WD Warns Customers That Hackers Stole Their Data

In March, Western Digital identified a network security incident in which both customer and company data were compromised. Western Digital notified those affected so they could take action to secure their private data as much as possible. Since this security breach, certain online functions have been halted. This week we’ve received an update on the situation along with plans to restore online activity.
According to Western Digital, an unknown third party accessed a Western Digital database containing customer information, including not only their names, addresses, and phone numbers but also billing details such as credit card information, although the numbers were encrypted. The customers impacted by this breach were contacted by Western Digital immediately so they could take action to help protect their private information.
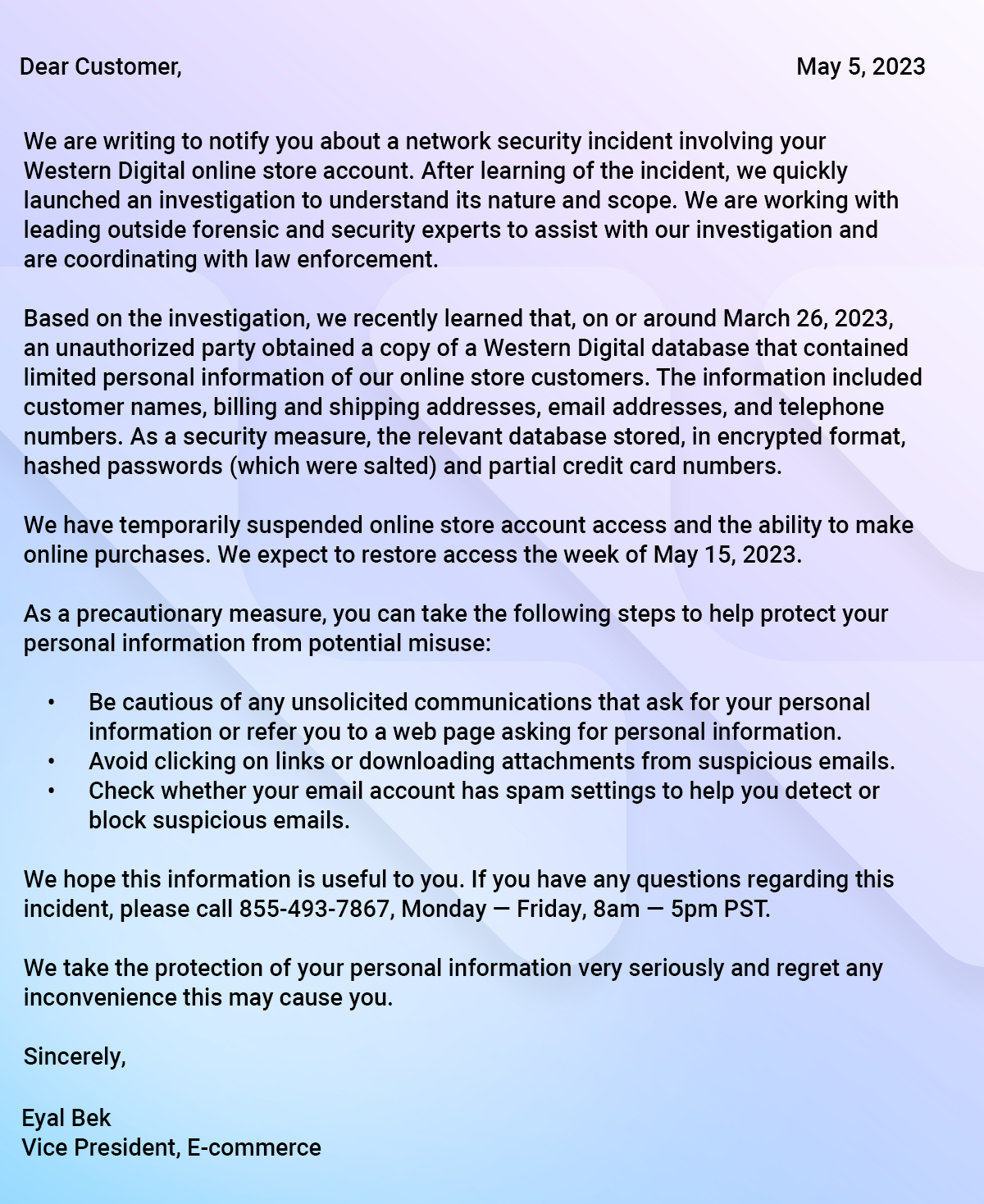
A reader submitted to us a copy of the notification sent from Western Digital pertaining to the matter.
Within a few days of the incident, on April 2nd, Western Digital made a public announcement about the matter and initiated a response to rectify the situation. This involved a plan to completely shut down certain services from public internet access, including the online web store. Many services have since been restored, but the online store is still shut down and cannot be used to process orders.
Despite the ongoing effort to limit online activity, Western Digital says that physical factories have been operating the entire time to help deliver products. The only impact has been for online services. So while new orders currently cannot be placed, existing orders can still be processed and delivered.
Western Digital confirmed that My Cloud services were completely restored by April 13th. The online store, however, is still shut down. However, users can expect account access to be restored by the week of May 15th. In the meantime, online orders will not be processed to ensure customer data can be appropriately protected.
If you want to read more about the incident, its impact, and Western Digital’s response, you can find the full press release on the official Western Digital website.
Get Tom's Hardware's best news and in-depth reviews, straight to your inbox.

Ash Hill is a contributing writer for Tom's Hardware with a wealth of experience in the hobby electronics, 3D printing and PCs. She manages the Pi projects of the month and much of our daily Raspberry Pi reporting while also finding the best coupons and deals on all tech.
-
TechieTwo IMO this is totally unacceptable. If a company is online then they have a legal obligation to prevent all unauthorized access to their customer's data. Providing a free credit report for three years doesn't in any way make a customer "whole" in the legal sense. Massive fines should be imposed by the FTC and the money distributed to those impacted by the insufficient internet security protection employed.Reply -
RichardtST Reply
Yes and no. It isn't quite that easy. Demanding absolute security like that really raises the bar, the cost to just get started. So no more little guys getting on the net. Big boys only because of the prohibitive cost. Second, its never going to be secure. Forget about it. Deal with it. DO NOT LEAVE INFORMATION ONLINE. God forbid you allow a site to "store your credit card data" for ease of use later. The bigger the site, the more data it has, the more valuable it is as a target. I 100% agree that it is totally unacceptable. Unfortunately there is no such thing as "computer security" and we live in a dishonest, corrupted world. Don't leave your data out in the open lying around at a bunch of different sites. That the best you can do. Oh yeah... and don't "link your back account" to anywhere either...TechieTwo said:IMO this is totally unacceptable. If a company is online then they have a legal obligation to prevent all unauthorized access to their customer's data. Providing a free credit report for three years doesn't in any way make a customer "whole" in the legal sense. Massive fines should be imposed by the FTC and the money distributed to those impacted by the insufficient internet security protection employed. -
Darkbreeze WD isn't in the "little guys" conversation. They are a company that had a 3.1 BILLION dollars revenue last year. Any company with a revenue in excess of 500 million has ZERO excuse for not having adequate protections in place.Reply
By the way, that's the picture of the letter WD sent me in the article. I sent it to Avram this morning asking why no article. WD, like pretty much everybody, needs to REALLY step up their game in terms of network and database security. They can do this, and by "they" I mean all large companies, they just choose not to take the steps that half our veteran members here could easily advise about and implement, because any fool with an IT degree regardless of actual competence, can get a job anywhere these days. Pathetic. -
hannibal Even bigger companies get hacked!Reply
So you can newer trust any online service.
Some are harder to hack, some less hard. Even covernment services has been hacked. -
Sluggotg That is why I don't use "Cloud" Storage. ( I did have to use Microsoft's Cloud for Work. The company thinks it is better than using local servers). I can see how handy it is and would certainly be fine for most people but typically they put everything there, including Important sensitive data. I do think the people that perform these hacks should face serious Jail Time. These are not Pranks.Reply -
danger007 The solution to all these database breaches is simple. You have to make it a serious issue in the United States or America. I find it outrageous that companies that have leaked my info usually send a letter saying sorry, do better next time, should feel secure they didn't get you entire credit card. However with a breach how are they going to truly know what was or was not accessed, after all if you are a hacker you won't fiddle with credit card numbers where possible without whipping their tracks clean so the credit card could be used a few times before it is stopped.Reply
Hospitals, banks, big companies like Western Digital, etc need to be made to answer to this screw up. Should they be required any illegal charges made on a credit card that was given to WD no matter where the purchase happened, like the card was used to buy jewelry at Zales. Should they automatically must issue a minimum of 2 years of credit monitoring? Should they have to give some sort of store credit equal to a % of a persons purchase? Should they be fined into the millions leaving them barely enough to show they made money that year.? What about discounts to all affects customers for 2 years, no 5% or 10% but maybe 15-20% and that it can be applied to any purchase even if already on sale or already using a computer code.
All punishments sadly most companies blow it off with a bulk accounts with a credit monitoring agency and they are off the hook, mostly.
Instead we need rules that truly spell out punishment. First the CTO should face fines, the CEO or maybe the entire board should face fines. Reward employees who find the holes. Be required to pass an annual or bi-annual or 1 every 3 years assault on their servers in which they must pay a reward to whoever can get in or exploit a hole. Then show notice to some Government agency that oversees the fines, overseas the tests, etc. Sorry if you are looking at this as a political career, don't apply. You need to have white, grey and even black credentials. Give this team much better pay than our elected officials since they are actually doing something. NO REPUBLICAN vs DEMOCRAT filling of slots on this new agency.
The agency and its employees select from amongst them the person they all feel will do the best job in managing teams. Perhaps put rewards for this head of whatever and those who selected with bonuses if they are able to show they did their job, like we hacked Company A and gave them a full list of what to fix. Then 2 months down the road, Company A is hacked and it was one of those on the list of exploits, this team/agency gets a reward paid for by the Company A and that company is put on notice the upper management must certify all exploits/holes, etc are fixed within 6 months or even a year. As the same team that hacked is assigned to hack again, if they breach Company A, again, then the upper management should face even harsher fines and maybe being fired.
The low people on the chart should be given cash bonus or stock, for locating and providing exact ways to breach/exploit the system where they send it to this agency and once confirmed that person is many times better off, with the company A paying the reward, sorry no gift cards to Starbucks, no $5 or 5% off next purchase. Maybe $500 in cash, 750, 1000? Each company must invest in a hacking prevention plan and have people whose only job is to hack the system. They sign NDA's and they have cameras on them all the time and maybe even get a pat down looking for hidden USB devices in case they are real black haters looking to breach for their own personal or web interest.
Who in government would have oversight? Well they should pass a basic Windows Security and IT/Network exam to make sure they know the difference between port open and port closed. Of course none of them would probably pass, so might need to hold election in each state for hackers who have shown they are white hatters and have only done good for companies and not sold or used the data they breach. They have no vote of course in Congress but they are to report the performance of this special agency.
Until companies see rules and regulations that hit the pocket books of the highest upper management and the company they won't change. Perhaps their profit after expenses and taxes is seized and that money is used to fix the issue and no dividend is paid for that year, shareholders will oust those board members for costing them a ROI. That way the CEO and Board of Directors will spend less time counting their money and their income and more time focused on exploits.
Of course what do you do when the exploit is because of Microsoft and not how a company has things set up? Maybe software companies have to have their new software test and gets some sort of certification. Obviously the shareware, free online software would be exempt except they still can face accountability if their software creates an exploit or some basic reason, but how to punish will be difficult and it would end the days of free software, so how to punish but not chase away developers or innovators.
