Phishing for Crypto: Half a Million Dollars Stolen Via Google Ads Exploit
Triple-check web addresses, all the time.
Cyber threat analysis firm Check point Research (CPR) has issued an alert regarding a recent phishing campaign mainly targeting Phantom and Metamask users. The threat makes use of Google Ads to bump fake websites in search results, meant to prompt users to provide their keys or make new wallets on behalf of bad actors. It's currently estimated that half a million dollars have been diverted from their legitimate users' wallets. Due to the nature of the attack being carried out during the (supposed) wallet creation process, new entrants to the crypto space are likely to be the most heavily affected.
As with all high-coverage threats to cybersecurity, bad actors focus their efforts on platforms that are most popular - as the number of potential victims increases, so does the potential return. Metamask and its 10.35 million peak users (as of August 2021) represents a sizable target for this phishing effort; the same is true for Phantom, which has already registered a million users since its introduction. The method seems to rely on the fact that these platforms make use of browser plugins as a facilitator. But beware: other DeFi apps like Sushiswap and Cakeswap are also popular victims of this sort of malicious behavior for similar reasons.
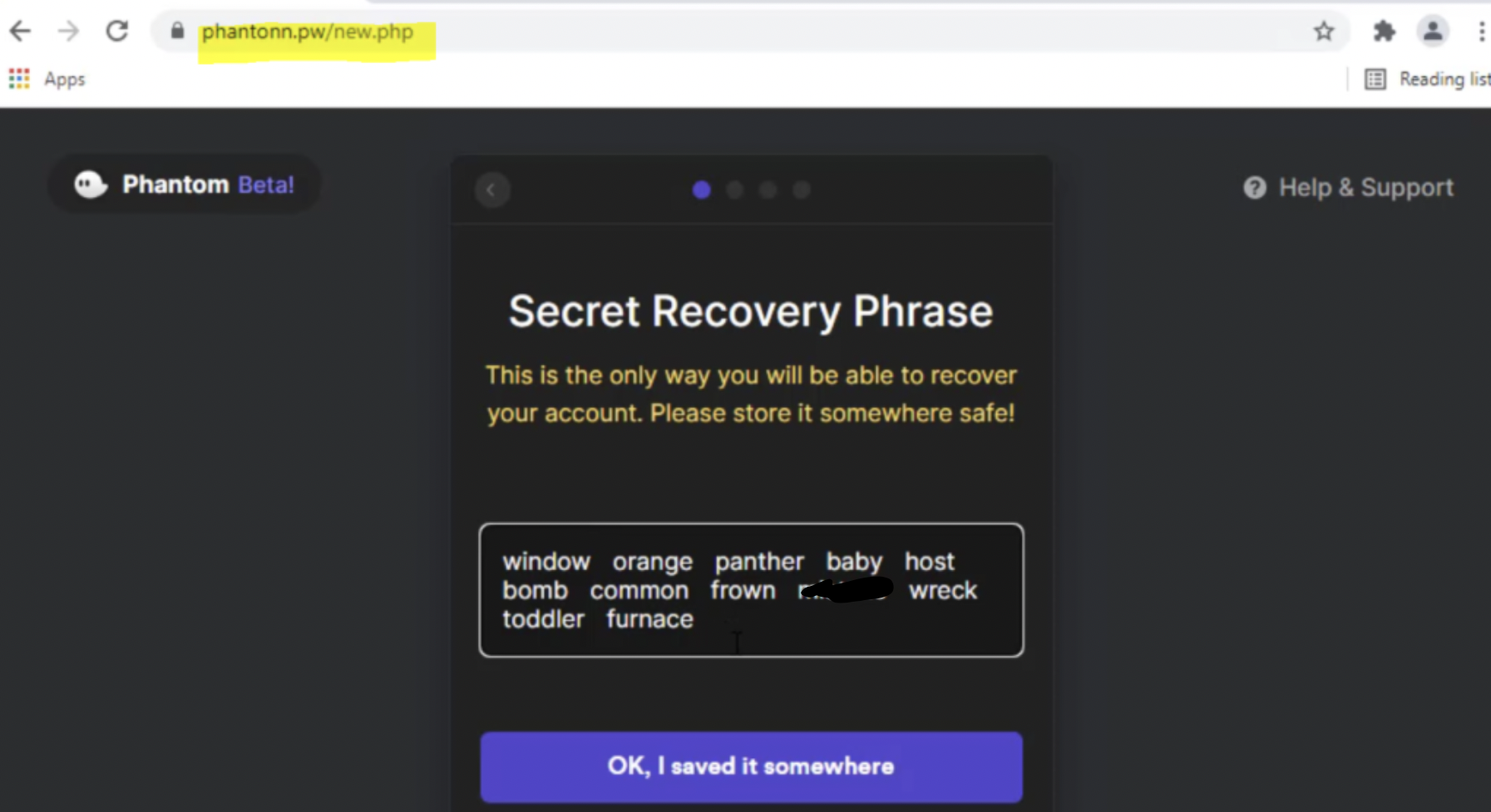
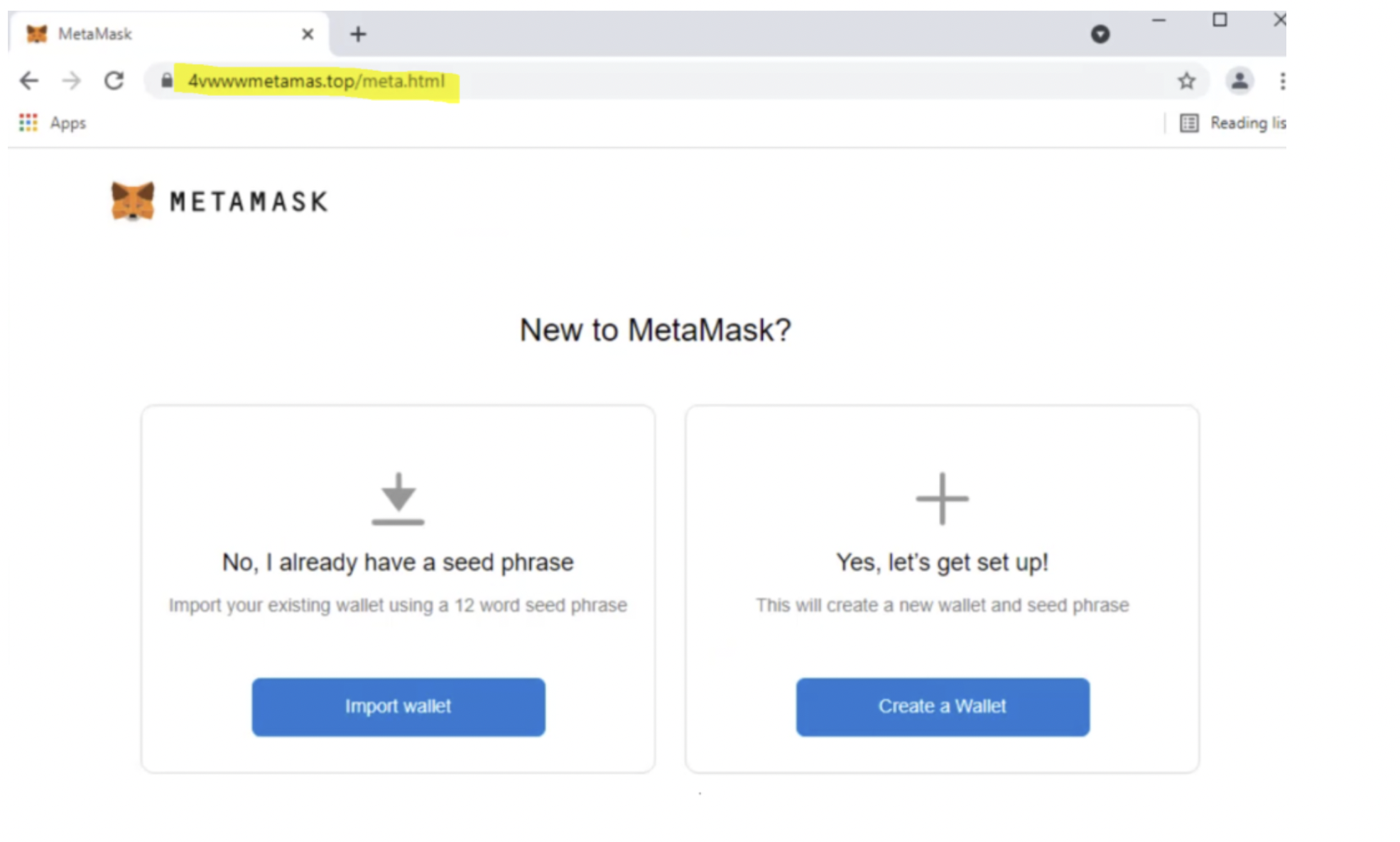
After erroneously clicking the top search result, users are then sent to a phishing website, which hides in plain sight by introducing a very minute change (such as phantonn instead of phantom) to the actual platform's web address. Users are then guided through a fake wallet creation process - which in reality, is just providing users with access to the attacker's wallet. After the "wallet setup" process has been completed, the phishing attack then redirects users towards the real website, where they're prompted to install the wallet extension. After introducing the pass phrase for the "generated" wallet address, users are actually connected to the bad actor's wallet. Any funds they transfer towards it can immediately be moved to another wallet that remains under the bad actor's control.
While the Phantom phishing scheme is focused on new wallet creations, the Metamask phishing attack is different, in that it can actually steal the users' private key. Not only is the fake wallet generation possible, but victims are also prompted to import their existing Metamask wallet - which will immediately give access to all of their existing funds.
More creative ways of stealing crypto funds have come and gone; however, and when it comes to this particular scam, an attentive user can look out for and easily skirt these attempts. Remember to always double-check the url you're clicking, and avoid landing in any crypto or banking-related page through an ad link. The browser URL is your best-friend here: it's good policy to keep an eye on it in any potentially sensitive scenarios. CPR published a YouTube video showcasing the phishing method; catch it below.
Get Tom's Hardware's best news and in-depth reviews, straight to your inbox.

Francisco Pires is a freelance news writer for Tom's Hardware with a soft side for quantum computing.
-
InvalidError Excpect these sorts of things to proliferate, largely thanks to most crypto transactions being irreversible once funds leave wallets managed by known entities.Reply -
cryoburner Of course, Google prominently featuring ads as if they were top search results doesn't help. If they are going to make ads look similar to results, you would think they would at least do some amount of manual verification that the company paying for the ad is legit before featuring an ad for them at the top of the page. I guess that's what gets the clicks to maximize ad revenue though.Reply -
Eximo Replycryoburner said:Of course, Google prominently featuring ads as if they were top search results doesn't help. If they are going to make ads look similar to results, you would think they would at least do some amount of manual verification that the company paying for the ad is legit before featuring an ad for them at the top of the page. I guess that's what gets the clicks to maximize ad revenue though.
That ship sailed a long time ago.
The ones that I can't tolerate are the free driver websites. Like, yes, they are free, what are you here for? Full of clickbait download links and malware. Google should nuke those from orbit, and yet, they have been there for over ten years. -
Krotow Good riddance for pyramid scheme zealots. If "money" loss will not teach them then no one should bother.Reply -
InvalidError Reply
If you happen to be parking your crypto in an exchange's wallet, yes.korekan said:Yes you might hit jackpot with crypto but can you actually cashout immideately?
If you stole crypto from people, that crypto would be in anonymous wallets that you need to launder somehow so the stolen crypto doesn't get immediately linked to you when you transfer it to a crypto exchange to cash out.

