FedEx Exposed Customer Data To The Public For Years
Get Tom's Hardware's best news and in-depth reviews, straight to your inbox.
You are now subscribed
Your newsletter sign-up was successful
Over the past couple of years we’ve seen multiple big companies, and even the Pentagon, expose large amounts of data that wasn’t supposed to be public due to improper configuration of Amazon S3 servers. FedEx is the latest to have exposed its customers’ records this way.
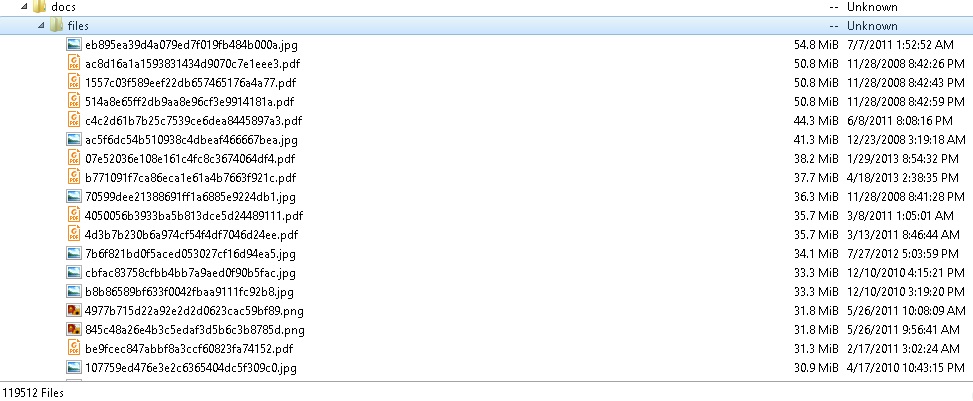
On February 5, security researchers from the German IT company Kromtech uncovered an Amazon S3 bucket set for public access. The researchers found more than 119,000 documents of U.S. and international citizens that included passports, driver licenses, security IDs, and more. The IDs were accompanied by "Applications for Delivery of Mail Through Agent" forms, which also contained names, addresses, zip codes, and phone numbers.
After further analyzing the data, the Kromtech researchers concluded that the data belonged to Bongo International LLC, a company that specialized in helping North American companies sell online to consumers in other countries.
Article continues below
FedEx purchased Bongo in 2014, and in 2016 it relaunched it under the name of FedEx Cross-Border International, to "address international purchasing obstacles with a seamless checkout and delivery approach that accepts over 80 currencies, provides 15 payment options, manages multiple delivery options, and offers credit card fraud protection, all through a single platform."
Ultimately, the FedEx Cross-Border service shut down in April, 2017. Kromtech’s researchers believe that anyone who used the Bongo service between 2009 and 2012 had their data exposed to the public.
Bob Diachenko, head of communications, Kromtech Security Center, said:
Technically, anybody who used Bongo International services back in 2009-2012 is at risk of having his/her documents scanned and available online for so many years. Seems like bucket has been available for public access for many years in a row. Applications are dated within 2009-2012 range, and it is unknown whether FedEx was aware of that "heritage" when it bought Bongo International back in 2014.
Get Tom's Hardware's best news and in-depth reviews, straight to your inbox.
Kromtech also believes that when a company sells its assets to another company, it should notify its customers that their data is being transferred to someone else. Additionally, the company getting the data should allow those customers to opt out of the transfer.
Amazon announced some changes to its Amazon S3 services last year, soon after the Pentagon data leak, to bolster the service's security. These should at least minimize data exposures due to erroneous configurations, as the IT managers will be warned when the data is public.
Lucian Armasu is a Contributing Writer for Tom's Hardware US. He covers software news and the issues surrounding privacy and security.