Researchers Develop RISC-V Chip for Quantum-Resistant Encryption
The goal is to pre-empt the fall of traditional cryptography likely to follow the quantum revolution.
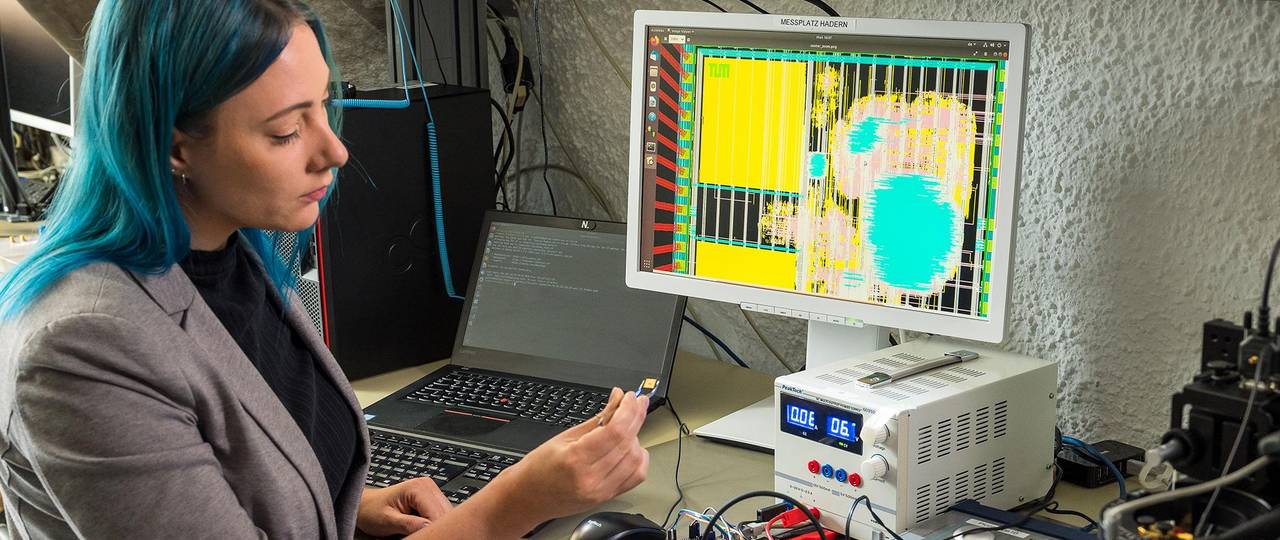
A research team with the Technical University of Munich (TUM) have designed a quantum cryptography chip aimed at the security demands of the quantum computing revolution. The RISC-V chip, which was already sent to manufacturing according to the researchers' design, aims to be a working proof of concept for protecting systems against quantum computing-based attacks, which are generally considered to be one of the most important security frontiers of the future. Alongside the RISC-V based hardware implementation (which includes ASIC and FPGA structures), the researchers also developed 29 additional instructions for the architecture that enable the required workloads to be correctly processed on-chip.
Traditional cryptography is generally based on both the sender and receiver holding the same "unlock" key for any given encrypted data. These keys (which may include letters, digits, and special characters) have increased in length as time passes, accompanying increases in hardware performance available in the general computing sphere. The idea is to thwart brute-force attacks that would simply try out enough character combinations that would allow them to eventually reach the correct answer that unlocks the encrypted messages' contents. Given a big enough size of the security key (and also depending on the encryption protocol used), it's virtually impossible for current hardware — even with the extreme parallelization enabled by the most recent GPUs — to try out enough combinations in a short enough timeframe to make the effort worthwhile.
A piece of information cryptographically encoded by one of the most popular encryption algorithms used today, AES-128, would be impossible to crack by even the most powerful distributed computing efforts of today, Bitcoin. For reference, it would take the network around 70,000,000,000,000,000,000,000,000 years to do so (kudos if you can count that high a number) and it's estimated our universe has existed for only 14 billion years, comparatively speaking. Encryption-breaking algorithms on the quantum computing sphere would require quantum systems with an estimated 2,953 logical qubits for near-instant decryption of an AES-128 key, and 6,681 logical qubits for AES-256.
Current quantum technology has achieved a "mere" 100 qubits total, so we're still somewhat far-off from a security collapse. But quantum computing is advancing at a breakneck speed since the first actual first quantum computer manifestation — a dual-qubit system showcased in 1998 by Isaac Chuang of the Los Alamos National Laboratory, Neil Gershenfeld of the Massachusetts Institute of Technology (MIT), and Mark Kubinec of the University of California at Berkeley that could be loaded with data and output a solution. The acceleration in qubit counts for new quantum systems and the potential appearance of new decryption algorithms could upend current encryption techniques much faster than expected, and that's the reason why the TUM research team is focussing on pre-empting security challenges that are expected to eventually materialize.
In designing their quantum-security chip, the TUM researchers took a cohesive (and world first) hardware and software co-design approach, with purpose-designed hardware that accelerates the current poster-child for quantum cryptography, the lattice-based Kyber algorithm. The researchers say they've achieved a 10x performance increase compared to current software Kyber encryption solutions, while using around eight times less energy. The chip also features support and a 21x performance increase for an even more advanced form of quantum encryption, Supersingular Isogeny Key Encapsulation (SIKE), which is expected to be deployed when lattice-based approaches, such as Kyber, no longer cut it.
In addition to the Kyber and SIKE acceleration, the research team is also using this chip as an accelerator for smart hardware Trojan detection. Hardware Trojan is a term that refers to the addition of hardware-based solutions that aim to circumvent typical security mechanisms by offering backdoors that either siphon information to a remote attacker, or enable silent, undetected access to the compromised system's processing. These hardware Trojans can be secretly implemented in various stages of hardware fabrication (such as in the design or manufacturing stages), and concerns regarding this potential attack vector hit the public space with the (fake) reports of certain Supermicro-manufactured motherboards allegedly featuring purpose-built chips that siphoned data to China.
To fill the void of information on this novel security exploit, the TUM researchers have also fitted their chip with four distinct hardware Trojans. These will literally destroy their proof-of-concept chip layer by layer while feeding each step of the process to newly-developed machine learning algorithms, training them in identifying hardware functions even in the absence of technical information regarding what the hardware does exactly. This helps to identify components (Trojans) that perform functions unrelated to the chip’s actual tasks that may have made their way into the final design. This research will also likely provide lasting effects in the reverse-engineering space, and it's likely that it's being pursued by other parties (academic or otherwise).
Get Tom's Hardware's best news and in-depth reviews, straight to your inbox.
Quantum computing stands at the forefront of a brave new world in the technology sphere. As I wrote this article, I was reminded of Arthur C. Clarke's Third Law: “Any sufficiently advanced technology is indistinguishable from magic”. I for one am having difficulty in distinguishing one from the other.

Francisco Pires is a freelance news writer for Tom's Hardware with a soft side for quantum computing.
