Google To Remove China's Root Certificate Authority From Chrome Over Ties To Forged Certificate
Get Tom's Hardware's best news and in-depth reviews, straight to your inbox.
You are now subscribed
Your newsletter sign-up was successful
Last week, Google's security engineers wrote a post about an intermediate certificate authority (CA) called MCS Holdings that issued some unauthorized digital certificates for Google's domains. The intermediate certificate for MCS Holdings was issued by CNNIC, China's main root certificate authority. Google believes CNNIC is also responsible for that forged certificate and has decided to remove it from Chrome.
The Problem With Rogue CAs
When a certificate authority issues false certificates that allow for unsecure connections and traffic interception, browser vendors usually respond by banning that CA and revoking its issued certificates.
This sort of policy is important because the security model of the Web is rather vulnerable, having to depend on thousands of random certificate authorities and a few root CAs. These root CAs may even have strong ties to their local governments, and depending on the government, their intentions may not always be to the benefit of everyone on the Web.
If browser vendors would allow the rogue CAs to break Internet security, even after they catch them doing it, then it could create a domino effect, and the security of the Web could fall apart. More CAs could start taking risks and forging certificates for various benefits, knowing that the browser vendors won't punish them.
Also, if more people would see that their browsers continue to trust less trustworthy certificate authorities, they would eventually stop trusting HTTPS connections, too (which are useful for secure online banking, e-commerce, and stopping traffic interception, among many other things).
Therefore, banning bad CAs seems like the most reasonable thing to do within the current security model of the Web as a deterrent for other CAs to avoid the same mistake.
Banning The CNNIC Root CA
Although this is usually expected to happen, few thought Google or any other browser vendor would go as far as to ban not just MCS Holdings, but also China's root certificate authority, CNNIC. Yet, this is exactly what Google has just announced.
Get Tom's Hardware's best news and in-depth reviews, straight to your inbox.
In a future update, the CNNIC root certificate will be revoked. For the time being, Google will continue to allow CNNIC's certificates to be used in Chrome through a publicly disclosed whitelist. After that, before it asks for reinclusion in the Chrome root store, CNNIC must adopt the Certificate Transparency system that Google has been proposing for the past few years.
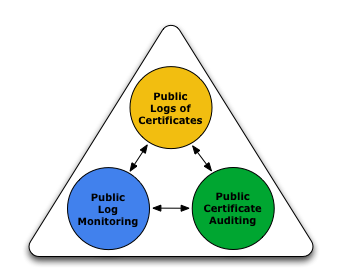
Certificate Transparency
Although right now Google can quickly identify when forged certificates are issued for its domains, thanks to certificate pinning in Chrome, this solution isn't scalable and usually works only for Google's own websites. For that reason, Google came up with the Certificate Transparency project, which provides an "open framework for monitoring and auditing SSL certificates in nearly real time."
The main goals of Certificate Transparency are:
Make it impossible (or at least very difficult) for a CA to issue an SSL certificate for a domain without the certificate being visible to the owner of that domain.Provide an open auditing and monitoring system that lets any domain owner or CA determine whether certificates have been mistakenly or maliciously issued.Protect users (as much as possible) from being duped by certificates that were mistakenly or maliciously issued.
Because it's an open framework, anyone can verify the basic components that make Certificate Transparency work. This open system should bring a certain degree of improvement to the current CA model where it's hard to even know when a certificate against a certain site has been forged.
China's CNNIC responds
Although Google seems to imply that CNNIC has already agreed to implement Certificate Transparency for its certificates before it's reincluded in Chrome, the root CA responded publicly today by using a completely different tone:
“1. The decision that Google has made is unacceptable and unintelligible to CNNIC, and meanwhile CNNIC sincerely urge that Google would take users' rights and interests into full consideration.2. For the users that CNNIC has already issued the certificates to, we guarantee that your lawful rights and interests will not be affected."
Other Browser Vendors Have Yet To React
Although Chrome is arguably the most popular web browser today (especially when including its mobile market share), it still has only about a third of the browser market. For this move to be completely effective, Mozilla, Apple and Microsoft might have to do what Google did and remove CNNIC from their certificate root store.
Right now, Mozilla seems to be at least considering limiting CNNIC new certificates in its browser. However, it doesn't currently plan to remove CNNIC from the root store, unless the Chinese root CA doesn't agree to its set of requests in order to have some form of verification for its certificates.
Do not remove the CNNIC root, but Reject certificates chaining to CNNIC with a notBefore date after a threshold date Request that CNNIC provide a list of currently valid certificates, and publish that list so that the community can recognize any back-dated certs Allow CNNIC to re-apply for full inclusion, with some additional requirements (to be discussed on this list) If CNNIC's re-application is unsuccessful, then their root certificates will be removed
Apple has been in a security promotion campaign lately and has even had some security troubles in China. Therefore, it wouldn't be too far-fetched for the company to follow in Google's footsteps. At the same time, Apple is seeing rapid growth for its iPhones in China, so it remains to be seen whether it will back Google on this, or whether it will compromise in order to maintain a good relationship with the Chinese government there and not harm its sales in any way.
China hasn't always treated Microsoft well either, especially more recently when the government announced the banning of Windows 8 from government institutions. However, Microsoft has a relatively long history of giving in to China's censorship or surveillance requests, so it's once again hard to predict whether the company would follow Google's bold move to ban CNNIC from Internet Explorer (and Project Spartan).
As usual, when security is involved, the weakest leak can make the whole system fall apart. In the same way, having some of the major browser vendors fail to agree to punish the rogue certificate authorities for issuing fake certificates could set a dangerous precedent.
Follow us @tomshardware, on Facebook and on Google+.
Lucian Armasu is a Contributing Writer for Tom's Hardware US. He covers software news and the issues surrounding privacy and security.
-
vaughn2k "For the users that CNNIC has already issued the certificates to, we guarantee that your lawful rights and interests will not be affected.." Yeah right...Reply -
Achoo22 That's great, so long as there is always a way for users to accept certificates Google deems insecure. What we can't have is a situation where overlord Google is the sole guarantor of web security, gatekeeper to all encrypted sites.Reply -
hellogts ReplyThey'll strike a deal before long.
That's great, so long as there is always a way for users to accept certificates Google deems insecure. What we can't have is a situation where overlord Google is the sole guarantor of web security, gatekeeper to all encrypted sites.
If you don't trust Google, don't use Chrome, simple.
'Don't be Evil' - Google
-
Achoo22 ReplyIf you don't trust Google, don't use Chrome, simple.
Better to be able to use Chrome without trusting Google. -
ananke CNNIC was hacked and certificates stolen, hence Google is immediately shutting them off, to ensure the existence of "cloud" and "Internet" the way we know it :) Probably, this was related to the bank sham that IBM announced discovered yesterday...Of course, nobody wants to explain clearly.Reply -
f-14 2. For the users that CNNIC has already issued the certificates to, we guarantee that your lawful rights and interests will not be affected."Reply
RIGHTS? YOU HAVE NO STINKING RIGHTS IN CHINA, YOU TAKE WHAT YOU ARE GIVEN BY CHINAGOV AND LIKE IT OR ELSE! *POOF* -
shiitaki I have more respect for Google since they are willing to take a stand.Reply
Microsoft will ask how high when China asks them to jump. They never have and never will promote or protect the end user. Everything about MS is how to shovel more money to stock holders.
I think there are simply too many Certificates anyway. It is a lot of work but maybe it is worth investigating the removal of 95 percent of them. I don't need any certs from mother Russia, Nigeria, or for that matter anywhere else I never go. And just to be fair, I don't need the five from the DOJ either.