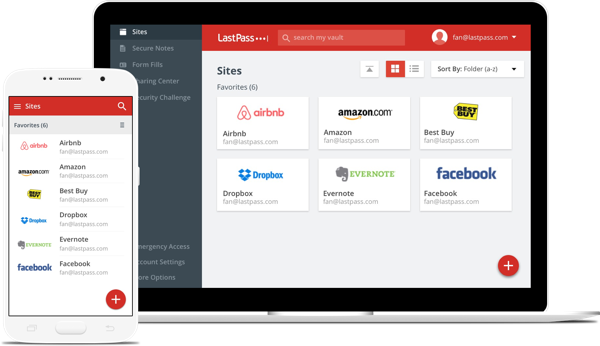
LastPass Becomes Free On Mobile, Eliminates Last Excuse For Not Using A Password Manager
LastPass, the most popular cloud-based password manager, was free for desktop but still required users to pay if they wanted their password to sync with their mobile devices. This likely turned away many users from adopting a password manager.
The company announced that the mobile versions of its password manager are now also free. Users should now have few excuses left for not using a password manager to protect their online accounts from getting hacked.
Security experts have rated password managers as one of the best ways to keep your accounts for various services secure. Too often, when millions of users’ credentials are leaked online, researchers then discover that a big portion of the users were using short and simple passwords to secure their accounts.
Article continues belowThese passwords can not only often be guessed by the attackers by looking into their targets’ past, but they can also be trivially broken with modern password cracking tools.
Short Passwords Cause Large Data Breaches
There are multiple reasons why people use such short, simple passwords. For one, they are afraid they might forget them, so they choose something simple that’s easily remembered.
Another reason is that they have to log in to dozens of websites and accounts these days, so they choose two or three simple passwords and re-use them across all of those sites. This also means that if only one of those websites is hacked, multiple other accounts may become compromised as well.
Another reason why people choose short passwords is because they don’t realize how advanced password cracking tools are these days. Many still believe that the only threat is the attacker “guessing” their password, when in reality the attackers would test millions of such short passwords in minutes.
Get Tom's Hardware's best news and in-depth reviews, straight to your inbox.
Password Managers To The Rescue
Password managers completely eliminate the above problems by generating long and unique passwords for each of your accounts. On average, it should make users (especially those relying on short passwords for multiple sites) much safer, which is why most security experts think so highly of this type of security tool.
A recent NIST study also talked about computer users’ “security fatigue,” mainly related to the fact that sometimes, in enterprise situations, users have to work with dozens of passwords. A password manager (with the appropriate security precautions) could solve that issue as well.
“So far in 2016, there were more than 1 billion passwords publicly leaked due to poor password practices,” said Joe Siegrist, LastPass’ Founder, in a blog post.“We want to empower our users to take back control of their online security, and no longer feel powerless against the next wave of breaches. The more convenient we make password management the better we will be able to solve this problem. We want our users to bring LastPass with them everywhere – including the workplace because accessing the sites, apps, and services you use every day doesn’t end because you checked in at the office,” he added.
Password Manager’s Weaknesses
However, password managers also pose a couple of major risks. One is that you have to trust it (at least a “cloud-based” manager such as LastPass that can sync your passwords across devices) to properly encrypt your passwords end-to-end, so that only you can have access to your own password database.
LastPass’ security architecture seems to do exactly that, and until malicious intent is proven, it can likely be trusted to keep its users’ passwords safe. Much like a certificate authority, user trust is all a cloud-based password manager company really has. If that trust is somehow broken, the company could risk a user exodus, and then bankruptcy.
Security-minded people are highly sensitive to such issues. Sometimes, even an acquisition can cause an uproar, because users are unsure whether the company still deserves their trust. In such cases, the companies need to properly reaffirm that they’ve committed to maintaining that user trust.
However, if you still don’t trust cloud-based password managers such as LastPass, Dashlane or 1Password, then there are still open source password managers for the desktop such as KeePass and KeePassX. You can also use these open source tools on mobile, but you’ll have to handle your own password syncing by importing the password databases into compatible apps.
Protecting Your Master Password
The second major potential issue that one could have with a password manager is getting your master password hacked or stolen. Once you start using a password manager, the master password for the tool is the only password you’ll ever need. Therefore, you should make sure it’s a solid one. You don’t want it to be easily broken by cracking tools.
A long, unique master password isn’t enough, so you’ll also want to use two-factor authentication to log in to LastPass or other similar services. Ideally, you should use a Yubikey or fingerprint/smart card, but Google Authenticator or the company’s own LastPass Authenticator could work as well.
It will probably be at least a few years until most users will be able to use fingerprint authentication to log in to websites, and not just unlock devices. However, even when biometric authentication is standard on all devices, people may still have good reasons to prefer strong passwords over those methods. Password managers can be almost as easy to use as biometric authentication, while ensuring that if an account is broken because of a company's bad security practices, you can still generate a new password. This "feature" is much more limited in the case of biometric authentication, because you only have so many fingers or eyes that you can use when your biometric data is stolen.
Lucian Armasu is a Contributing Writer for Tom's Hardware US. He covers software news and the issues surrounding privacy and security.
-
kennysmoothx I personally use 1Password, it's about $2 a month, and I honestly couldn't go back.Reply
Took me a while to switch to a password manager but I'm really glad I did, lets me login to sites quicker than before yet with unique long password. -
owens This was great news until I went back and re-installed the app on my phone thinking it will now be free to use...Reply
Nope!
You still have to get a premium subscription to SYNC your passwords between desktop and mobile devices if you have an existing account.
What this article fails to mention is you can now use the mobile app for free, BUT you have to get a new account, and your passwords will only be synced to mobile devices. Your passwords stored via the mobile app won't sync to the PC version.
More explanation here:
http://www.makeuseof.com/tag/lastpass-is-now-free-on-phones-but-theres-a-catch/ -
velocityg4 The main problem for password managers is they are too difficult to use. For the average user.Reply
Some websites won't auto fill and you have to manually tell the manager to fill the login. Even worse is when you have to find the password then copy and paste or even manually input.
As for remembering passwords. Sometimes they won't recognize you created a new login and have to input it manually. It will save the wrong info or not update a changed password.
Another issue is password rules. I can see there being different minimums. All websites should allow letters, numbers, uppercase, lowercase, all special characters and no maximum. That way you can easily auto generate secure passwords.
Until they can make at least the detection, auto fill, save and updating consistent. People will shy away from password managers.
Many techies don't understand how the average user uses a computer. When they do something they don't understand what they did to accomplish a task. They just memorized a procedure. Even a slight change causes them a lot of problems. -
randomizer Reply18816451 said:More explanation here:
http://www.makeuseof.com/tag/lastpass-is-now-free-on-phones-but-theres-a-catch/
So basically if you want to use it on the desktop and your mobile devices nothing has changed. -
drajitsh I agree with velocity. Most banks do not allow auto fill and right click is universally disabled on financial sites (though they do allow ctrl+V in some situations). with separate password rules for each site + manual entry of passwords with time out when redirected from merchant sites, password managers don't make sense.Reply -
Yuri_6 After years of using lastpass- I did the unthinkable and managed to botch up a master password change. None of the techniques for recovery worked either so I was forced to start over.Reply
Thing was, I am a chrome user and noticed chromes Google Smart Lock technology was offering to save nearly every password lastpass was. In the back of my head I was always thinking- this is free across all platforms that chrome is on, maybe I should just standardize on this- I certainly trust google's infrastructure more than lastpass.
So... I've now been using chromes Smart Lock for several months now and couldn't be happier. Works every bit as well as lastpass premium, syncs across all my devices and is free. -
kspearrin If you're looking for a truly free, open source alternative, check out https://bitwarden.com. I switched from lastpass and haven't looked back.Reply -
WhiteCake There's also Encryptr. It's free, syncs across all devices.Reply
I'm hoping they implement 2FA with yubikey in the future -
hjfsdhg4g ReplyMore explanation here:
http://www.makeuseof.com/tag/lastpass-is-now-free-on-phones-but-theres-a-catch/
No this is how it was before but a few days ago they made it truly free which is what this whole news post is about.
https://blog.lastpass.com/2016/11/get-lastpass-everywhere-multi-device-access-is-now-free.html/