Imperva: 71 SQL Injection Attacks Per Hour Since July
Imperva's latest report reveals that web applications are attacked by SQL injection an average of 71 times per hour.
Get Tom's Hardware's best news and in-depth reviews, straight to your inbox.
You are now subscribed
Your newsletter sign-up was successful
On Thursday the Justice Department confirmed that the FBI arrested two alleged members of LulzSec and Anonymous in San Francisco and Phoenix while also securing charges against a third suspect from Ohio. The FBI was also said to be executing search warrants in New Jersey, Minnesota and Montana.
According to reports, 23-year-old Cody "recursion" Kretsinger from Phoenix, Arizona is believed to be a current or former member of LulzSec and has been charged with conspiracy and the unauthorized impairment of a protected computer.
Additionally, 47-year-old Christopher Doyon of Mountain View, California, believed to be part of Anonymous, has been charged with conspiracy to cause intentional damage to a protected computer, causing intentional damage to a protected computer and aiding and abetting. 26-year-old Joshua Covelli of Fairborn, Ohio also faces the same charges.
Article continues belowAs reported earlier, LulzSec and Anonymous use a hacking technique called SQL injection (SQLi) to breach systems. Thursday Imperva pointed to a recent report (PDF) stating that, since July, web applications are attacked by using SQL injection an average of 71 times per hour. Even more, specific applications were occasionally under aggressive attacks and at their peak, were attacked 800 to 1300 times per hour.
"SQL injection is the most pernicious vulnerability in human computer history," Imperva said in a blog earlier this week. "From 2005 through today, SQL injection has been responsible for 83-percent of successful hacking-related data breaches. Using data from Privacyrights.org, we checked the data breaches from 2005 to today. There were 312,437,487 data records lost due to hacking with about 262 million records from various breaches including TJMax, RockYou and Heartland, all of which were SQL injection attacks."
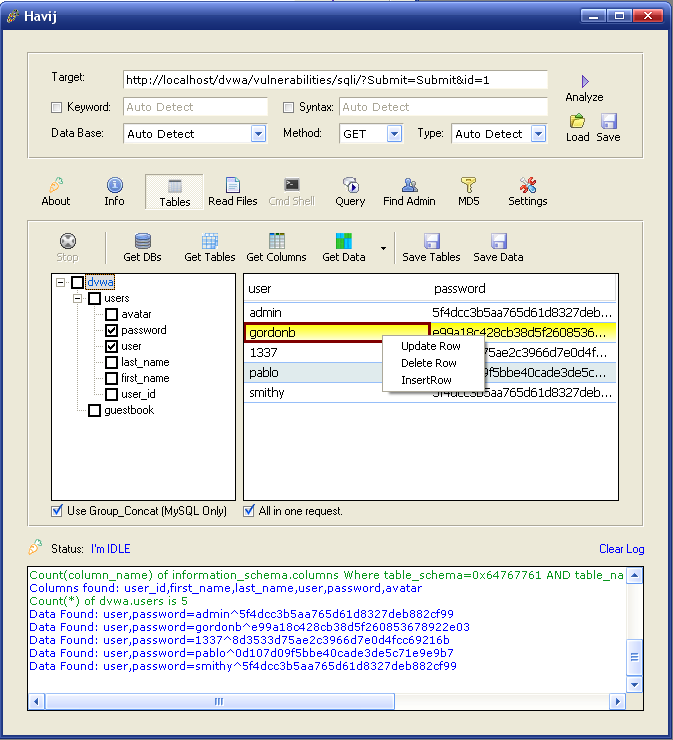
According to the report, hackers are using new SQLi attack variants which allow the evasion of simple signature-based defense mechanisms. Hackers are also using readily-available automated hacking tools like Sqlmap and Havij. To execute their attack, hackers hide behind a distributed network of compromised hosts, or "zombies," that are used in an interchangeable manner in order to defeat black-listing defense mechanisms. Nearly 41-percent of all SQLi attacks originate from just ten hosts.
To combat these attacks, Imperva suggests that companies use a combination of application layer knowledge (application profile) and a pre-configured database of attack vector formats. They also need to identify the access patterns of automated tools, and create and deploy a blacklist of hosts that have initiated SQLi attacks.
Get Tom's Hardware's best news and in-depth reviews, straight to your inbox.
The report goes on to reveal that 58-percent of the SQLi attacks occurring since July have originated here in the States. Sweden trails way behind with 11-percent, followed by China (8-percent), Great Britain (6-percent) and Vietnam (3-percent). The Netherlands, Bulgaria, Ecuador, the European Union and Germany are also on the list. Imperva also shows an "Other" listing which executed another 6-percent of the attacks since July.

Kevin Parrish has over a decade of experience as a writer, editor, and product tester. His work focused on computer hardware, networking equipment, smartphones, tablets, gaming consoles, and other internet-connected devices. His work has appeared in Tom's Hardware, Tom's Guide, Maximum PC, Digital Trends, Android Authority, How-To Geek, Lifewire, and others.
-
gmarsack @otacom72, totally agreed. Bad programming = easy attack. SQLi is simple to do and it's simple to prevent. Lazy = bad.Reply -
ThisIsMe Kevin ParrishNearly 41-percent of all SQLi attacks originate from just ten hosts.So why don't they go and physically find the 10 hosts and knock on their owners door and either arrest them, or at the very least tell them to GET SOME FREAKING ANTI-MALWARE SOFTWARE or something. I mean at least make them turn the "hosts" off.Reply
gmarsack@otacom72, totally agreed. Bad programming = easy attack. SQLi is simple to do and it's simple to prevent. Lazy = bad.If they were so simple to prevent, they wouldn't be so simple to do. Maybe some issues means laziness, but most are something that is accidentally overlooked after thousands of updates to websites every year. Odds are someone will slip up and make a mistake sometime. Human error will always be a problem and you cannot defend against it aside from redundancy checks by some automated means and other humans doing QA on all updated code. However, in the end, no system is or will be prefect. The only systems that come close cost major amounts of resources to maintain. -
Vladislaus ThisIsMeSo why don't they go and physically find the 10 hosts and knock on their owners door and either arrest them, or at the very least tell them to GET SOME FREAKING ANTI-MALWARE SOFTWARE or something. I mean at least make them turn the "hosts" off.So you're saying that someone should be arrested because it's computer has bad security and is being used to hack sites with also bad security. Logical.Reply -
freggo Funny, this 'article' very nicely mirrors the entry in Wikipedia at http://en.wikipedia.org/wiki/SQL_injectionReply
If we stop being lazy and spend a little time checking a user's data entries the problem is no problem anymore.
-
ThisIsMe VladislausSo you're saying that someone should be arrested because it's computer has bad security and is being used to hack sites with also bad security. Logical.Is that what I said?Reply
Read the whole thing. ;) I said "either arrest them, or at the very least tell them to get some freaking anti-malware software." Obviously I meant whatever is the most logically applicable. For all you know some of these 10 hosts could be helping these guys or at the very least know who they are. The stuff could have been put on their PC's after they called a local place and had a "guy" come out and "look" at their PC because they needed it repaired or something to that extent. I think it at least warrants a look into the matter. Don't you, Mr. Logical? -
cheepstuff freggoFunny, this 'article' very nicely mirrors the entry in Wikipedia at http://en.wikipedia.org/wiki/SQL_injectionIf we stop being lazy and spend a little time checking a user's data entries the problem is no problem anymore.Reply
It closely mirrors Wikipedia because Wikipedia is using the same source article.
-
eddieroolz You'd think the government would hire more SQL programmers to cover these vulnerabilities.Reply -
freggo cheepstuffIt closely mirrors Wikipedia because Wikipedia is using the same source article.Reply
I find it highly unlikely that Wikipedia is "using" someone else's original article if for no other reason than possible copyright infringement accusations. -
Vladislaus eddieroolzYou'd think the government would hire more SQL programmers to cover these vulnerabilities.This is a problem that affects tons of website not related to any governments. So the responsibility shouldn't be on government hands in those cases.Reply