Backdoored Automatic Updates Amplify NotPetya's Destruction
Get Tom's Hardware's best news and in-depth reviews, straight to your inbox.
You are now subscribed
Your newsletter sign-up was successful
According to ESET, and later confirmed by Cisco’s Talos threat intelligence division, NotPetya installed backdoors in a popular accounting software in Ukraine, M.E.Doc, through which it managed to infect the systems of over 2,000 Ukrainian companies. This feat shows that although automatic updates are generally beneficial, unless a vendor takes great care in securing its servers, they could also prove to be catastrophic.
NotPetya’s Attack Vectors
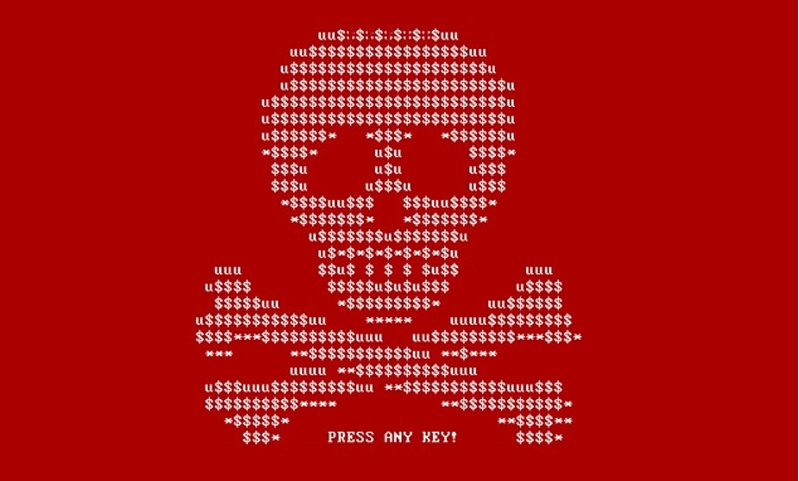
NotPetya--or Nyetya, as it was nicknamed by antivirus companies after they discovered that it wasn’t in fact the original Petya ransomware--has infected thousands of Ukrainian companies or multinationals with operations in Ukraine.
The NotPetya "ransomware" later proved to be a destructive malware that asked for ransom mainly as a distraction from its real objectives. It used multiple attack vectors, including the Windows SMB protocol and NSA’s EternalBlue exploit tools, just like the WannaCry ransomware before it.
Article continues belowInfecting M.E.Doc Accounting Software
The ESET security researchers found that the malware authors had an even better way to spread NotPetya to thousands of companies. They hacked the M.E.Doc update servers and then put in a backdoor through which they could later push the NotPetya malware to the systems of thousands of companies using the M.E.Doc accounting software.
According to ESET, backdooring M.E.Doc shouldn’t have been possible without the malware authors first having access to the M.E.Doc source code. This likely means that the malicious actors had previously stolen that source code from other servers belonging to the makers of the M.E.Doc software.
Fully-Featured Cyber-sabotage Platform
The backdoored version of M.E.Doc was also able to collect the Ukrainian companies’ legal entity identifiers, called EDRPOU numbers, as well as proxy and email settings, including usernames and passwords. The attackers also added the ability to control the infected machines remotely, making the malware a “fully-featured cyber-espionage and cyber-sabotage platform” at the same time.
ESET said it couldn’t verify at this time whether or not there are other backdoors in the 1.5GB M.E.Doc accounting software, as the source code is quite large. It also couldn’t say for how long the backdoor has been in use. The security company recommended M.E.Doc users to change their proxy and email passwords immediately.
Get Tom's Hardware's best news and in-depth reviews, straight to your inbox.
Dangers Of Malicious Automatic Updates
The M.E.Doc accounting software uses automatic updates, which made the backdooring of the software so much more dangerous, because it allowed NetPetya to quickly spread to thousands of companies.
Auto-updates are generally considered a security feature, because they remove much of the delay between when a security patch is released of and when it's actually installed by all the people who use that particular software.
We can see how ransomware makers continue to abuse the SMB vulnerability in unpatched Windows systems, despite the fact that Microsoft started issuing a patch for it months ago. When the updates are not automatic, a large portion of the users tend to postpone them for whatever reason. However, once Microsoft announces patches for some bugs, the malware makers also know which bugs to use to spread their malware on unpatched systems.
The problem with auto-update systems arises when software vendors with millions of users, and with a target painted on their backs by hackers, don’t take good care of their servers’ security. When updates are manual, even if the servers are hacked, that delay until everyone patches could be used to the users’ advantage, because during that time, the hack may be discovered. Therefore, many users may never be affected by the backdoored update.
If more of this type of attack continues, people may start losing faith in automatic updates, such as those seen in Chrome and Windows 10. The NSA, which had previously hijacked Windows’ update system to spread the Flame cyber-espionage tool, has also been a proponent of malicious automatic updates as a way to bypass encryption. However, as security experts have warned, if this ever came to pass, even more people would disable auto-updates. That could further put their own security at risk.
There is no easy solution against malicious updates in general, because this “comes with the package” when using a digital service or product. When you use an online service or product you’re always at risk of having your data stolen, which is why choosing companies that prioritize security is always a good idea. As for the avoid automatic malicious updates, the solution could be to disable them, but then you may be exposed to other attacks, so this solution would at least need some serious consideration.
Lucian Armasu is a Contributing Writer for Tom's Hardware US. He covers software news and the issues surrounding privacy and security.
-
redgarl Auto-update... My Aetheros Lan driver is making my Windows 10 systems crash. Everytime I desinstall the driver, Windows 10 resinstall it back at every reboot. This nonsense needs to stop! I should be able to install the updates that I want since many are useless junk.Reply -
popatim Automatic updates have always been used maliciously. Just look at how many times Adobe Reader and java auto updates have been intercepted and used as an easy attack vector.Reply -
derekullo Windows 10: I'm sorry, Redgarl. I'm afraid I can't do that.Reply
Windows 10: This mission is too important for me to allow you to jeopardize it. -
ledhead11 My like of Windows 10 has been dying by the microsecond for the last six months. I'm, glad I have a legitimate pro edition disk of 7 still hanging around. That being said, all software or OS is vulnerable to this when the root vendor servers are not properly protected. Why corrupt a vulnerability in the masses when the source can be the target? Although convenient now, avoiding 10 and others is short sighted in relation to the true threat of this strategy. It doesn't matter what OS or software you use, if anything is left to auto-update you should be concerned.Reply -
FunSurfer Companies that issue Auto Updates can create a "Checksum" to an update and send it through a second channel like an email. The installer will run the Checksum test before installing the update and if the result doesn't match the original the update is corrupted.Reply