How Microsoft Intends To Go 'Passwordless' With Hello And Passport Authentication
Last month, Microsoft announced its "Hello" biometric authentication protocol along with another protocol called "Passport," for logging into apps and websites with either a PIN number or through the Hello protocol. At Build 2015, Microsoft revealed new details about its two new security features.
Most people either use very simple passwords or reuse them across different websites of various security levels, which makes their passwords very susceptible to hacking. Even though biometric authentication systems are far from being perfectly secure, they should still improve the average users' security.
Microsoft has also worked to ensure that the security standards for the Hello and Passport protocols are as high as possible.
Article continues belowHello Protocol
The Hello protocol supports three types of biometric authentication: fingerprint, face and iris. We've already seen fingerprint authentication in the mobile market, made popular by Apple. We've also seen "Face Unlock" from Google, starting with version 4.0 of Android. Now, Microsoft is introducing iris recognition as well, which could be significantly more accurate in identifying the user as well as more resistant to spoofing.
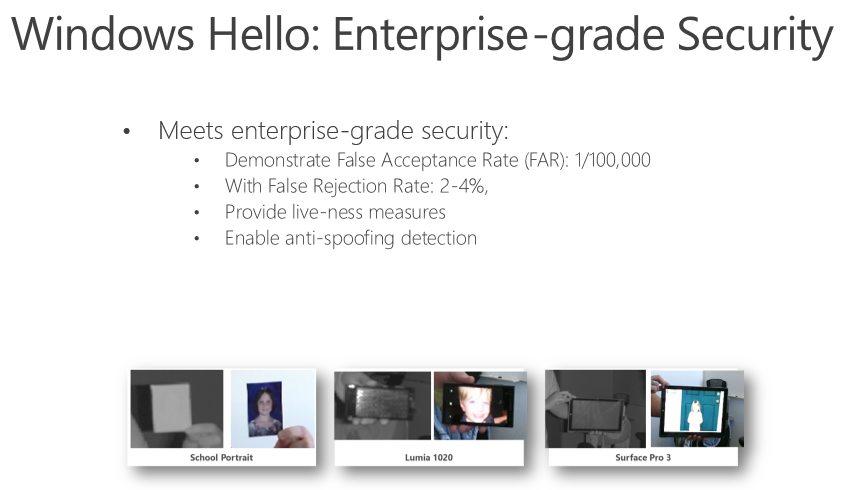
Microsoft states that Hello has "enterprise-grade security," which includes a False Acceptance Rate (FAR) of 1/100,000, a False Rejection Rate of 2-4 percent, live-ness measures (to ensure it's not just a photo being shown to the camera, but a living person) and an anti-spoofing detection system that seems to block images that are received from other devices.
There will be a "Windows Biometric Framework," which will come on all Windows 10 devices, and all current fingerprint readers will be supported. In terms of face recognition, Microsoft will support all Real Sense cameras from Intel starting with series f200 (the current series). All devices with IR sensors will be supported as well, but only if they comply with Microsoft's specification.
The iris authentication specification doesn't seem to be fleshed out yet, however, the company confirmed that the spec will be announced soon. Microsoft also confirmed that some devices that will arrive on the market in the next 12 months will support iris authentication.
Get Tom's Hardware's best news and in-depth reviews, straight to your inbox.
Passport Protocol
If Hello is the way in which you can authenticate to devices and keep them secure against third party access, Passport is how Microsoft hopes everyone will log into third party apps and websites in the future, without the need to remember long passwords to stay secure.
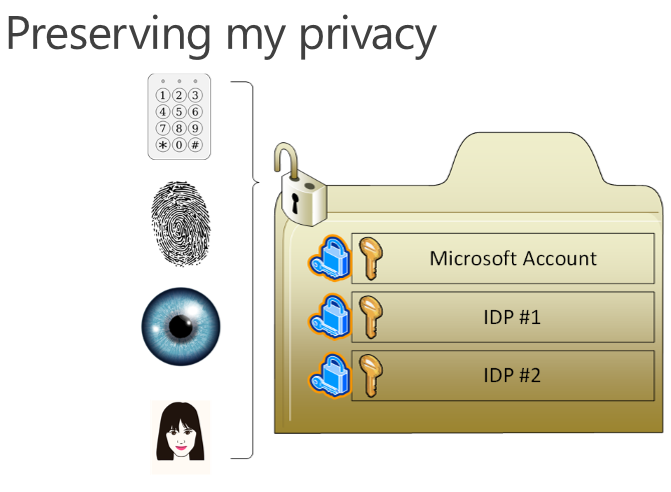
Passport can work with Hello, so for instance, you'll be able to use the locally stored fingerprint to authenticate to a website without ever transmitting the fingerprint to that third party server (which could expose your fingerprint to being stolen in a database hack).
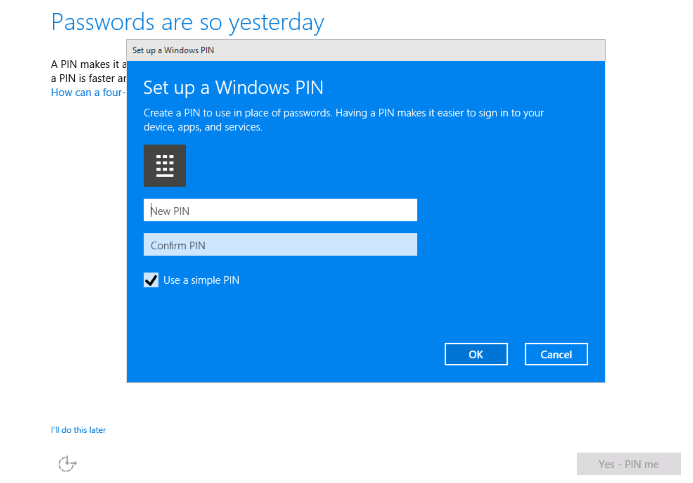
As an alternative to biometric authentication (for those who are more skeptical about it), Microsoft will also allow app and website logging through a PIN number. Microsoft claimed that a PIN is actually more secure than an average password. That's because a potential hacker would need to know the PIN and also have access to the user's device to hack into a Passport-protected account.
Microsoft noted that the PIN isn't stored on the device. The PIN will be created during Windows setup, while Hello can be configured to work with Passport in settings.
There were a few other interesting tidbits for developers as well. The native Passport API will be provided through the Universal Windows Platform, which means only apps will be able to use it initially. Also, a Javascript API for browsers will be provided later this year so websites can use it, too.
Microsoft also promised to standardize Passport under the FIDO 2.0 specification, which means other platforms including Android and even iOS (if Apple so chooses) could be implementing the Passport protocol for app and website authentication without transferring fingerprint, face or iris data to third party providers.
Both Google and Microsoft are part of the FIDO Alliance so they're likely to use it, but Apple will probably stay on its own course, as usual. However, this will create some kind of fragmentation in the "passwordless authentication" world, or at the very least, app and web services providers will have to support both the FIDO 2.0 protocol as well as Apple's own protocol, while also continuing to support passwords for people without biometric authentication devices.
Follow us @tomshardware, on Facebook and on Google+.
Lucian Armasu is a Contributing Writer for Tom's Hardware US. He covers software news and the issues surrounding privacy and security.
-
TechyInAZ This should be fine for normal users. But for people who really truly want high end encryption/security then the password is still going to be the dominant type of security. I have a hard time trusting new security programs like this until they are 90-100% proven to work well.Reply -
falchard I think there will be a move to no passwords, and use a key instead. Personally, I welcome never having to enter a password again and allowing Microsoft to manage all my passwords as some complex gibberish that it automatically enters when I use a service.Reply -
Solandri Biometric security is implicitly insecure. You can easily duplicate someone's fingerprint, face, voice (just added to Lollipop), or iris with a photo or recording. The only way to make it secure is to have another person next to the machine verifying that it's a living, breathing person whose biometrics the device is reading, not a photo or recording or some other duplicate.Reply
Also, I'm skeptical about the reliability of iris scans. I was in the government's NEXUS program (fast lane between the U.S. and Canada) back when they used iris scanners at the airport. It works well for some people, but is problematic for others. I always had to take off my glasses, use my fingers to hold both my eyes wide open, and the machine would still take 3-5 tries before it recognized me. My experience must not have been unusual because they've since gotten rid of the iris scanners and replaced them with fingerprint scanners. I've never had a problem getting recognized by those. -
loggert Once your fingerprint is hacked from some store's database you will never be secure again. Never. That is why biometrics are not secure and not used in any high stakes applications.Reply