U.S. Senator Calls On Federal Agencies To Improve IoT Device Security, Stop DDoS Attacks
Get Tom's Hardware's best news and in-depth reviews, straight to your inbox.
You are now subscribed
Your newsletter sign-up was successful
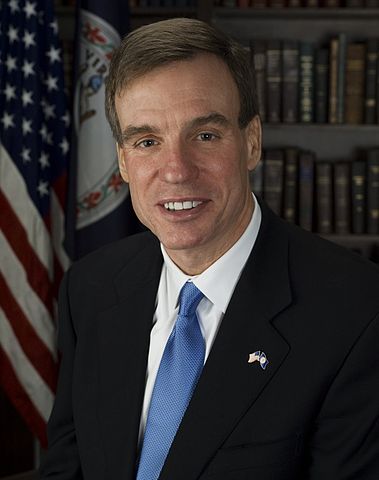
Virginia Senator Mark Warner (D), who is the co-founder of the Senate Cybersecurity Caucus and a member of the Senate Select Committee on Intelligence, sent a letter to three governmental agencies (FTC, FCC, and DHS) asking them what they can do about the recent IoT DDoS attacks and other related threats.
DoS Attacks Getting Stronger, Quickly
As seen with the recent massive DDoS attacks that have surpassed the terabit per second (Tbps) bandwidth limit, DDoS attacks are becoming an increasingly higher risk to internet services companies, and to the internet's infrastructure in general.
“The weak security of many of the new connected consumer devices provides an attractive target for attackers, leveraging the bandwidth and processing power of millions of devices, many of them with few privacy or security measures, to swamp internet sites and servers with an overwhelming volume of traffic,” said Sen. Warner in an article on his personal Senate page.“I am interested in a range of expert opinions and meaningful action on new and improved tools to better protect American consumers, manufacturers, retailers, Internet sites and service providers,” he added.
Article continues belowThings are likely going to get much worse before they get better, because we’re probably still a few years away from most IoT manufacturers taking the security of their devices much more seriously. They need to build the necessary infrastructure to support that new level of security.
In the meantime, many new insecure IoT devices are thrown on the market for consumers to buy, continuously expanding the potential for stronger DDoS attacks. Innovative new amplification techniques for DDoS could also make these attacks even stronger by at least an order of magnitude.
The botnet software that has been used in the past few massive DDoS attacks was open sourced under the name of "Mirai," which means it should now be even easier for malicious actors to use botnets or create their own forked versions.
The United States Computer Emergency Readiness Team (US-CERT) seems to have already identified a new family of malware, which is similar to Mirai, infecting vulnerable IoT devices. That means we may see further development of more effective and more resilient botnets in the future.
Get Tom's Hardware's best news and in-depth reviews, straight to your inbox.
IoT Security, A “Tragedy Of The Commons”
When the outlook for internet resilience is this dire, it seems government intervention to set some baseline standards for IoT security may be imminent. The European Union is already considering a labeling/rating system that would at least give consumers the opportunity to know which products are more secure.
However, this will likely be an insufficient solution, because when people buy their smart coffee maker or smart fridge, their first thought likely isn’t that it needs to be protected against being taken over by DDoS-creating botnets.
Individual consumers who buy IoT devices aren’t usually directly impacted by a DDoS attack, though. Their devices may upload a little more data when the botnet sends some packages to the DDoS target, but otherwise they may work just as well as they normally do.
Therefore, ensuring that most IoT devices that are being sold on the market are secure shouldn’t rely solely on the consumers. The consumers themselves won’t be able to put enough pressure on manufacturers to secure their devices simply because they wouldn’t be the ones most affected by the botnets taking over their devices.
Senator Mark Warner called this a “tragedy of the commons,” which is an economic theory about a situation where individuals would act in their own self-interest to the detriment of the common good.
“Manufacturers today are flooding the market with cheap, insecure devices, with few market incentives to design the products with security in mind, or to provide ongoing support,” said Senator Warner in his letter to the three federal agencies.“And buyers seem unable to make informed decisions between products based on their competing security features, in part because there are no clear metrics. Because the producers of these insecure IoT devices currently are insulated from any standards requirements, market feedback, or liability concerns, I am deeply concerned that we are witnessing a ‘tragedy of the commons’ threat to the continued functioning of the internet, as the security so vital to all internet users remains the responsibility of none. Further, buyers have little recourse when, despite their best efforts, security failures occur,” added Warner in his letter.
ISP-Level Blocking Of “Zombie” IoT Devices
Senator Warner noted also noted that under the FCC’s Open Internet rules, ISPs aren’t allowed to block “non-harmful” devices from their networks. However, they should be able to block harmful ones, such as the infected IoT devices participating in DDoS attacks, also called “zombie” devices.
Such an action might be a potential solution to the increasingly larger and rapidly evolving DDoS problem. It would not only disrupt DDoS attacks (assuming the ISPs are quick enough to react to them), but it might also hurt the image (and later the sales of) IoT manufacturers, whose devices would then be blocked from using the internet.
If consumers learn that the devices they bought from a manufacturer are no longer connected to the internet because they had security vulnerabilities that allowed them to be taken over by a DDoS-creating botnet, they might choose a different, more secure brand next time they buy a similar product. This is also where a good security rating system for IoT devices would be welcome.
That potential damage to their image and future sales could become the incentive IoT manufacturers need to invest heavily in security their devices. Government-mandated recalls could be another, stricter, alternative solution that should have a similar impact. However, IoT device makers will likely agree to do whatever is necessary to avoid that highly expensive scenario.
Preventing Censorship, Extortion, And Disruption Of Economic Activity
These solutions are not ideal, as abuses or other problems could arise from these actions, and they are also not the only possible solutions for dealing with DDoS attacks. However, they may be the most effective ones in stopping damaging DDoS attacks in the near future, and in accelerating the security of new IoT devices.
Massive DDoS attacks could be used as censorship tools against sites such as Reddit and Twitter, but they can also be used to target financial services sites such as PayPal--or government services, or any other website--for the purpose of extortion. This is why customers of IoT devices, who may mainly care whether the device works properly and has all the features they need, can’t be the only ones putting pressure on manufacturers to improve security.
Lucian Armasu is a Contributing Writer for Tom's Hardware US. He covers software news and the issues surrounding privacy and security.
-
skit75 Spouse A: Ohh look dear... this toilet paper dispenser only has a $300.00 annual firewall subscription!Reply
Spouse B: That must be on sale, GRAB IT! As long as we let the manufacturer know how much we wipe and agree to the 3rd party marketing flea-poop print, the first year is actually only $150.00! -
InvalidError A "limit" implies that it wasn't meant or believed to be possible to beat. 1Tbps DDoS isn't a limit, it is a milestone or a new high-watermark that will inevitably get surpassed at some point in the future as more bandwidth becomes available at the network edge and more potential victim devices come online.Reply -
falchard Honestly, when I saw it was a Democrat Senator proposing regulations on the Internet in the vain of added security, I expected something idiotic. He at least makes some sense that ISPs should not be forced to allow all traffic through their networks. Aside from that he didn't propose anything like requiring certain features, or having computer assemblers get a certification which is positive. He just asked for ideas from this business sector. So suffice to say I can't say how dumb it is until legislation is written.Reply
The only thing I can say is that he misunderstands the "Tragedy of the Commons" in terms of economics. It only applies to a limited resource that is open to public consumption. The tragedy of the commons is mostly eliminated when the resource is owned privately. It would be difficult to apply the theory on internet security and DDoS attack. -
Jeff Fx >Honestly, when I saw it was a Democrat Senator proposing regulations on the Internet in the vain of added security, I expected something idiotic.Reply
"Democratic." Wingnuts say "Democrat" rather than "Democratic." Do you want to be mistaken for a wingnut?
Why? Insanity usually comes from the delusional Republicans. Wingnuts, with inverted worldviews from Republican propaganda, imagine that the Democrats are the party that's out of touch. Again, you risk being mistaken for a wingnut.
Btw, it's spelled "vein." -
undersuit What if put government backdoors in all our devices? Then if our devices are misbehaving the government can turn them off.Reply
/s -
javaskull This to me sounds like a good idea potentially. It reminds me of computer interference regulations like what the FCC has on power supplies etc. Your device has to be secure. Otherwise it's illegal and we'll block it or fine you for using it (or better yet, selling or making it).Reply -
Blitz Hacker Mandate security standards on IoT Devices. Specifying a port range they can use (with default firmware) and develop security standards (updateable Over the Wire/Air) updates like cellphones. This will do two things. #1 it will make scanning for the devices easier (if the device doesn't pass security updates it will be apparent almost instantly as they will be exploited) secondly if such an attack occurs ISP's could simply drop the port range from traffic vs trying to filter packets which is not only resource intensive but not really practical.Reply
There will always be 'cheap crap' out there but simply blocking off the use based on traffic type outside of the given port ranges I think would be acceptable. Aswell I think device manufacturers need to be liable for maintaining the firmware (to a reasonable security level) over the life of the product.
This isn't an 'annoying side effect' this is potentially internet destroying behavior and should be dealt with as such. -
falchard Reply18787814 said:>Honestly, when I saw it was a Democrat Senator proposing regulations on the Internet in the vain of added security, I expected something idiotic.
"Democratic." Wingnuts say "Democrat" rather than "Democratic." Do you want to be mistaken for a wingnut?
Why? Insanity usually comes from the delusional Republicans. Wingnuts, with inverted worldviews from Republican propaganda, imagine that the Democrats are the party that's out of touch. Again, you risk being mistaken for a wingnut.
Btw, it's spelled "vein."
Republicans are a different type of stupid. Democrats, and I do use that as an insult tend to be for over regulation and unnecessary restrictions. They tend to make legislation on things they typically know little about, bring in experts they don't listen to, and implement overbearing rules that make the problem worse. Take for instance licensing which is a roadblock for people intending to get into an industry while not providing any added protection for the consumer.
Like I said, I can't say how this will be stupid until they make legislation on it. From the only proposal in the article, they are moving in a positive direction. Makes sense considering its the Virgina Senator proposing it instead of an institutionalized one like Chuck Schumer. -
targetdrone Just because a device has the latest top of the line totally impenetrable security TODAY doesn't mean design flaw or bug won't appear 12 months from now totally compromising the security. (Heartbleed, Stagefright, and all of those Java and Adobe flaws)Reply
It's hard enough getting security patches for Android smartphones that cost several hundreds of dollars. No IoT manufacture is going to write a new firmware for a year old, out of production $50 toaster(which was designed to break after 13 months of collecting dust on the counter anyways) -
targetdrone Reply18788737 said:This to me sounds like a good idea potentially. It reminds me of computer interference regulations like what the FCC has on power supplies etc. Your device has to be secure. Otherwise it's illegal and we'll block it or fine you for using it (or better yet, selling or making it).
So it should be illegal to use any version of Android that's not the latest version(which is Nougat as of today)? Yeah good luck with that one. millions of phones being used right now will never ever see Nougat. Now expand that craziness to toasters and coffee makers.