Macate 'Cyberphones' Promise Unspoofable Face Recognition, Other Security Measures
Get Tom's Hardware's best news and in-depth reviews, straight to your inbox.
You are now subscribed
Your newsletter sign-up was successful
Issac Daniel is paranoid. So are some of his entourage, which included at least two PR personnel and a security detail.
We met with Daniel and his team at a restaurant in Las Vegas during CES 2016 to talk about his company, Macate, and the security technology they’re building into smartphones. Originally, we gathered in a lounge area outside the main sitting area, but we were awkwardly and suddenly ushered into a booth to the back of the restaurant.
One of the PR people apologized, but noted that someone had apparently been shadowing Mr. Daniel that day, so they were taking precautions. (I wondered if perhaps it was time to bail on this particular meeting, but I was intrigued, so I stayed. Were those guys at the next table part of the security detail? They were shooting furtive glances our way. The PR folks seemed to know them, though. Hm.)
Article continues belowBackground
If Daniel’s stories are true, though, he has reason to be paranoid. He said that in 2000, when he was working on GPS technology, his son was kidnapped. He realized that if he had a hidden GPS chip on the boy, he could have easily tracked him, and so he developed a GPS chip designed for shoes.
He said that by 2005, the U.S. government wanted to talk with him about his technology, and his portfolio evolved from there into cybersecurity.
Today, Macate has created so-called “cyberphones” that are designed to offer the best security around. It is true that smartphones are too often an easy target for theft and are usually major security vulnerabilities for companies, governments and individuals alike.
Get Tom's Hardware's best news and in-depth reviews, straight to your inbox.
“Your mobile phone is your partner for life,” he said. “But we leave our phones vulnerable.”
What Are You Making?
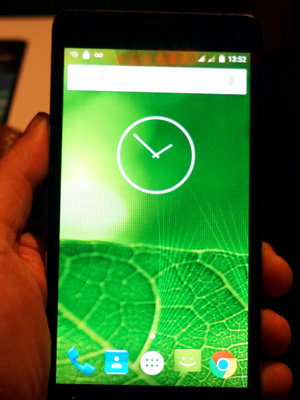
It took a rather long while in our meeting for me to understand what Macate actually wants to make. (Spoiler: On-chip security technology for smartphones.) Daniel and Co. first showed us a series of “high-end” smartphones that Macate makes.
There’s the Gatca series, which includes the Gatca 3, Gatca 4/4+ and Gatca Elite ($850), as well as the premium Belici. They all run Android 5.1, but Daniel said that an Android 6.0 update was in the offing.
| Header Cell - Column 0 | Gatca 3 | Gatca 4/4+ | Gatca Elite | Belici |
|---|---|---|---|---|
| SoC | MT6582M 1.3GHz Quad Core | MTK6735P 1.0GHz Quad Core | MT673 1.3GHz Quad Core | -- |
| Display | 5-inch qHD screen, 1280x720 | -5.0-inch HD IPS (1280x720) -5.5-inch HD IPS {1280x720} | 5.5-inch IPS, 1280x720 | 5.0, 1280x720 |
| RAM | 2 GB | 2 GB | 2 GB | 2 GB |
| Storage | 16 GB (up to 32 GB microSD) | 16 GB (up to 32 GB microSD) | 32 GB (up to 32 GB microSD) | 32 GB (up to 32 GB microSD) |
| Camera | Rear: 8MP (AF)Front: 5MP (FF) | Rear: 8MP (AF)Front: 2MP (FF) | Rear: 13MP (AF)Front: 5MP (FF) | Rear: 8MP (AF)Front: 5MP (FF) |
| OS | Android v5.1 | Android v5.1 | Android v5.1 | Android v5.1 |
| Sensors | Light, Gravity, Proximity | Light, Gravity, Proximity | Light, Gravity, Proximity, Biometric | Light, Gravity, Proximity |
Daniel carries Macate’s second-highest-end model, the Belici, a “luxury” device. However, they showed us an even more high-end version of the Belici that’s completely coated in 9 karat gold.




I asked why there were showing us these smartphones if they ultimately aren't interested in being a smartphone maker, and the answer was essentially that they wanted to show that stylish, high-end smartphones for stylish, high-end people whose information and secrets are the most valuable (heads of state, celebrities, company CEOs) should come with robust security.
That’s a fair point. Given the choice between stealing my phone or a senator’s phone (or a Kardashian’s phone for that matter), one is obviously a juicier target than the other.
How It Works (Sort Of)
Codetel is technology that works on-chip, so Macate should, more than anything, get in tight with chipmakers. Indeed, the version we saw in our meeting was built using a Mediatek SoC (they would not reveal which one). That works fine for some Android devices, but Macate wants to get the attention of Apple and Qualcomm to get onto iPhones and so many other smartphones, too.
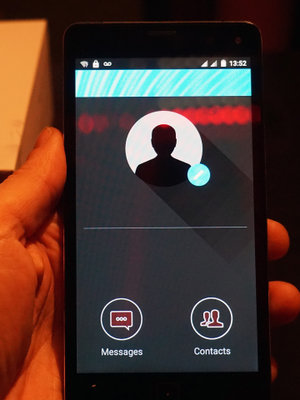
Codetel is bolstered by face recognition technology called TrueFace. To authenticate the phone, you hold it up to your face, like you’re taking a somewhat close-up selfie. The device’s camera captures your face, and the on-chip magic compares that to an image (stored in the cloud) and determines that it’s you. According to Daniel, the technology can recognize you even if your facial hair or glasses change, because it truly “looks” at your whole face and maps it. Setting up the authentication is apparently a swift and painless process, too.
The facial mapping was built by Macate; the algorithm belongs to someone else, but Daniel would not say who created it.

With your face recognition data stashed beneath even the OS, no one can grab your phone and run away with it unless they want to own a paperweight. Ostensibly, the encryption will prevent anyone from hacking the phone. Codetel supports up to 512-bit AES encryption (although it will use 128- or 256-bit depending on local laws). More importantly, though, if anyone removes the SIM card, it will brick the phone.
This has obvious pros if you’re worried about thievery, and obvious cons if you just want to swap out your SIM card. However, Daniel explained that to un-brick the phone, all you (the authenticated user) has to do is pop it back in and use your face to restore everything to normal.
Face...Off?
For a few paragraphs now, you’ve probably had the same burning question I had, which is what happens when someone 1) forces you at gunpoint to log in, thereby acquiring access to everything on your phone or 2) just uses a nice telephoto lens to snap an image of your face to spoof the system.
To the first point, you’re mostly out of luck (although a feature I’ll get to in a moment can ameliorate that problem to an extent). However, that’s no different than any other heist or theft where if one has the “keys” -- whether that’s actual physical keys, a thumbprint, an iris, or a whole face -- one has access.
To the second point, I pressed Daniel on that, but he was adamant that you simply cannot spoof TrueFace with a photo. I remain skeptical of this claim. The device uses a camera to “see” your face, and that camera has certain limitations; if TrueFace has no trouble recognizing you regardless of changes in facial hair and glasses, why would it have trouble recognizing you from a photo? Bear in mind that this security solution does not make use of thermal imaging or depth; it uses the regular camera on your phone.
What it came down to is that Daniel would not elaborate on this claim further because it would reveal trade secrets. Therefore, at best you’ll have to take him at his word (or don’t) that spoofing is impossible.
Geo Locking
One feature that Daniel did elaborate on is Geo Locking, which uses GPS to “lock” certain content on the device to a specific location. You could, for example, lock photos you take of your kids to your home and keep any work files locked to your office location. It’s an added layer of security.
The idea is that even if someone were to get their hands on your phone and somehow unlock it, they wouldn’t be able to see everything stored on the device. Let’s say you left your phone in a taxi and someone found it and managed to crack it; unless that person physically went to your office, they couldn’t see that snapshot you took of a prototype you’re working on in the lab, even though the photo is stored on the device itself.
Plans
Macate is working on the necessary partnerships to get Codetel and TrueFace onto other companies’ shipping products. As I mentioned earlier in this article, this is on-chip technology, so Macate will need the buy-in of chipmakers before it can make significant progress -- or you can choose one of Macate’s own “cyberphones.”
Seth Colaner is the News Director for Tom's Hardware. Follow him on Twitter @SethColaner. Follow us on Facebook, Google+, RSS, Twitter and YouTube.
Seth Colaner previously served as News Director at Tom's Hardware. He covered technology news, focusing on keyboards, virtual reality, and wearables.
-
Urzu1000 Most of this sounds pretty "meh", but that geo-locking feature isn't a bad idea at all if they can implement it well enough.Reply -
WFang I bet at least part of the 'can't use photo' feature involves comparing multiple rapid succession images. Most people have subtle and not so subtle facial changes (eyes blink, nostrils flare/move, lips move) that would be hard to fake by twitching or vibrating a photo. The next natural choice would be a video, but screens have a different set of features, moire patterns, glare, etc. That said, if I needed to crack one, I would probably start out with high-res video of the 'key' person and work on playback device and environment to reduce/eliminate tell-tale signs that the phone camera was looking at a screen... it may still not work, after all this is what i came up with from a 3 minute think about it, these guys presumably have spent years working to make this as safe as possible and probably have additional tricks up their sleeve...Reply -
spiketheaardvark I thought part of reason Intel's real sense could use infrared and 3D was to solve the picture spoofing problem. Just the 3d camera part makes it much harder to spoof the camera and infrared images look much different than visible light and not easily replicated. I've read they can reliably distinguish identical twins. I'd be surprised if these guy weren't using similar methods.Reply
-
alidan so, facial recognition for the phone...Reply
you have just been beaten half to death for your money, they left the phone because it wasn't an apple or other known expensive product, you want to call for help, it tells you "you're not my owner" and will not activate.
yea... i don't want retinal scanning, fingerprint, or facial, even voice, all of these things can easily get messed up or change just enough to lock you out of something important.
i don't want fingerprint scanning in fear of a mugger deciding it would be a good idea to take a thumb too, retna... that is an even scarier prospect. face i doubt someone would try to steal, but i have seen enough people get messed up to the point you couldn't tell who they are anymore (to be fair i have seen people get punched in the face and everyone around me tells me "look how bad they are swelling" but i cant tell a difference) and a fingerprint... how many of us have cut our thumbs or just any finger, you really want that locking you out if lets say you were in an accident? -
canadianvice Most impressive. The moment any security solution promises "-proof", they're out the window - because anyone who actually understands security knows nothing is "-proof".Reply

