OPM Update Shows Fingerprint Databases Highly Vulnerable To Hacking
The Office of Personnel and Management, where the biggest data breach in the U.S. government's history happened, initially reported that along with the sensitive information and social security numbers of 21.5 million government employees and their relatives, 1.1 million fingerprints were stolen as well. The OPM has now discovered that the number was in fact more than five times greater: 5.6 million fingerprints were stolen.
It seems that in this case, as well as with the original report on how many employees it affected, the OPM was off by a factor of five. The OPM also said that it initially believed only the records of 4 million employees were stolen, when it was actually 21.5 million.
Senator Ben Sasse (R-Neb.) even stated that the administration is still treating the OPM case as something that needs to be as low-key as possible, as if it would be a "PR problem" for the government, rather than a big national security issue:
"Today's blatant news dump is the clearest sign yet that the administration still acts like the OPM hack is a PR crisis instead of a national security threat," said Sen. Sasse in a statement.
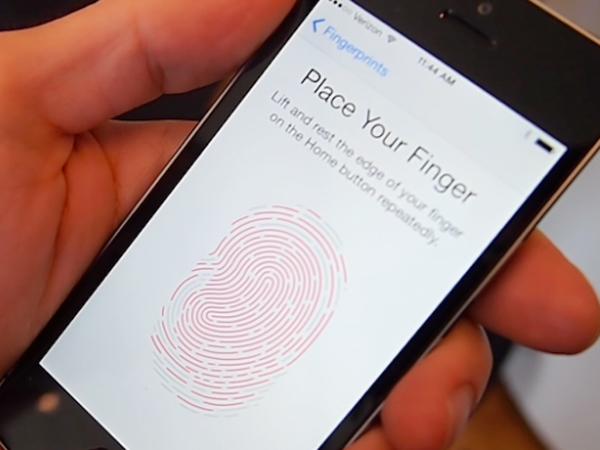
The good news now is that fingerprints aren't being used for authentication across the government, so the hackers can't use them to further penetrate other systems inside the government. The bad news is that many of those employees may already have personal phones that use fingerprint authentication, and their phones and personal data could now be at risk.
It also makes fingerprint authentication a non-starter for government IT infrastructure, at least for these 5.6 million employees, at a time when Apple, Google and Microsoft are all pushing fingerprint authentication as the de facto way to unlock your devices.
However, the government should have realized by now that fingerprints would always be a high-value target, especially in the future when more devices use it. That doesn't seem to be quite the case, though, as only recently the EFF reported that the FBI is not only ramping up its collection of fingerprints in centralized databases, but that it's also merging the civil and criminal databases together, just so its job gets a little easier. A future government hack could affect not just those working for the government, but regular people as well, whose only crime was to submit to a background check.
Get Tom's Hardware's best news and in-depth reviews, straight to your inbox.
Fingerprints should probably never be used alone to protect a device or computer, but in conjunction with a passphrase, PIN, Bluetooth unlock or a one-time password (OTP) code. Even then, it would be best to keep only a hash of the fingerprint on the local device, not the whole fingerprint image stored in someone else's servers, especially if that someone keeps millions of them in one place. That's just making the fingerprint database a highly valuable target, worth going after not just by other nations, but by criminal groups as well.
Follow us @tomshardware, on Facebook and on Google+.
Lucian Armasu is a Contributing Writer for Tom's Hardware US. He covers software news and the issues surrounding privacy and security.
-
house70 A few weeks ago I was having a back-and-forth with another commentator here about this whole debacle, where I was expressing my indignation towards the lack of professionalism and utter nonchalance of the OPM (as part of an even more nonchalant government) in dealing with this crisis, and the other party expressing a more lenient attitude, even suggesting that media reports are not always to be trusted and in this case they're likely exaggerated.Reply
This new development shows that the only thing inaccurate was the extent of the damage reported, in this case the initial report was conservative at best.
The new OPM attitude will probably be like "so what? just replace your fingers, and thank you for your taxes".