Windows 7 Suffers ‘Total Meltdown’ Thanks To Microsoft’s Meltdown Patch
As if the Meltdown and Spectre CPU flaws weren’t bad enough on their own, Microsoft was somehow able to make the flaw even worse on Windows 7. According to Swedish security researcher Ulf Frisk, the fix that Microsoft provided to Windows 7 computers for the Meltdown flaw, which could allow attackers to read kernel memory at a speed of 120 KB/s, would now allow attackers to read the same kernel memory with a speed of gigabytes per second.
“Total Meltdown”
Frisk called the new vulnerability, which Microsoft introduced on Windows 7 machines while trying to fix the Meltdown flaw, “Total Meltdown.” The new bug allows any process to read the complete memory contents of the system, and it also makes it possible to write code to arbitrary memory, too.
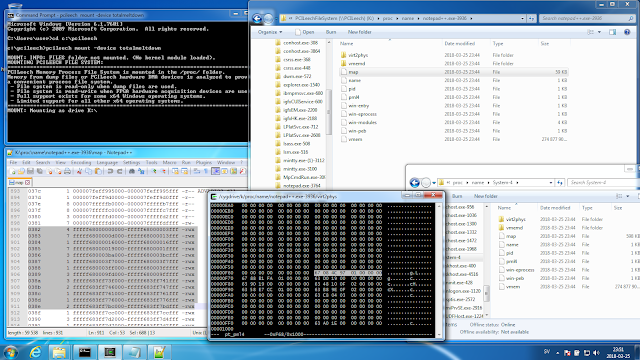
According to Frisk, no special attack or technique was needed. All he had to do was take advantage of Windows 7’s mapping of memory contents that belong to running processes.
The main issue and mistake made by Microsoft is that the company set the PML4 page table permission bit to User instead of the kernel Supervisor. This made it so the memory that would normally be assigned to the kernel be assigned to every process, including those running with user-level privileges. The PML4 is the base of the 4-level in-memory page table hierarchy that the CPU Memory Management Unit (MMU) uses to translate the virtual addresses of a process into physical memory addresses in RAM.
In Windows 10, the PML4 is mapped to a random address, while in Windows 7 and Windows Server 2008 R2 the PML4 is always mapped to the fixed address 0xFFFFF6FB7DBED000 in virtual memory. The PML4 doesn’t exist in 32-bit versions of Windows, so these versions have been unaffected by this flaw.
Frisk said that:
Once read/write access has been gained to the page tables it will be trivially easy to gain access to the complete physical memory, unless it is additionally protected by Extended Page Tables (EPTs) used for Virtualization. All one have to do is to write their own Page Table Entries (PTEs) into the page tables to access arbitrary physical memory.
Get Tom's Hardware's best news and in-depth reviews, straight to your inbox.
Frisk also noted that Microsoft has already issued a fix for this bug earlier this month, after he alerted the company about it.
Patching In A Rush
Although Microsoft seems to have been one of the few companies that knew about Meltdown and Spectre earlier than the general public, it seems that the company was still able to bungle the release of the patches by rushing to fix the vulnerabilities as soon as possible.
Frisk’s revelation comes after Intel also botched the release of the Spectre variant 2 patch, which caused some rebooting issues for its customers. Microsoft and OEMs had to recall the patch for Windows machines. Microsoft's Meltdown and Spectre patches also caused some rebooting issues for older AMD systems, but the company blamed AMD on poor documentation.
Lucian Armasu is a Contributing Writer for Tom's Hardware US. He covers software news and the issues surrounding privacy and security.
-
ssdpro Windows 7 is over, move along and stop the bleeding. George W Bush was president when Windows 7 was developed - that is 3 USA presidents ago and the iPad didn't even exist. You can get a text message on a mobile phone but believe it or not some people are still using beepers and whining about it.Reply -
LORD_ORION "Ooh... see Windows 7 is so vulnerable... you better switch to Windows 10."Reply
-Microsoft -
hannibal Well at least this time the finder was professional and did give MS time to fix this before telling about it to all hackers unlike some amatour companies...Reply -
Myrmidonas I want a stable operating system to do my job. I am no labrat and I do not run like an idiot inside test labyrinths (W10 privacy settings), while being constantly injected with various unstable substances (creator updates!), for the crazy scientist (MS) to observe my reactions.Reply
I have paid for my operating system and I want it to operate the way I want and meets my needs. Sorry if you are butthurt (random W10 user), because we do not share your stupidity.You paid nothing and the OS does not belong to you to configure it the way you want. It belongs to MS and they are entitled to do as they please (and rape) on your machine. What? Didn't you read the licence agreement? Better luck next time.
Thank you -
RememberThe5th Windows- "I wanna update"Reply
Me- "Im playing GAME"
Windows- "but i wanna UPDATE"
Me- "NO"
Windows- "Updates anyway"
Me- -.-"
Well im not saying that Windows isn't bad, but, for Pete's sake, let me allow when to update, not when "you" want to update.
But as i've never read license agreement... neither i want to. Well if hacker wants to use my PC, ill let it, because i dont have any important data :D. -
lakimens Reply20835573 said:Windows 7 is over, move along and stop the bleeding. George W Bush was president when Windows 7 was developed - that is 3 USA presidents ago and the iPad didn't even exist. You can get a text message on a mobile phone but believe it or not some people are still using beepers and whining about it.
I swear, you people are unbelievable. Is it better that I get a BSOD every day on my "Donald Trump" Windows 10? I didn't get any BSOD on my "BUSH" Windows 7. -
USAFRet Reply20836034 said:
I swear, you people are unbelievable. Is it better that I get a BSOD every day on my "Donald Trump" Windows 10? I didn't get any BSOD on my "BUSH" Windows 7.
And having run Win 10, since Day 1 of the Tech Preview, on various hardware...
The number of BSOD's I've had can be counted on one hand. If I cut off 4 fingers. -
decker.davison I just upgraded to windows 10 from win7 when i also replaced my raid array this week. I was concerned about mounting potential vulnerabilities in less supported now termed "legacy" OS, win7. Newer is always better, right?Reply
Wrong!
Well, long story short, while troubleshooting driver incompatibilities between my older hardware's utilities+drivers from 2012 and windows 10, I managed to accidentally short my ga-z77x-ud5h rev 1.0 motherboard and am getting the 15->36->32(hangs on 32) mobo debug code the resets in a loop while attempting to POST. I cleared the cmos which didnt work then switched to the backup bios (dual-bios) and got it working again until i accidentally shorted it, im guessing from stupidly plugging in power connections of devices to the motherboard while it was already powered on- causing mobo to immediately reset, AGAIN while running on the backup bios too the second time and now neither bios will post. Cpu fan wont turn on anymore and accidentally corrupted both cmos chips most likely and bricked the mobo. Please PM me or something if your a uber-techy and can provide me a potential solution.
Before I screwed it up, windows 10 seemed tailored for tablet/mobile + touchscreen and appear to more similar to Android.
Don't even get me started on Cortana.... who actually wants to add a microphone to their desktop?
Thanks microsoft for making a bloated upgrade and abandoning simplicity.... at least 10 did away with the horrid "start screen" and went back to just a start menu overlay like a good gui -
10tacle Reply20835573 said:Windows 7 is over, move along and stop the bleeding. George W Bush was president when Windows 7 was developed - that is 3 USA presidents ago and the iPad didn't even exist. You can get a text message on a mobile phone but believe it or not some people are still using beepers and whining about it.
I understand your point about moving on, but a LOT of people out there reject MS's rather invasive approach with Windows 10. I have it on my general use laptop that I don't care about who sees what (got the free upgrade from Win7) but am still running Win7 on my gaming rig. I am holding out for what comes next beyond Win10 or the 2020 EOL extended support of Win7, whichever happens first.
Heck I only just retired Windows Vista two years ago on my 1080p backup gaming rig for looming non-support security reasons. A PC I built in 2009. And to put things in perspective, it was not too long ago that people and even businesses finally moved on from Windows XP - and only then for a lack of support. We should never be forced to upgrade OS's every three or four years.
People complained about Vista, but Windows 8/8.1 was a disaster as the shortest running OS in recent history (2012 -> 2015). Remember all the complaining from users when Win8 removed the start button and menu? You don't design a PC user interface people have been familiar navigating with since Windows 95 that is really more useful for touch screens, tablets, and smart phones.
20836228 said:Cpu fan wont turn on anymore and accidentally corrupted both cmos chips most likely and bricked the mobo. Please PM me or something if your a uber-techy and can provide me a potential solution.
Hi. I would suggest you start a new thread in the forums for any assistance for your issue. You will reach a wider audience who can possibly help.