WireLurker Marks New Era Of Malware In Apple Devices
Get Tom's Hardware's best news and in-depth reviews, straight to your inbox.
You are now subscribed
Your newsletter sign-up was successful
Researchers from Palo Alto Networks uncovered the largest malware attack against iOS devices, and the first attack of its kind to affect non-jailbroken devices on such a large scale. According to the report, there have been 467 infected Mac OS X applications that have been downloaded 356,104 times from the Chinese app store, Maiyadi, since March of this year. This malware is called WireLurker and is described as a "new era in OSX and iOS malware" by the researchers who discovered it.
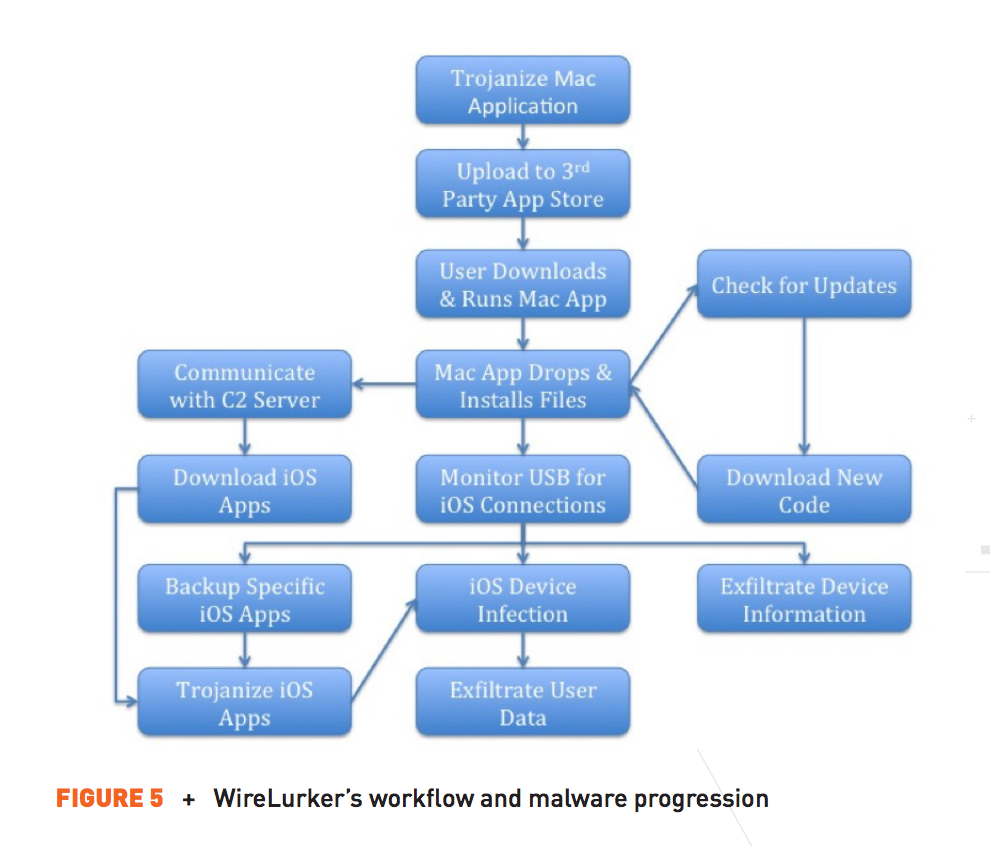
The way this malware works is by infecting users' Macs when they download an infected app from the Maiyadi app store and then connect their iPad or iPhone to the Mac through a USB cable.
After the two are connected, the Trojan installs infected iOS apps on the mobile devices through Apple's "Enterprise Provisioning Profile" feature, which is normally used by businesses to install apps on their employees' devices.
Article continues belowIn this case, however, the feature was used to allow the malware to bypass the iPhone or iPad's security. The user would still have to agree to use the app, but once he or she would click on "continue," the infected app would be installed.
"WireLurker is unlike anything we've ever seen in terms of Apple iOS and OS X malware," said Ryan Olson, Palo Alto Network's intelligence director."The techniques in use suggest that bad actors are getting more sophisticated when it comes to exploiting some of the world's best-known desktop and mobile platforms."
The researchers said that the malware was able to steal "a variety of information" from the mobile devices, including phone numbers from the Contact app and the user's Apple ID. The malware would also repeatedly make requests to the attacker's command-and-control server.
Apple has already issued a statement about this attack:
Get Tom's Hardware's best news and in-depth reviews, straight to your inbox.
"We are aware of malicious software available from a download site aimed at users in China, and we've blocked the identified apps to prevent them from launching," it said."As always, we recommend that users download and install software from trusted sources."
The bad news is that it seems Apple only blocked the infected apps, but at best that's a short term solution. Apple will need to send an update to iOS that further restricts the use of Enterprise Provisioning Profile in consumer iPhones and iPads so that the devices won't be able to install such infected apps anymore.
Because Apple doesn't have such a solution out yet, it's unclear whether this could fix the malware problem for the jailbroken devices, too. iOS devices that are jailbroken are usually much more vulnerable to infection because the user has administrator privileges, which means the attackers do, too.
To minimize the effect of this malware, the researchers who uncovered it recommended that the users:
Do not download Mac apps from third-party storesDo not jailbreak iOS devicesDo not connect their iOS devices to untrusted computers and accessories, either to copy information or charge the machinesDo not accept requests for a new "enterprise provisioning profile" unless it comes from an authorized party, for example the employer's IT department
The past few months have not been good to Apple from a security point of view. From the hacking of celebrity iCloud accounts, to having Chinese users' traffic intercepted by the Chinese government, to this rather widespread malware infection of non-jailbroken iOS devices, it's becoming clear that increasingly more attackers are attempting to infect or hack Apple devices.
Despite all of the security checks Apple has implemented in its hardware and software, it was only a matter of time before malicious hackers would turn their attention to iOS and Macs, given the rising popularity of these devices, globally. Apple may be able to fix these issues as quickly as they appear, but they can't put the cat back in the bag. More hackers have their eyes on Apple's devices now, and there's little doubt that there will be more such attacks in the future.
Follow us @tomshardware, on Facebook and on Google+.
Lucian Armasu is a Contributing Writer for Tom's Hardware US. He covers software news and the issues surrounding privacy and security.
-
vern72 I was just a matter of time. No system is completely secure (or else it would be unusable or useless).Reply -
Billzegun1 I think people are just trying to show that apple is just as vulnerable to viruses as windows.Reply
-
qlum TBH on windows at least they did make it really really easy to get virusses running during the xp era, nowadays its not that bad anymore although a lot of linux distro's are still far ahead of windows and ios is also more secure simply due to it forcing everything through their app store, sure not perfect but more secure then having open downloads and unlike linux not requiring a password for everything.Reply -
scolaner A few years ago, I spoke to a security researcher who debunked the "Apple is secure" myth. He basically said that it was just a matter of time...and that one of the reasons Macs hadn't been hit hard yet was a simple market share issue: It made more sense for malware makers to exploit Windows because it had a much larger footprint. More bang for their buck.Reply -
TeraMedia ReplyDo not connect their iOS devices to untrusted computers and accessories, either to copy information or charge the machines
"Hey - can I borrow your charger?"
"Wow, you've gotta try these speakers!"
I suspect that accessory-to-phone infection is limited to those devices that have some type of writable memory and/or built-in processor.
USB 4.0 spec needs a "power only" mode modification so that you can definitively disable unwanted data connections. -
Simon Ayres "This is not possible, Apple devices are immune to viruses"... *Points and laughs at every Apple support that has ever made this stupid claim.*Reply -
Simon Ayres "This is not possible, Apple devices are immune to viruses"... *Points and laughs at every Apple support that has ever made this stupid claim.*Reply