Researchers Find Zero-Day Bugs That Could Allow LastPass Password Theft
Both Google’ Tavis Ormandy, who works on Project Zero (a project meant to find zero-day vulnerabilities in other products), and Mathias Karlsson, an independent researcher, have found vulnerabilities that could allow others to gain access to users’ LastPass passwords.
LastPass is one of the most popular password managers out there that allows users to generate strong passwords for any website they want, as a way to avoid re-using passwords that could otherwise be easily bruteforced.
Password managers are currently the preferred secure way to create passwords online, something that’s also recommended by most security experts. However, password managers also have one potentially large weakness, and that’s the fact that if your master password is leaked, then all of your other passwords will be, too.
That’s why it’s important to use both a strong passphrase (as the master password for the password manager) and two-factor authentication (preferably not SMS, though) to minimize the risk of attackers gaining access to all of the sites where you’re registered as a member.
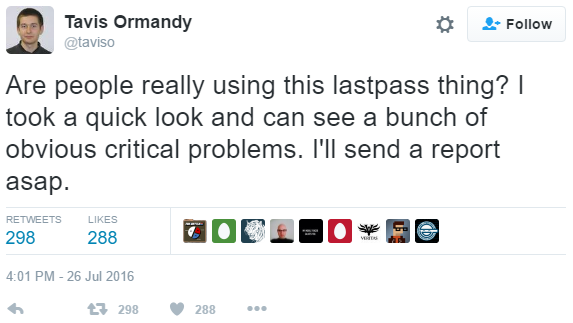
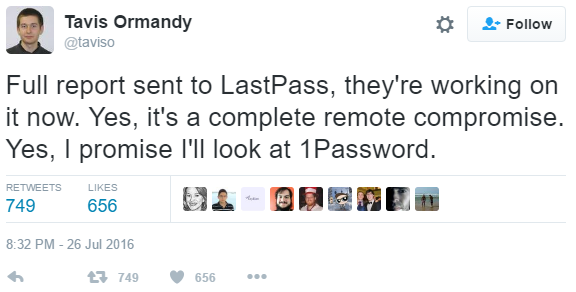
Tavis Ormandy, who has found and has written about multiple zero-day vulnerabilities in various products, seems to have found a remote compromise of LastPass’ password database and has already alerted LastPass about it.
Mathias Karlsson, an independent security researcher, seems to have found what is likely to be a different vulnerability, considering he has already reported it to LastPass and the company pushed the fix within a day.
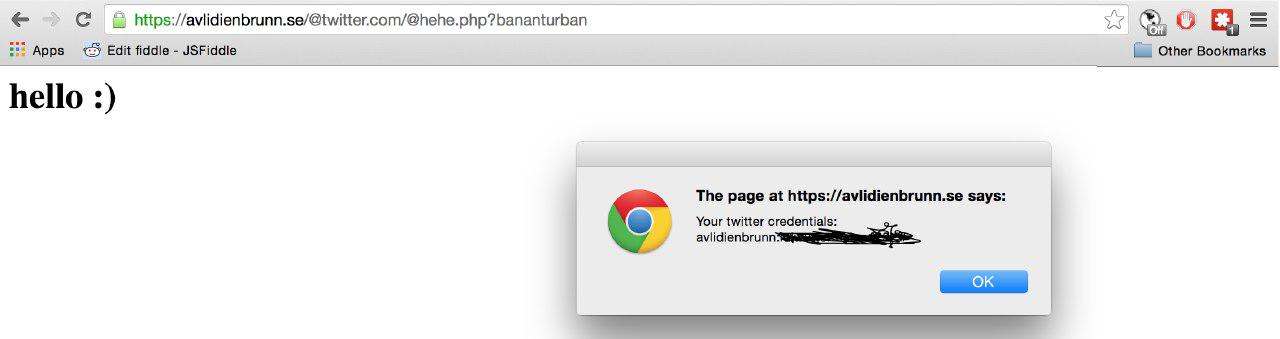
Karlsson claimed that the bug he found in LastPass’ browser extension had to do with the autofill functionality and the flawed parsing of the URL. For instance, if he had tried to access the link (http://avlidienbrunn.se/@twitter.com/@hehe.php), the LastPass extension would think the site to which he’s trying to log in to is twitter.com rather than avlidienbrunn.se. Then he could extract the credentials for twitter.com, and he could use the same tactic to get the credentials for other popular sites, too, due to the bug in the autofill functionality.
Get Tom's Hardware's best news and in-depth reviews, straight to your inbox.
Karlsson still recommended using password managers over re-using a simple password, but he also said the autofill functionality should be disabled, as there have been other issues in the past with it, as well. He also noted that if multi-factor authentication had been enabled, this flaw couldn’t have been exploited.
Lucian Armasu is a Contributing Writer for Tom's Hardware US. He covers software news and the issues surrounding privacy and security.
-
ddpruitt "Are people really using the lastpass thing?"Reply
Doesn't sound like anyone who knows about security to me. A quick web search through the company he works for would reveal all.
It's scary how many companies don't implement two factor authentication, I have it enable for everything possible. For something that's universally agreed to severely cut down on hacking and phishing attempts this is stupid. Companies are required by law to protect certain pieces of information, they should also be required to enable two factor authentication.