How to Get Persistent SSH Connections in Linux Using Eternal Terminal
You won’t need to manually reconnect, even if an IP address changes.
An SSH connection is typically used to connect with remote machines. It works on a client /
server model, in that the machine being used to connect to a remote machine is called a client, while the latter is the server. To establish the connection with the remote machine, you must know its IP address, as well as the username/password to authenticate the connection.
Because the connection is based on IP address, any change in the IP address automatically breaks the SSH connection, turning even mild-mannered users into rage monsters.
Article continues belowReleased under Apache license, Eternal Terminal can be used as a replacement for SSH. Its claim to fame is the ability to re-establish connection to a remote machine without user intervention. This is in sharp contrast to SSH connections, which once terminated have to be re-established manually.
Eternal Terminal relies on SSH to connect and authenticate with the remote machine. So you must have SSH installed and running to be able to connect the different machines with Eternal Terminal.
How to Install Eternal Terminal
The easiest way to install Eternal Terminal is with the Homebrew package manager. If you don’t already have it installed, you can do so with a single command:
bin/bash -c “$(curl -fsSL https://raw.githubusercontent.com/Homebrew/install/master/install.sh)”This command first downloads the install.sh script, and then executes it. Once the installation is complete, follow the instructions on the screen to add brew to your $PATH.
Get Tom's Hardware's best news and in-depth reviews, straight to your inbox.
With all that done, you can now use Homebrew to easily install Eternal Terminal with the brew install MisterTea/et/et command. Because Eternal Terminal operates on the client/server principle, just like SSH you’ll also have to install it on the remote machine you
wish to connect with as well.
If you’re put off by the idea of having to use yet another package manager, fret not! Ubuntu users can install Eternal Terminal from a PPA while Arch and Fedora users can use the software repositories to install it.
Apart from instructions on installing it on these distributions, you’ll also find directions to install Eternal Terminal on Debian and openSUSE as well as building it from source on the project’s website.
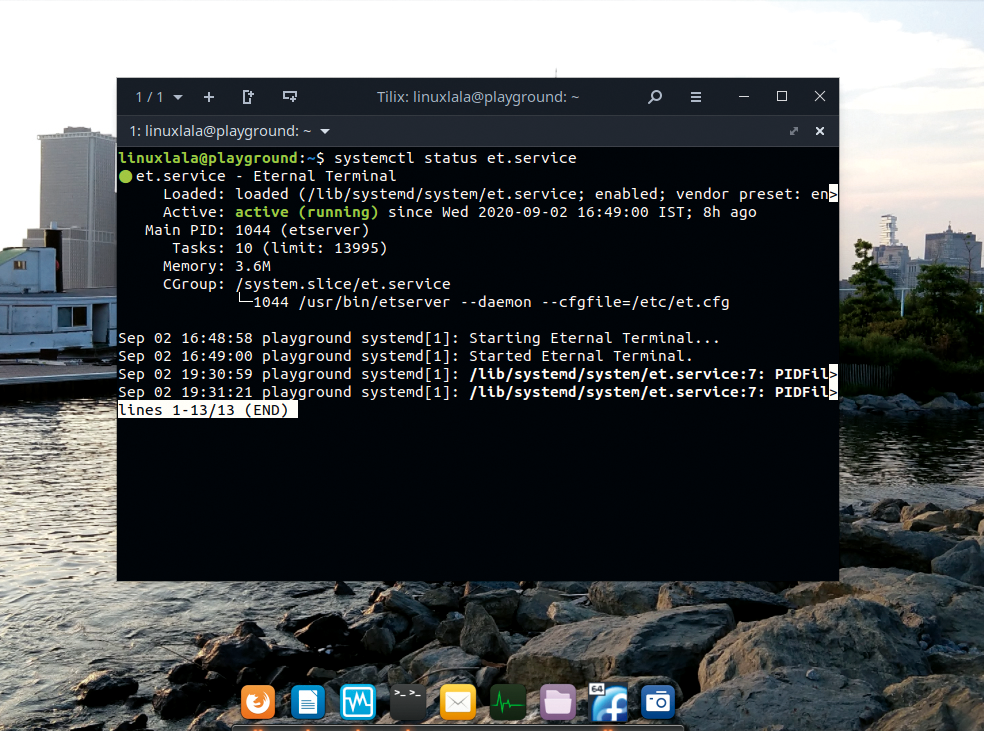
On the server machine – that is, the remote host you wish to connect with – ensure that the Eternal Terminal service is active. Depending on your distro, you might have to run sudo systemctl enable --now et to activate the Eternal Terminal service on the remote machine.
How to Connect with Eternal Terminal
Once this is done, you can connect to the remote machine in much the same way as you would using ssh.
The syntax of the command is: et username@<ip address>:{port] . By default, Eternal Terminal uses port 2022. The essential configuration, such as the port number, for Eternal Terminal are stored in the /etc/et.cfg file. See the section below on connection errors if you can’t connect to the remote machine and receive a Could not reach the ET server: <ip address>:[port] error.
When connecting to a remote machine, you only need to provide the port number if you’ve changed the configuration and opted to use a different port number than the default. Additionally, if no username is provided, the tool uses the current username on the host machine to connect with the remote machine:
Eternal Terminal uses SSH for handshaking and encryption, and if you’ve ever used ssh to connect to a remote machine, the output generated by the et command would seem familiar.
When you first connect to a remote machine with Eternal Terminal, the host machine gets a ECDSA key fingerprint. You’ll be asked to confirm if you wish to continue connecting to this remote machine. If you answer ‘yes’, this key is stored in the ~/.ssh/known_hosts file.
When connecting to a remote machine, Eternal Terminal consults this file as a way of identifying the remote machine. The key is also used to encrypt the data transmitted between the machines. You won’t be prompted to confirm the identity of the remote machine if its key is stored in the ~/.ssh/known_hosts file.
To check the ssh key on the remote machine, you must run the ssh-keygen command:
ssh-keygen -l -f /etc/ssh/ssh_host_ecdsa_key.pub
256 SHA256:ovbASZs2/xb44fCzxiegocpF3ZYDL/
g3Agtmefh3G6k root@playground (ECDSA)As you can see, this key is a match for the key fingerprint as provided by Eternal Terminal when trying to establish the connection with the remote host.
You can terminate the connection to the remote machine by typing exit or pressing Ctrl+D. This is yet another overlap in functioning between Eternal Terminal and SSH, but that’s to be accepted since we’ve already mentioned that Eternal Terminal relies on SSH to establish connection to remote machines.
Apart for the change in the bash prompt, Eternal Terminal itself doesn’t produce any output or otherwise inform you when it successfully establishes connection with a remote machine. It similarly doesn’t provide any information about poor connections, or even when the
connection is lost entirely, such as when the remote machine is disconnected or powered off.
As long as you’re connected to the remote machine, Eternal Terminal produces instantaneous results for all commands and operations you execute. However, if the connection is lost, such as when the remote machine’s IP address is changed or if the remote machine is hibernated, then whatever you type on the screen is no longer shown in the terminal. In fact, the terminal will appear to be non-responsive. However, Eternal Terminal remembers all the keystrokes made during this period, and executes them in order once the connection is re-established.
The project achieves this feat by implementing a special layer between the application and TCP layer. The ability to reconnect automatically only works if the connection is terminated at the remote machine.
If you restart the host machine while connected to the remote machine, the Eternal Terminal session isn’t killed automatically. Instead, such Eternal Terminal sessions are referred to as orphans, and there’s no way for you to connect with such orphan sessions. Your only recourse is to establish a new connection with the remote machine. When you make a new connection, the orphaned connections aren’t terminated automatically and will persist until you manually kill them. You can do so by using the -x command option:
et -x linuxlala@192.168.0.9
This command kills all orphaned sessions and establishes a new connection with the remote machine.
Eternal Terminal is often compared with alternatives such as Mosh. While the latter also boasts of the autoreconnect feature, Eternal Terminal additionally supports scrolling, which means that you’ll be able to go back and forth and review the generated output on the terminal screen.
How to Solve “Could Not Reach ET Server” Error
Depending on the distribution running on your remote machine, you might not be able to create an Eternal Terminal session when you first run the et command.
If you encounter a Could not reach the ET server: <ip address>:[port] error, this means that the remote machine doesn’t allow incoming connection on the specified port.
You can either change the configuration to use a port, which is open for use, or alternatively open a port for Eternal Terminal. How you do this will depend on the distribution and the firewall utility. For instance, Fedora users can open a port with the sudo firewall-cmd addport=2022/tcp command. You can list all open ports with the sudo firewall-cmd --list-ports command.
If you’re using UFW however, such as on Ubuntu, you’ll have to run the sudo ufw allow <port number> command to open the specified port. You can then run the sudo ufw status verbose command to confirm that the specified port is now open.
Should you encounter any other problems with Eternal Terminal, you’ll likely find answers in the issues section of its GitHub page. It’s a popular project and many common issues, such as lack of colours in the output of ls command and X11 forwarding workaround have already been addressed and closed by the developer.
This article originally appeared in the November 2020 issue of Linux Format Magazine.

Shashank Sharma is a freelance writer for Tom’s Hardware US, where he writes about his triumphs and joys of working with the Linux CLI.
-
w_barath You're on the go, on mobile data, or WIFI, or even just want the freedom to let your device suspend to save battery life:Reply
On the remote:
$ sudo apt install screen || sudo yum install screen
On your roving mobile terminal:
$ sudo atp install autossh || sudo yum install autossh
Then
$ autossh -C host -t 'screen -xRR'
This will automatically re-attach a disconnected shell session, leaving you exactly where you were, without HUPping the command you were running. This is great for when you're running system updates, or compiling, or anything else that requires a long connection.
Personally I use it to shell into a cloud host, which I then have shells to all my other servers combined into a single screen session so I can hop between machines with CTRL-A #, and I set the window names to reflect the hosts.
For another trick - if you want to be able to shell into your laptop and you don't know what it's IP is, set up a TOR hidden SSH service on it. That will allow you to connect no matter what your IP is. It also makes it possible to ssh between two hosts where neither of them know the other's IP. There will be some latency, but you can always connect directly after you've established what the IPs are. Also very handy if your laptop is stolen since your autossh will connect as soon as they connect to the internet, and you can shred your disks or use x11vnc, your laptop's microphone and camera to spy on their activities, get their public IP, and send the cops their way. -
Jbar_ You may look also at autossh, which do the same job, since very long time.Reply
https://linux.die.net/man/1/autossh -
Jbar_ Replyw_barath said:For another trick - if you want to be able to shell into your laptop and you don't know what it's IP is, set up a TOR hidden SSH service on it.
More simple, if you have an ssh access to a machine always connected and reachable from Internet : ask autossh to start and monitor a reverse ssh tunnel.
(I let you search the command line to do so). -
w_barath ReplyJbar_ said:More simple, if you have an ssh access to a machine always connected and reachable from Internet : ask autossh to start and monitor a reverse ssh tunnel.
Not everyone has an ssh box with a static public IP to push reverse connections through.
To add SSH as a TOR hidden service to your linux box is trivial:
$ sudo apt install tor && sudo systemctl enable tor.service && sudo systemctl start tor.service
$ sudo nano /etc/tor/torrc # ucomment the sample hidden service and SSH port (22) line
$ sudo service tor restart
$ sudo su -c 'cat /var/lib/tor/*/hostname' # to see the newly generated hidden service domain name
$ sudo apt install netcat
then add this to your ~/.ssh/config:
Host *.onion
VerifyHostKeyDNS no
ProxyCommand nc -x localhost:9050 -X 5 %h %p
After that you can ssh to the generated tor address like any other domain name.
Alternatively, on a client machine all you need is to install netcat and TorBrowser and add this line to your ~/.ssh/config:
Host *.onion
VerifyHostKeyDNS no
ProxyCommand nc -x localhost:9150 -X 5 %h %p
That will use the tor client which TorBrowser installs, which will work in countries and with hotspots which block tor. -
anscarlett Reply
I just use a spare raspberry pi and install Duckdns on itw_barath said:Not everyone has an ssh box with a static public IP to push reverse connections through.
I generally use mosh and tmux, as this provides resilience to bad connectivity issues. I have no permanent broadband connection at home, I use multiple 4g services which generally works fine, but can occasionally drop connections.