UpGuard: RNC Firm Exposed Data Of 198 Million American Voters
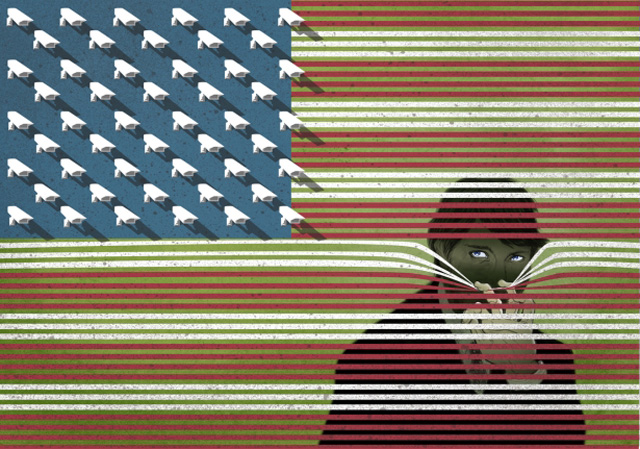
UpGuard revealed that a misconfigured database made the personal information of 198 million U.S. voters publicly available to anyone who went looking for it. The security company said this is the "largest known data exposure of its kind," and that the data includes 1.1TB of "entirely unsecured personal information" collected by three data firms hired by the Republican National Committee (RNC) during the 2016 presidential election.
The exposed information includes the "names, dates of birth, home addresses, phone numbers, and voter registration details" of nearly all of America's registered voters, UpGuard said in its disclosure, "as well as data described as 'modeled' voter ethnicities and religions." The company said the data was collected by TargetPoint Consulting, Data Trust, and Deep Root Analytics (DRA) and stored on a publicly accessible server managed by DRA. All three firms have connections to the GOP and were hired to help the party win the 2016 presidential election.
TargetPoint, Data Trust, and DRA have not released statements about this disclosure. TargetPoint and DRA have not responded to our requests for comment, and a Data Trust spokesperson said, "We are aware of Deep Root's situation, but inquiries about it need to be directed to them."
UpGuard cyber risk analyst Chris Vickery discovered the misconfigured database on June 12. Besides the 1.1TB of publicly accessible information, another 24TB of secured data was stored on the server. Vickery downloaded the public info between June 12 and June 14, at which point UpGuard notified "federal authorities" about the leak. DRA is said to have blocked public access to all of the server's data shortly after that disclosure. It's not clear for how long the server was publicly accessible, or how many people downloaded the data before it was secured.
This leak highlights the dangers of collecting personal information about hundreds of millions of people. It's worth driving home the point that nobody stole this data--it was made publicly available to anyone who went looking for it. Besides harming U.S. voters' privacy, the information and analysis affected by this leak could put people at risk of phishing campaigns or other, more damaging attacks.
The revelation of personal data might not be the most damaging aspect of this leak. That dubious honor belongs to spreadsheets that sought to answer questions, according to UpGuard, "ranging from how likely it is the individual voted for Obama in 2012, to whether they agree with the Trump foreign policy of 'America First,' to how likely they are to be concerned with auto manufacturing as an issue, among others." UpGuard's Dan O'Sullivan said he was able to "view his modeled policy preferences and political actions as calculated by TargetPoint" and that they were "astoundingly accurate."
Those models could help hackers personalize their attacks. It's easier to make someone click on a link, download a file, or otherwise let their guard down with more carefully targeted attacks. So-called spear-phishing attacks are often more successful than mass emails from "Nigerian princes" willing to shower you with riches if you front them a few bucks. The information and analysis exposed by this leak would make those targeted attacks much easier to conduct. Almost everyone who was registered to vote in the 2016 election could now be in danger.
Get Tom's Hardware's best news and in-depth reviews, straight to your inbox.
Unfortunately, there's nowhere to go but down from here. As UpGuard said in its disclosure:
The fundamental problems which exposed this data are not rare, uncommon, or consigned to one side of the partisan divide; indeed, while those responsible for this exposure are of one party, the 198 million Americans affected span the entire political spectrum, their information revealed regardless of their political beliefs. The same factors that have resulted in thousands of previous data breaches—forgotten databases, third-party vendor risks, inappropriate permissions—combined with the RNC campaign operation to create a nearly unprecedented data breach. [...] Despite the breadth of this breach, it will doubtlessly be topped in the future—to a likely far more damaging effect—if the ethos of cyber resilience across all platforms does not become the common language of all internet-facing systems.
Political parties, private companies, and other organizations are only going to become more reliant on big data. Knowledge is power, after all, and databases like this hold all the knowledge that the powerful could want. It makes it easier for politicians to win elections, companies to target advertisements, and other organizations to boost their own effectiveness. Unfortunately, the apparent inability to secure this information means it will also be used to attack the people behind the data, whether it's by breaching an organization's systems or accessing a public server.

Nathaniel Mott is a freelance news and features writer for Tom's Hardware US, covering breaking news, security, and the silliest aspects of the tech industry.
-
jtd871 Sounds like grounds for demanding the US Federal Government provide free credit monitoring for all US citizens...lolReply -
Danilushka Meanwhile, the Left leaks from deep in our nation's government and obstruct's justice (Lynch, Obama spying) and liberal media ignore it. But if they can pin it on a rightwing group, silence is broken...loudly.Reply -
bit_user If they collected and modeled this data, so can anyone else. It's just a matter of $. Although, being able to download a copy for free is certainly more budget-friendly for most hackers, spammers, and scammers.Reply
What I find more scary is the prospect that politicians' web sites can be tailored to the political views of the person browsing it. It could emphasize points you're likely to agree with, and bury positions of the candidate's you'd oppose. Web analytics companies are so sophisticated they don't even need the kind of database mentioned above. They probably already know enough about you.
-
synphul As scary as this sounds, between windows/cortana, google and amazon they probably know far more about us and have it stashed away than these voter analysis companies do. Just as thieves get irritated with the government over competition, so do tech firms get irritated by competition when others are harvesting data. That's their gig.Reply -
teamninja So lucky I didn't vote this time around, no one in my family bothered this time around.Reply -
bit_user Reply
If you're registered, then you're certainly in that database. The total number of Americans voting in the 2016 federal election was not 198 million, I'm sad to say.19838743 said:So lucky I didn't vote this time around, no one in my family bothered this time around.
http://thehill.com/homenews/state-watch/324206-new-report-finds-that-voter-turnout-in-2016-topped-2012
And they care very much about people who didn't vote, that they might be able to turn out for their side.
We should consider it our civic duty to stay informed and participate. Voting is only the first step in participatory governance. -
bit_user Reply
The lack or weakness of available encryption wasn't the problem. It was probably just a case of recklessness and irresponsibility.19839205 said:Welcome to the naked America!
Now think about it do you want a end to end encryption?
The 4th Amendment of the US Constitution protects against spying on the citizens by the government (without probable cause, at least), but these protections don't extend to online data collection by private individuals or corporations. What we need are laws establishing individuals' rights over their data and rules & requirements applying to anyone holding that data.
I'm not optimistic, since personal data has become the lifeblood of the online economy. The combined valuation of all the businesses trading on this stuff probably ranges into the tens of $Trillions.
-
therealduckofdeath Hey, Danilushka, don't use your actual Russian account when you're spinning your typical B on the internet. It kind of makes everything you say sound too comical.Reply