'KRACK' Wi-Fi WPA2 Vulnerability Compromises Encrypted Connections
Get Tom's Hardware's best news and in-depth reviews, straight to your inbox.
You are now subscribed
Your newsletter sign-up was successful
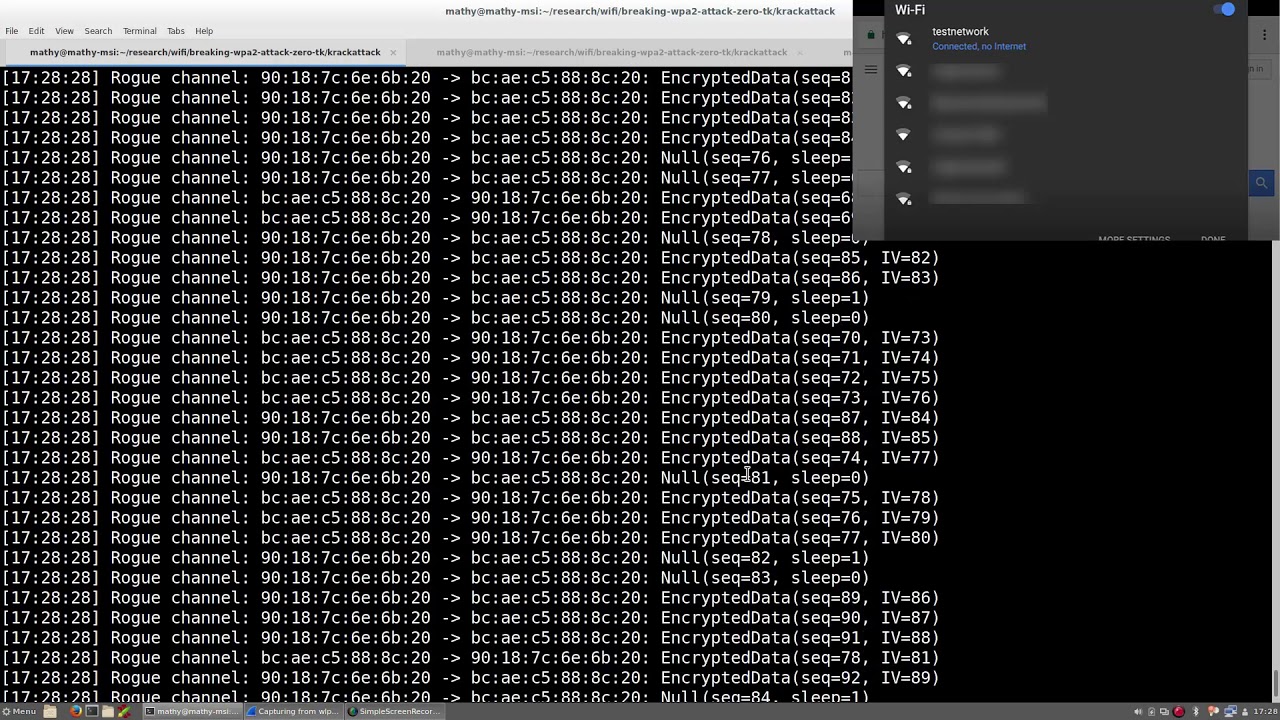
Researcher Mathy Vanhoef of KU Leuven, Belgium’s highest-ranked university, uncovered a vulnerability in the WPA2 encryption standard of the Wi-Fi protocol that affects virtually all Wi-Fi devices.
Attackers can use key reinstallation attacks (KRACKs) when in range of someone connecting to a Wi-Fi router to re-install or reset to zero their encryption keys, thus allowing them to read information that was assumed to be encrypted.
Weakness In The Wi-Fi WPA2 Standard
The vulnerability is in the Wi-Fi WPA2 standard itself, not in the implementations of the protocol, which means that even if it's correctly implemented devices are still vulnerable to attacks. In the researcher’s own tests, he found that Android, Linux, Apple, Windows, OpenBSD, MediaTek, Linksys, and other platforms were all affected by some variant of the attacks.
Article continues belowVanhoef was able to decrypt a large number of packets when testing across the platforms mentioned, but the traffic of Android 6+ and Linux devices was even easier to decrypt than the other platforms. That's because these devices’ WPA2 keys could be reset to zero, so in essence all traffic could then be decrypted.
Technical Details
The researcher executed the attack against the four-way handshake of the WPA2 protocol. The handshake happens when a client wants to join a protected Wi-Fi network. It is used to confirm that both the client and the access point posses the correct credentials (the network's password). A fresh encryption key to protect the traffic is also negotiated at the same time.
Via this form of attack, an adversary tricks the victim into re-installing an already-in-use encryption key. When the victim re-installs the encryption key, the incremental transmit packet number (i.e. nonce) and receive packet number (i.e. replay counter) are reset to their initial value. However, to guarantee security, a key should only be used once. This is not guaranteed by the WPA2 protocol.
Vanhoef noted that when the victim uses the WPA-TKIP or GCMP encryption protocol, the results of the attack can be more catastrophic, because the attackers can not only decrypt the traffic, but they can also inject malicious packets such as ransomware or some other malware. The GCMP protocol is being used by the WiGig wireless protocol, which should see an increased adoption in devices over the coming years.
Get Tom's Hardware's best news and in-depth reviews, straight to your inbox.
Even if the content is encrypted with HTTPS, too, the attacker could still decrypt it via a man-in-the-middle attack that downgrades the connection to HTTP. To avoid this, the website would also need to support the HSTS protocol, so that the HTTPS connection is enforced by the browser itself, rather than the server. Then the browser would not accept any non-HTTPS connection to the site.
Android 6+ And Linux
Attacks against Android 6+ and Linux are more catastrophic because these platforms eliminate the key from memory once it has been installed the first time. This is supposed to be a security measure against attackers trying to steal the encryption key from memory.
However, this also means that when the attacker uses KRACK to re-install the encryption key, an all-zero key is installed. Having a known all-zero key used for encryption means the attacker can decrypt all traffic. According to the researcher, 41% of existing Android devices are impacted by this more devastating variant of KRACK.
Vanhoef's paper was first sent to the platform vendors in May 2017, but he said that since then he has found improved versions of the attack that can more easily decrypt connections of macOS and OpenBSD systems.
The researcher has only now made the paper public, as he has been waiting for the vendors to prepare patches for their platforms. Vanhoef mentioned that we shouldn’t need a WPA3 protocol to fix this vulnerability, because implementation fixes will suffice. What the patches will do is ensure that a key can only be installed once.
Changing the Wi-Fi password alone will not help to avoid this type of attack. Instead, Vanhoef recommended that users update the firmware containing the patches against KRACK on all of their devices and routers. Changing the Wi-Fi password afterwards can be done optionally as an extra precaution.
Lucian Armasu is a Contributing Writer for Tom's Hardware US. He covers software news and the issues surrounding privacy and security.
-
Rob1C How is this 'better' than Fluxion (or other methods)?Reply
Both are quick, this resets your password to a know value on the client and allows MitM whereas Fluxion obtains the Router's password which you can reuse to reconnect in the future (assuming it's not changed often).
Thanks.