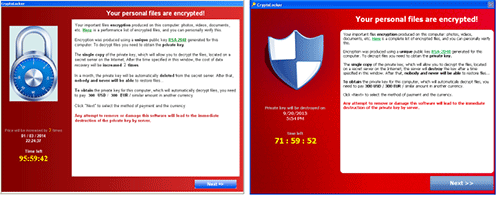
Improved CryptoLocker Clone "Cryptowall" Has Locked Over Half A Million PCs, 5 Billion Files
A few months ago, the devastating CryptoLocker malware that has locked the files of half a million PC users across the world was finally neutralized. The US government managed to seize the computers that were spreading the CryptoLocker malware with support from some security experts. Later, a security firm made public a tool that people whose PCs were infected could use to decrypt and recover their files.
But Cryptolocker wasn't the only ransomware spreading on the Internet. Since Cryptolocker was taken down, Cryptowall, a similar piece of ransomware that has existed since November 2013, has taken Cryptolocker's place and has already infected 625,000 PCs and over 5.25 billion files.
Cryptowall has been using a variety of ways to infect so many PCs in so little time, including through spam mail with attachments; infecting websites that users visit and then downloading programs that are infected with CryptoWall; and through other malware that had already existed on people's PCs. The infection can affect not only local hard drives but also mapped cloud drives, such as Google Drive or Dropbox.
Cryptowall assigns a unique identifier for each infection and a single key that can be used to decrypt those files, so unless someone gets access to all of these keys, then the infected PC owners won't ever be able to decrypt those files.
The alternative is to pay the ransomware makers somewhere around $500 through Bitcoin. The problem with that is that even if the file owners want to pay, not too many are able to use Bitcoin or know how to pay with it, so only 0.27 percent of people who had their PCs infected have paid the ransom to the creators of CryptoWall. That's a much lower number compared to 1.3 percent for CryptoLocker, which gained most of its money by using other payment methods such as MoneyPak.
The US seems to have the most CryptoWall infections: 253,521 (or about 40 percent), followed by Vietnam with 66,590 infections, the U.K. with 40,258, Canada with 32,579 and India with 22,582.
The best way to stay protected against CryptoWall is to avoid downloading strange files from random e-mails or places on the Internet, and you should avoid using Administrator accounts on your PC that could make it easier for such malware to be installed without your knowledge.
Get Tom's Hardware's best news and in-depth reviews, straight to your inbox.
Follow us @tomshardware, on Facebook and on Google+.
Lucian Armasu is a Contributing Writer for Tom's Hardware US. He covers software news and the issues surrounding privacy and security.
-
whiteodian These bad boys have hit my company a few times. Stupid users will click on anything.Reply -
soccerplayer88 That's really the biggest problem.Reply
We regularly go over safe browsing habits with customers but short of us "policing" their internet these problems will never go away.
So at the very least we strongly encourage users to either purchase a backup external drive or setting them up to save files to a central server. Worse case scenario we can just roll back the backup and all is well. -
rayden54 If they really wanted to be paid you'd think pick an easier way--or less money. I know people who've had computers for years and every file they've ever acquired will fit on a single DVD. It might be worth $10-$15 to unlock their files, but for $500 they'll just buy a new computer.Reply -
Christopher1 Having an admin account really has nothing to do with these things. Even if you have a standard user account that you use daily, the problem is that these things have methods to get around UAC and other protections in Windows Vista-8.Reply
Now, as to the "Don't download programs from iffy websites!" that I agree with.
If they really wanted to be paid you'd think pick an easier way--or less money. I know people who've had computers for years and every file they've ever acquired will fit on a single DVD. It might be worth $10-$15 to unlock their files, but for $500 they'll just buy a new computer.
Or they will just re-image their computer and have done with it. That is what I would do in this situation, re-image my computer and move the hell on. -
mapesdhs If I fitted my house with locks which failed so miserably at preventingReply
a break-in, beyond any insurance claim I'd certainly consider suing
the lock maker. What we need one of these days is a person/company to
sue MS (or class action) to force them to make operating systems
with far better security by default. The security mess known as Windows
has been plodding along for years & years, costing individuals & corps
enormous sums every year in wasted time, resources, etc., yet nothing
seems to change. Instead, blame & responsibility is placed upon the
user wrt to visited sites, handling emails, downloads, etc. - an approach
which means the security 'effort' is replicated billions of times over and
over again with no improvement in the base system. The focus is
entirely at the wrong end of the scale; a decently written OS shouldn't
be such a security nightmare in the first place, but because winblows
is standard, nobody seems to care, it's regarded as normal, an attitude
found nowhere else in modern consumer tech. If an ordinary consumer
tells a computer shop owner that their PC has a virus problem, they are
told that's a normal risk; same response for a bug-related BSOD or other
Windows issue. When are we going to say enough is enough and force
the responsibility back onto MS?
I quite like Win7 in general terms, but it's security aspects are absolute
junk compared to the 15-year-old UNIX box I also use.
I have no interest in Win8; I only use desktops & thus refuse to be treated
like a child by being forced to use a gesture-focused interface more suited
to a slate & chalk era.
Ian.
-
warezme ReplyIf I fitted my house with locks which failed so miserably at preventing
a break-in,
It doesn't matter what MS does. If you fitted your house with locks and every time ANYONE knocked on the door you opened it up for them and invited them in for cookies, your locks are still worthless.
People unfortunately when it comes to computers, are stupid. They treat them like appliances which they are not. I have been running windows for many many years and I could count on one hand (2 fingers) how many times I have had a problem with malware or viruses. Of those two times I recognized immediately what I did wrong and knew how to fix it.
-
oxxfatelostxxo ReplyIf I fitted my house with locks which failed so miserably at preventing
a break-in,
It doesn't matter what MS does. If you fitted your house with locks and every time ANYONE knocked on the door you opened it up for them and invited them in for cookies, your locks are still worthless.
Funny way of putting it, however he is correct. Not only are 95%(made up number) of the viruses and spamware on peoples computer on there because of their own doing but no matter how well designed any program is if somebody wants to break into it they will.
Seriously though when even government computers get hacked into every now and then and their security and restrictions on what a user can do are a 1000x more extreme, don't expect a home computer to ever be 100% unless you leave it powered off. -
Blazer1985 You can have the best lock money can buy but as long as you leave the door open (click on install) you can't expect great protection.Reply -
Achoo22 ReplyIf I fitted my house with locks which failed so miserably at preventing
a break-in, beyond any insurance claim I'd certainly consider suing
the lock maker. What we need one of these days is a person/company to
sue MS (or class action) to force them to make operating systems
with far better security by default. The security mess known as Windows
has been plodding along for years & years, costing individuals & corps
enormous sums every year in wasted time, resources, etc., yet nothing
seems to change.
It's painful to see dozens of "blame the victim" posts, but that seems to be the trend on much of the Internet. It's equally troubling to see thoughtful posts like your own downvoted so hard.
MS could absolutely provide an OS with better security. Virtualization technology has been readily available for decades, so there's no reason that "unsafe" code should be allowed to takeover your system, just as there's no reason that DRM should be able to upload your financial documents or e-mail.
The idea of holding software developers accountable for their software would do much to ensure software correctness and ethics. Only licensed software architects should be able to distribute certified software, and everything else should be restricted to sandboxes (which, honestly, really shouldn't limit functionality in any way). There are a ton of other professions that require licensure, so I don't think it's really that big of a stretch to require it of software developers.
I'd also like to see some legislation that limits OEM hardware and software to functions that support their advertised use. So, no more cell phones that come prepackaged w/ spyware, no SmartTVs that record and upload your viewing habits, etc. -
Marcel Hardy Precisely why there need be monitoring for accountability. I believe in a neutral Internet where all traffic run uninhibited like the free air we speak in. But certainly when one overhears of a crime and they should do something about it. That is mature and responcible. To whine over anonymity is paranoia, selfishness, immature and conceited. A free uninhibited net with accountability is responcible and prudent and a mature internet. Many will whine as they do best. But the whining spoiled coward is always the liability to all and themselves. To act without integrity and cowardice is what too many twenty somethings do. Like the brat wanting his way. Privacy for what. If the NSA wants to plant a camera iin my toilet I am not ashamed. Anti-social zealots whom hide behind screens too much neednt decide anyones future. They cant cope with their own.Reply