Valve's Steam Client Had A Decade-Old Remote Code Execution Bug
Tom Court, a senior researcher at the Context security company, found a remote code execution bug that has existed in the Steam client for more than a decade.
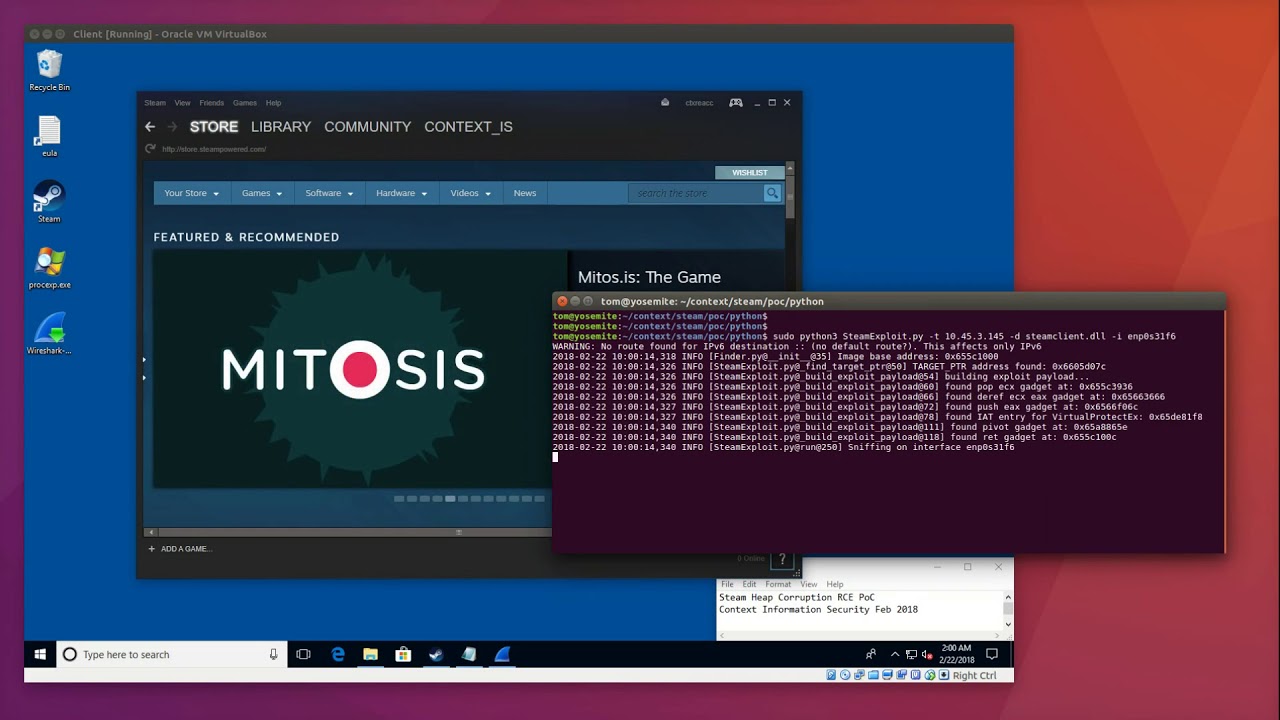
Heap Corruption In Steam Client Library
The bug was a heap corruption that could have allowed attackers to remotely trigger a memory leak. The Steam client uses a custom protocol delivered on top of the User Datagram Protocol (UDP), which has two fields that are relevant to the vulnerability. One is packet length and the other is total reassembled datagram length.
The vulnerability resulted from the absence of a check to ensure that, for the first packet of a fragmented datagram, the specified packet length was less than or equal to the total datagram length. According to Court, this heap corruption bug, aided by the fact that Valve didn’t even use address space layout randomization (ASLR) protection for its client, could have allowed attackers to turn this bug into a highly reliable exploit.
Valve Mitigated The Bug By Accident
Last July, Valve started implementing ASLR and other exploit mitigations into its client, which would then cause the client to crash if someone would try to exploit the bug. At the time, Valve was not aware of this bug, so it stopped it from working by accident.
However, according to Court, if attackers were able to use a separate information leak vulnerability, they could have learned the memory location of the heap corruption bug, making ASLR irrelevant at that point. ASLR’s purpose is to randomize the location of code in memory.
Court said that he disclosed the bug to Valve on February 20 and that the company pushed a patch to the beta version of the Steam client less than 12 hours later. The stable version of the client received the patch a month later, on March 22.
Get Tom's Hardware's best news and in-depth reviews, straight to your inbox.
Lucian Armasu is a Contributing Writer for Tom's Hardware US. He covers software news and the issues surrounding privacy and security.