen it."
Mitnick's post-prison career path resembles the early stages of Kim Dotcom's - known as Kim Schmitz back then - post-hacking career. Schmitz hacked NASA, Citibank, and the Pentagon using the name Kimble. Following these activities, he began consulting with Germany's DeTeMobil cellular provider and founded a security consulting firm, Data Protect, which he sold before the company went bankrupt in 2001.
Given the fact that the U.S. government once considered Mitnick capable of starting a nuclear war "by whistling into a pay phone," it is interesting to see that it is now listening to his security advice.
Contact Us for News Tips, Corrections and Feedback
Get Tom's Hardware's best news and in-depth reviews, straight to your inbox.

Wolfgang Gruener is an experienced professional in digital strategy and content, specializing in web strategy, content architecture, user experience, and applying AI in content operations within the insurtech industry. His previous roles include Director, Digital Strategy and Content Experience at American Eagle, Managing Editor at TG Daily, and contributing to publications like Tom's Guide and Tom's Hardware.
-
overclockingrocks How ironic. They chased him for years because of a lot of stuff attributed to him that he never actually did and as the article pointed out they were pissing their pants scared of him and his supposed ability to whistle nuclear launch codes into a payphone and launch the nukes at NORAD. Just hilarious to me that they are not only listening to his security advice and good advice it is but have hired him and are paying him for it!Reply -
frombehind that's the US government for ya bro...Reply
They payed me $30k a year when I was in the military to work my ass off 12hours a day, 7 days a week...
Now I have THE EXACT SAME job as a civilian contractor for over 250k a year, and all I do is show up and play video-games for 8 hours a day =) -
juvx frombehindthat's the US government for ya bro...They payed me $30k a year when I was in the military to work my ass off 12hours a day, 7 days a week...Now I have THE EXACT SAME job as a civilian contractor for over 250k a year, and all I do is show up and play video-games for 8 hours a day =)Reply
Your job sounds awesome !
Good for Mitnick. China has whole divisions of cyber hackers.... we need a lot more. -
jhansonxi Navy could use some education:Reply
http://gcn.com/articles/1998/07/13/software-glitches-leave-navy-smart-ship-dead-in-the-water.aspx
http://en.wikipedia.org/wiki/Submarine_Command_System -
igot1forya The chants over the years...Reply
(1) Early 2000's - "Hack the planet! Hack the planet!"
(2) Mid 2000's - "Free Kevin! Free Kevin"
(3) 2012 - "Hire Kevin! Hire Kevin!"
The kids are growing up so fast! -
mikemp3 How the worm turns. Similar to how we sold Sadam the weapons then we bombed him now we are wiping our hands of that mess.Reply -
alidan overclockingrocksHow ironic. They chased him for years because of a lot of stuff attributed to him that he never actually did and as the article pointed out they were pissing their pants scared of him and his supposed ability to whistle nuclear launch codes into a payphone and launch the nukes at NORAD. Just hilarious to me that they are not only listening to his security advice and good advice it is but have hired him and are paying him for it!Reply
um yea... rememer us... the reason you went to jail for so long... much of it lies... and fear... we kind of made up... we really appreciate that you didnt sue the crap out of us... lets make this up to you.