New LastPass Bugs Could Have Been Used To Steal Users' Passwords
Tavis Ormandy, one of the security researchers from Google’s “Project Zero” group, has been looking for (and finding) vulnerabilities in popular password managers for the past few months. He recently found a new bug in LastPass’ extension that would have allowed attackers to steal any of your passwords saved via the service. Another similar-but-different bug was also reported in the utility's Firefox add-on.
Password Manager Security
Security experts generally recommend password managers, not necessarily because they’re an ideal way to deal with passwords, but because they’re the best way to deal with them without re-using the same password on multiple sites. Re-using passwords seems to be a much bigger risk than keeping all of your passwords in a password-protected and encrypted vault. Plenty of data breaches or account hacks have showed the risk of password reuse.
As an example, your Gmail password may be safe on Google’s servers, but if you use the same password for another website, and then that website is hacked, the attackers could log in to your Gmail account. Gmail's servers were secure the whole time, but that didn't matter in the end, because the attacker was able to obtain that same password from a much less secure website.
Article continues belowPassword managers may be of great help in such situations, but they are not without risks, either. For instance, password managers that use browser extensions can more easily be attacked remotely, through the browser.
Syncing your password vault with an online server comes with its own risks, too, compared to using a local vault such as those provided by KeePass or KeePassX (two applications recommended by Ormandy). It gives attackers the opportunity to brute-force your master password and login to the vault.
LastPass’ Latest Vulnerabilities
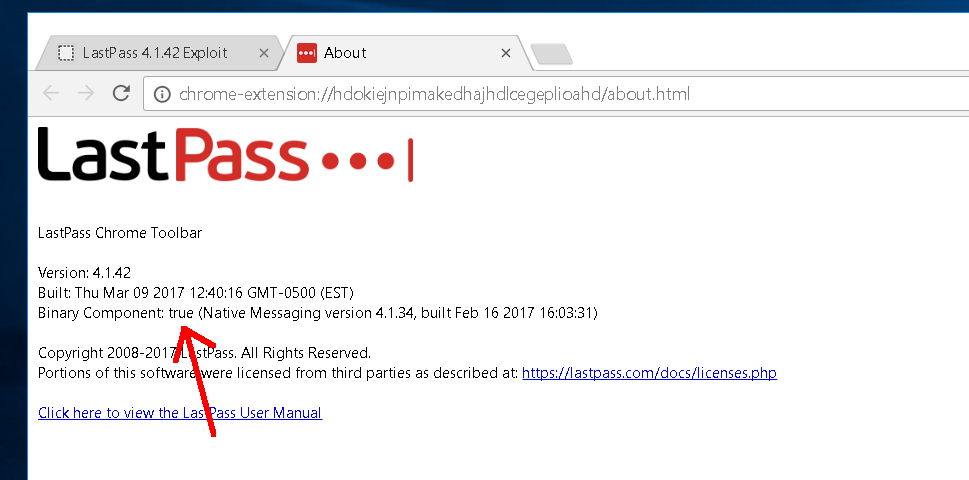
The flaw that Ormandy discovered on March 20 in the LastPass Chrome extension (version 4.1.42.80) was found in an intermediary JavaScript script that stands between the browser extension and LastPass’ cloud service, where your password vault is stored. This bug could allow an attacker to steal your passwords as the vault is accessed.
If you had the “binary component” installed, it would have allowed arbitrary code execution, too. The binary component for the LastPass browser extension contains additional convenience features such as enabling fingerprint authentication support, exporting and importing data, and much more.
Get Tom's Hardware's best news and in-depth reviews, straight to your inbox.
Ormandy put together a proof of concept in which he showed that the “calc.exe” application could be started remotely on Windows via that LastPass extension vulnerability. According to a recent LastPass post, the bug affected all versions of the extension (Chrome, Firefox, Edge, and Safari). The company said this bug was addressed--apparently via workaround, rather than a complete fix--hours after it was reported.
Another vulnerability was reported for Firefox on March 21. This bug seems to affect version 4.1.35a of the Firefox extension, and the company said the flaw is “largely the same” to the one reported the previous day. However, instead of addressing the Firefox extension's issue via the same workaround used for the previous bug, LastPass decided to wait until a full fix was ready. The company said it released version 4.1.36a of its extension for Firefox to fix the reported issue at 12:15am ET today.
LastPass added that it has no knowledge of the vulnerabilities being exploited in the wild and that it plans to release a more comprehensive summary of the events soon.
Lucian Armasu is a Contributing Writer for Tom's Hardware US. He covers software news and the issues surrounding privacy and security.
-
velocityg4 You want a bigger bug I've mentioned to them. By default the password manager stays signed in. Rather than automatically signing out after inactivity or closing the web browser.Reply
For the average user this negates much of the security as anyone who has access to the computer has access to the passwords. Sure you can say that they can change the settings. The average user won't think to do that. Just getting them to use it successfully is a feat.
There is a huge gulf between people that understand tech and those that don't. Most tech companies don't grasp this. What seems like a very simple concept to a technically minded person is fraught with complexity for those whom don't get it.
Leaving a huge hole in the security like this and giving them the option to fix it themselves means it will never be fixed. They may as well just leave a piece of paper taped to their wall with a list of passwords. Which I see a lot. -
therealduckofdeath By default, LastPass does not stay signed in. In fact, LastPass gives you a double pop-up "are you sure you want to do this?" question when you tick the "always signed in" box.Reply
I've used LastPass Premium for a couple years now, and it is a really stable and truly platform agnostic service. It works as good on my Android as it does on my desktop and my Microsoft Surface. They have also been really quick with fixing issues reported, like the one in the article above. -
ddpruitt Been using LastPass for a few years. Tried KeePass but it won't do the job, I need to be able to sync across devices and LastPass does that without the extra hassle of needing to login to one app to sync keyfiles, open the updated keyfile and then finally loggin.Reply
They're also probed regularly and have a fast security fix response time. -
alextheblue Reply
This black box is more secure than this other black box! Because they told me it was.19462099 said:That's why I switched to Enpass, much much safer.