Nvidia Licenses Rambus DPA Countermeasures To Secure Critical GPUs
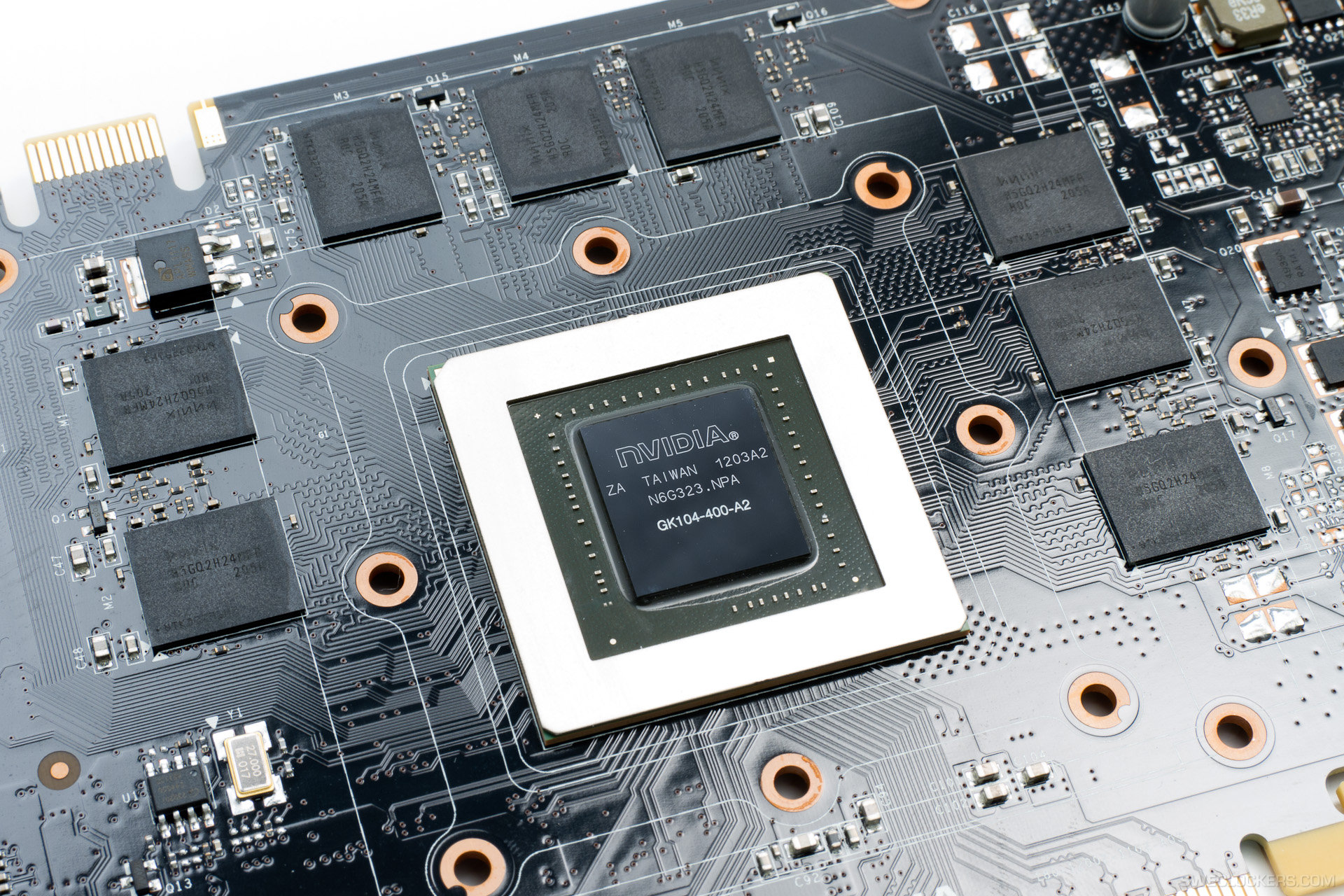
Rambus announced that Nvidia licensed its differential power analysis (DPA) countermeasures for use in GPUs powering AI, self-driving cars, and more.
Rambus designed the countermeasures to protect Nvidia's GPUs from side-channel attacks that steal encryption keys by measuring a device's power consumption. Attacks like this can be used to break into protected systems, assist law enforcement with digital forensics, and undermine the common encryption protocols used to secure private data. As computer control more objects--be it through AI, self-driving vehicle technologies, or the rise of the Internet of Things (IoT)--these side-channel attacks could simultaneously grow in popularity and in their ability to wreak havoc on people's lives.
Rambus made a DPA Workstation (DPAWS) to help its customers defend themselves from these attacks. The company said in its announcement that DPAWS "analyzes hardware and software cryptographic implementations for vulnerabilities to power and electromagnetic side-channel attacks" and uses "an integrated suite of hardware and data visualization software to aid in the identification and understanding of vulnerabilities in cryptographic chips." The idea is that all of these tools will be able to work together to ensure that a device's power consumption doesn't leak any sensitive information.
Article continues below"Rambus’ Security Division has pioneered countermeasures designed to thwart Differential Power Analysis (DPA) attacks – an increasingly common attack that uses variations in electromagnetic emissions to derive cryptographic keys and other sensitive information from chips found in modern hardware. These threats are not found just in the artificial intelligence, autonomous cars, virtual reality and professional visualization industries, but also expose vulnerabilities in the aerospace and defense industry, financial sector, retail sector and more," read a press release in part.
Nvidia's GPUs have become increasingly popular among technologists working on AI and other advanced technologies. For such applications, GPUs are generally faster and more efficient than CPUs, which makes them ideal candidates for use in systems that require lots of processing power, like training a deep learning network. Nvidia encourages the use of its GPUs in these technologies by hosting online courses, presenting at conferences devoted to AI, and developing new platforms designed specifically for self-driving vehicles. GPUs--and therefore Nvidia--are critical to the development of increasingly smart devices.
The growing ecosystem also makes GPUs a target for hackers. As critical systems come to rely on Nvidia's products, the company will have to make sure it’s prepared for all kinds of attacks. It's not enough to encrypt information, prevent it from being posted to the internet, or even making sure a device is completely self-contained. If someone can conduct a side-channel attack, there's a good chance they'll be able to gain access to devices to use them for nefarious purposes, whether it's driving an autonomous vehicle off the road or allowing them to conduct DDoS attacks with a continually growing botnet.
Botnets have already become a problem as IoT enters more homes. A DDoS attack thought to be conducted via a botnet of infected "smart" cameras took down some of the world's most popular websites last week--twice. Most of these devices use CPUs for now, but as they become more resource-hungry, they too could switch to GPUs for many tasks. Companies making GPUs are going to have to batten down the hatches to make sure their products don't accidentally help state-sponsored actors and criminals alike with surveillance, theft, or other misdeeds.
Get Tom's Hardware's best news and in-depth reviews, straight to your inbox.
The good news is that the side-channel attacks like those Rambus is defending against require physical access to a device. This means that hackers are unlikely to rely on these attacks on a large scale, but that doesn't mean these companies should be complacent. Increasingly connected lives create a growing number of attack vectors, which means Rambus and Nvidia working together to block these attacks is likely to pay off sometime in the near future.
Rambus and Nvidia did not say when Nvidia would incorporate DPAWS and other DPA countermeasures into Nvidia's products.

Nathaniel Mott is a freelance news and features writer for Tom's Hardware US, covering breaking news, security, and the silliest aspects of the tech industry.
-
falchard Good bye nVidia. Nothing good has happened from licensing Rambus Technology.Reply
Intel licensed them for Pentium 4. They let in an unprecedented era of AMD64. Sony licensed Rambus Technology for the PS3, failed compared to the XBox 360. -
Lkaos "Sony licensed Rambus Technology for the PS3, failed compared to the XBox 360"...FAILED!?Reply
Are you living in the same universe as us? The PS3 was a huge success in all aspects... -
10tacle Reply18775521 said:Sony licensed Rambus Technology for the PS3, failed compared to the XBox 360.
Yes because the PS3 outselling the XB360 by 90 million to 85 million worldwide is a failure (never mind the 360 had a year head start in sales). And let's not even get into the joke of the XBone that can't run games at native 1080p like the PS4. :sarcastic: http://www.extremetech.com/gaming/225131-quantum-break-is-gorgeous-stuck-at-720p-on-the-xbox-one