It's Now Legal to Crack Your PC Games
...but strictly for security purposes. New DMCA rules make it legal to rip your DVDs, jailbreak and unlock your phones too.
Get Tom's Hardware's best news and in-depth reviews, straight to your inbox.
You are now subscribed
Your newsletter sign-up was successful
The Digital Millennium Copyright Act (DMCA) got a big revision today that will likely change the way that users may lawfully use and enjoy the products and media that they own.
Today the Librarian of Congress announced DMCA Section 1201, which adds six provisions whereby "persons who circumvent access controls in order to engage in noninfringing uses of works in these six classes will not be subject to the statutory prohibition against circumvention."
Essentially, it comes down to this:
- People may now rip DVDs to show clips for educational purposes, criticism, commentary and noncommercial videos.
- People may now legally jailbreak their iPhones and root their Android phones without fear that a corporation will rain down upon them.
- People may now legally unlock their cell phones.
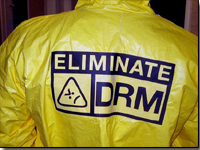
(These first three are mostly the result of lobbying from the Electronic Frontier Foundation.) - People may now circumvent the copy protection of PC and video games for investigative reasons. This should be a great thing for PC gamers sick of dealing with the DRM of the games they legally purchased.
- People may now get past software that's protected by an outdated hardware dongle.
- People may now break past ebooks that don't allow the text to be read aloud.
The official listing of the six classes of works are:
(1) Motion pictures on DVDs that are lawfully made and acquired and that are protected by the Content Scrambling System when circumvention is accomplished solely in order to accomplish the incorporation of short portions of motion pictures into new works for the purpose of criticism or comment, and where the person engaging in circumvention believes and has reasonable grounds for believing that circumvention is necessary to fulfill the purpose of the use in the following instances: (i) Educational uses by college and university professors and by college and university film and media studies students; (ii) Documentary filmmaking; (iii) Noncommercial videos(2) Computer programs that enable wireless telephone handsets to execute software applications, where circumvention is accomplished for the sole purpose of enabling interoperability of such applications, when they have been lawfully obtained, with computer programs on the telephone handset.(3) Computer programs, in the form of firmware or software, that enable used wireless telephone handsets to connect to a wireless telecommunications network, when circumvention is initiated by the owner of the copy of the computer program solely in order to connect to a wireless telecommunications network and access to the network is authorized by the operator of the network.(4) Video games accessible on personal computers and protected by technological protection measures that control access to lawfully obtained works, when circumvention is accomplished solely for the purpose of good faith testing for, investigating, or correcting security flaws or vulnerabilities, if: (i) The information derived from the security testing is used primarily to promote the security of the owner or operator of a computer, computer system, or computer network; and (ii) The information derived from the security testing is used or maintained in a manner that does not facilitate copyright infringement or a violation of applicable law.(5) Computer programs protected by dongles that prevent access due to malfunction or damage and which are obsolete. A dongle shall be considered obsolete if it is no longer manufactured or if a replacement or repair is no longer reasonably available in the commercial marketplace; and(6) Literary works distributed in ebook format when all existing ebook editions of the work (including digital text editions made available by authorized entities) contain access controls that prevent the enabling either of the book’s read-aloud function or of screen readers that render the text into a specialized format.
Get Tom's Hardware's best news and in-depth reviews, straight to your inbox.