Samsung Seemingly Falls Victim to Nvidia Attackers
Lapsus$ has released what it claims to be some proprietary Samsung code.

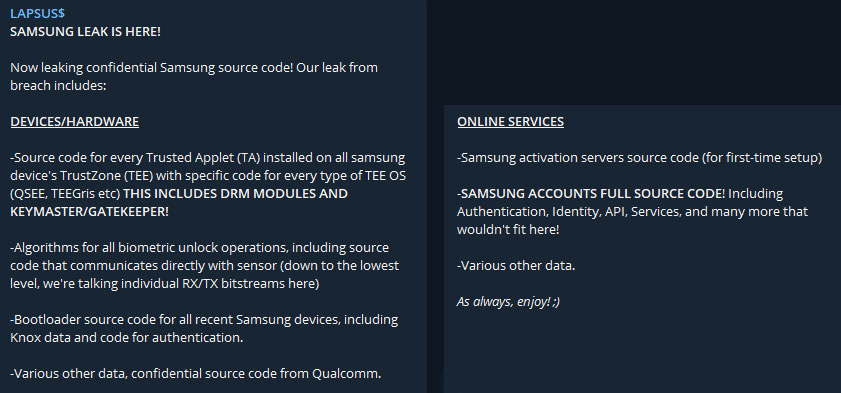
Lapsus$, a hacking extortion group that previously targetted Nvidia, has begun crowing about a significant Samsung data leak that it has architected. The hackers claimed they plundered about 200GB of compressed data from Samsung servers, including confidential documentation, code, and other proprietary information. More specifically, Lapsus$ claims to have its hands on Knox authentication code, biometric unlock algorithms, bootloader code for all recent Samsung devices, Trusted Applet source code, code behind online services and Samsung accounts, and much more.
If the claims are correct, Samsung has suffered a significant and potentially very damaging leak due to the actions of these South American hackers. From the notices published by the group, it is difficult to pinpoint the most crucial data leak, as they all sound so very central to the security of Samsung devices. One in every five smartphones sold worldwide is a Samsung Galaxy device, so Samsung won't just feel the potential fallout from this hack; it has hundreds of millions of users to consider.
In trying to determine the nature and contents of the Samsung hack, Bleeping Computer has pondered over the extortion gang's claims, shared screenshots, and a downloadable file-set containing the leaked data. The screenshot reveals some C/C++ code from Samsung software open in an editor. The contents of the leak are available via the BitTorrent protocol. About 400 peers shared the pilfered Samsung content, so this is a rather popular lump of data.
Interestingly, Bleeping Computer downloaded the small ReadMe.txt from the torrent, and it explains the contents of the trio of 7Zip archives as follows:
- Archive part 1: contains a dump of source code and related data about Security/Defense/Knox/Bootloader/TrustedApps and various other items
- Archive part 2: contains a dump of source code and related data about device security and encryption
- Archive part 3: contains various repositories from Samsung Github: mobile defense engineering, Samsung account backend, Samsung pass backend/frontend, and SES (Bixby, Smartthings, Store)
Nvidia then Samsung - who's next?
You may well know of the name Lapsus$ from our coverage of the Nvidia hack over the last week or so. Around five days ago, the online extortionists threatened to release Nvidia's LHR code - part of a claimed 1TB data haul it had gathered over the preceding week. Nvidia reacted the next day with its first official statement about the code theft. At the same time, Lapsus$ ramped up its financial demands - asking for a payoff to keep Nvidia's data under wraps.
The financial sums at stake became apparent, as Lapsus$ had put a sticker price of $1 million on keeping the LHR bypass code secret. Most recently, Nvidia was jabbed by the hackers again yesterday. Lasus$ appeared to release credentials of 71,355 Nvidia employees, perhaps as another warning that the green team needs to pay up for it to shut up.
We don't have any evidence of Samsung and Lapsus$ quibbling over payoffs. That doesn't mean the extortionists didn't try to extract cash from Samsung before going public today. It seems likely that Samsung has resisted any financial demands, and that is why we are seeing this seemingly sensitive data distributed today.
Get Tom's Hardware's best news and in-depth reviews, straight to your inbox.
Hopefully, other companies will see Nvidia and Samsung's examples as obvious warnings that they could be next and will carefully examine and invest in their IT security.

Mark Tyson is a news editor at Tom's Hardware. He enjoys covering the full breadth of PC tech; from business and semiconductor design to products approaching the edge of reason.
-
jkflipflop98 You keep picking fights with the biggest dudes in the yard, eventually you're going to get silently shanked and disappear into the night.Reply -
hotaru251 most of this doesnt effect typical user or their usage.Reply
sure, if someone else with this info gets ur device, bu thats unlikely.
also bootloader is actually somewhat good for modding community as samsung limits control/access to do a lot of nice stuff with our devices. -
Arbiter051 This might be a stupid question. Does/could this effect Samsung hard drives as well?Reply -
renz496 Btw what happen to the hacker? I thought they was supposed to leak even more juicy info on nvidia part if they are not getting paid?Reply