'EFAIL' Vulnerability Undermines PGP, S/MIME Email Encryption
Researchers have discovered a vulnerability in the OpenPGP and S/MIME protocols that allows for the exfiltration of plaintext messages. (Both protocols are used to secure end-to-end encrypted emails.) They dubbed the vulnerability "EFAIL" because it effectively breaks these emails' protections. (And, you know, because every vulnerability has to have a catchy name and the email-fail portmanteau was simply too good to pass up.)
EFAIL Voids End-To-End Encryption
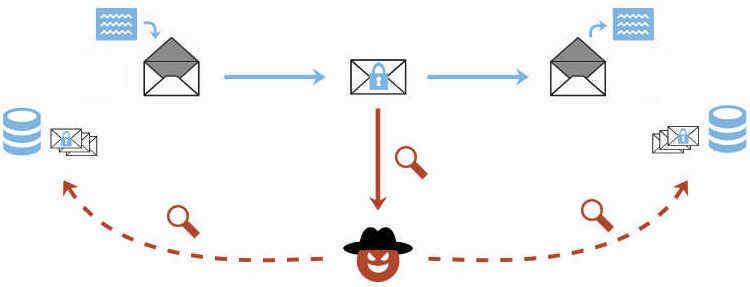
The researchers said on a website devoted to this vulnerability that "EFAIL abuses active content of HTML emails, for example externally loaded images or styles, to exfiltrate plaintext through requested URLs." This requires the attackers to already have gained access to the encrypted message by "eavesdropping on network traffic, compromising email accounts, email servers, backup systems, or client computers."
End-to-end encryption is used specifically to secure emails that have been compromised in those manners. The idea is that attackers shouldn't be able to read your messages even if they intercept them or somehow gain access to your accounts. EFAIL basically strips those protections and lets attackers read encrypted messages regardless of who sent them, how long ago they were sent, or how they were initially compromised.
Article continues belowThe researchers who discovered EFAIL said there's no way to know for sure if you were affected by the vulnerability. Their advice for mitigating the vulnerability's impact is to stop encrypting or decrypting emails directly in affected email clients and to disable HTML rendering. They do note, however, that disabling HTML rendering won't completely stop EFAIL attacks. Otherwise, it's up to developers to patch against the vulnerability.
How People Are Responding To EFAIL
Reactions to EFAIL's disclosure have been mixed. Some have criticized the researchers for teasing the vulnerability before publishing their full paper on it, while others have jumped straight to disabling PGP in their email clients. (S/MIME is more typically used to protect corporate emails, which means its use is up to the IT department, not individual workers.) We're still in the "knee-jerk reaction" phase of the response cycle.
The Electronic Frontier Foundation (EFF) is one of the parties advising people to disable PGP in their email clients. The organization provided step-by-step guides explaining how to do just that in Apple Mail, Outlook, and Thunderbird, which are the most popular clients affected by EFAIL. But the EFF did say this is a "temporary, conservative stopgap until the immediate risk of the exploit has passed and been mitigated against."
The Gnu Privacy Guard (GnuPG) team responded to the EFF's warnings by saying the problem lies with how email clients implement OpenPGP, not with the protocol itself. That's because EFAIL can be stopped by using authenticated encryption; OpenPGP started to support authenticated encryption in 2001. It's not a mandatory aspect of the protocol, however, which is why attacks like EFAIL can still happen 17 years later.
Get Tom's Hardware's best news and in-depth reviews, straight to your inbox.
Yet chances are good that many of the people who use OpenPGP do so via affected email clients. It doesn't matter whether the problem lies with the protocol or its implementation--messages that were supposed to be secure are now vulnerable either way. So how will this be fixed? Will devs willingly fix their implementations of OpenPGP, or will authenticated encryption have to be made a mandatory part of using the protocol?
Nobody knows. But we do know that end-to-end encrypted emails aren't as secure as we thought they were, and that means we'll have to continue to be careful about how we communicate. Encrypting messages is still safer than not encrypting them--EFAIL basically just lets attackers read messages they've already compromised in some other way--but it's still not enough to truly protect the contents of those emails.
You can learn more about EFAIL via the researchers' paper on the vulnerability.

Nathaniel Mott is a freelance news and features writer for Tom's Hardware US, covering breaking news, security, and the silliest aspects of the tech industry.