Software Bug Affected All Apple Devices
Kevin Backhouse, a researcher from U.S.-based security company Semmle, has uncovered six software vulnerabilities in Apple’s XNU operating system kernel, which is used in all of Apple's devices. The vulnerabilities have affected more than 1.3 billion devices worldwide.
According to the Semmle researcher, the critical vulnerabilities exist in the XNU kernel used by Apple’s iOS, macOS, tvOS and watchOS operating systems. Backhouse said attackers could use these low-level software flaws to take remotely control any Apple device on the same network.
The vulnerabilities exist in the kernel’s networking code and its client-side Network File System (NFS) implementation. The first vulnerability is a heap buffer overflow flaw in the ICMP packet-handling module of the XNU kernel’s networking code (CVE-2018-4407). An attacker could use this bug to run arbitrary code on a user’s machine, extract data, or cause a reboot.
Article continues belowBackhouse also warned that because the flaw can be so easily exploited, it could be automated as a denial-of-service attack, which may then crash all affected devices on a network, potentially shutting down an entire organization. User interaction is not required for attackers to be able to take advantage of this vulnerability.
The five bugs the researcher found in Apple’s NFS implementation could also allow attackers to read, write and delete files on a user’s NFS-mounted drive, as well as install applications or wipe the device entirely. The NFS implementation bugs primarily affect macOS machines.
Disclosure and Mitigation
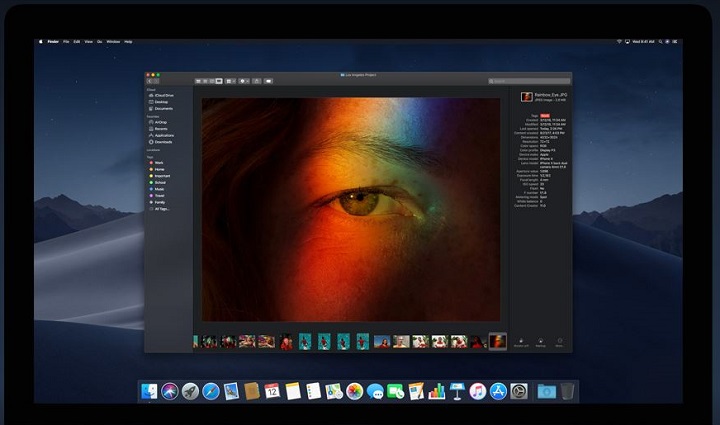
Backhouse discovered the vulnerabilities as part of his work for Semmle. He privately disclosed the ICMP packet handling vulnerability to Apple on August 9, and Apple acknowledged the security issues the same day. Apple also released patches for iOS 12 on September 12 and for the Mojave macOS edition on September 24.
Backhouse told Apple about the NFS implementation vulnerabilities in May, and Apple fixed those vulnerabilities in macOS version 10.13.6 on July 9.
Get Tom's Hardware's best news and in-depth reviews, straight to your inbox.
Apple made all the vulnerabilities public on October 30. However, Backhouse also noted that only 60 percent of iOS devices have implemented the iOS 12 update, which means a large portion of Apple customers are still affected by some of these bugs. If you haven’t updated your Apple devices to the latest version yet, it may be time to do that.
Lucian Armasu is a Contributing Writer for Tom's Hardware US. He covers software news and the issues surrounding privacy and security.
-
bit_user Correct me if I'm mistaken, but it doesn't seem like this should affect devices that don't have any NFS volumes mounted. Otherwise, I don't see why the NFS client would be active.Reply
For their portable devices, it would seem the exception that they'd ever be using NFS shares.
In other words, I think the practical scope of this vulnerability might've been overstated.