7-Zip App Vulnerability Grants Admin Privilege to Attackers (Update)
But while we wait for an update it is quite easy to mitigate.

Update 4/20/2022 7:50amPT: The listed 7zip CVE-2022-29072 vulnerability has now been marked as "disputed" in the official listing, and "multiple third parties have reported that no privilege escalation can occur." According to Google Project Zero vulnerability researcher Tavis Ormandy who alerted us to the dispute, this exploit could only occur by editing the registry and possibly other maneuvers (like adding another Local Administrator account). However, the description isn't clear enough to discern the method of attack. We'll keep you updated if the dispute is granted.
Original Article:
A vulnerability has been discovered in 7-zip, the popular archiving program. This is an active zero-day vulnerability and is characterized as allowing privilege escalation and command execution. In other words, someone with limited access to your computer would be able to gain higher-level control, usually admin access, to run commands or apps. GitHub user Kagancapar seems to have unearthed this 7-zip Windows vulnerability, and it has reference CVE-2022-29072.
7-zip is a cross-platform app, but this vulnerability is tied to Windows, as it relies on 7-zip's interactivity with the Windows help application, hh.exe. For example, the GitHub readme file for CVE-2022029072 surmises "Windows allows privilege escalation and command execution when a file with the .7z extension is dragged to the Help>Contents area."
The clip above shows the vulnerability discoverer dropping a specially crafted file with a .7z extension (mimicking the 7-zip file extension) onto the 7-zip help window and running a command in admin mode. This looks like quite a simple way to gain higher-level access to a system and run commands and apps that might otherwise be off-limits.
Kagancapar provided some enlightening background information on the vulnerability and its discovery. First, they mention that 7-zip isn't entirely happy to shoulder the blame for this vulnerability, as it seems dependent on the Microsoft Help system. However, the dropping of the custom .7z extension file on the Help window causes a heap overflow in 7zFM.exe and resulting privilege elevation – so that means 7-zip authors should accept part of the blame.
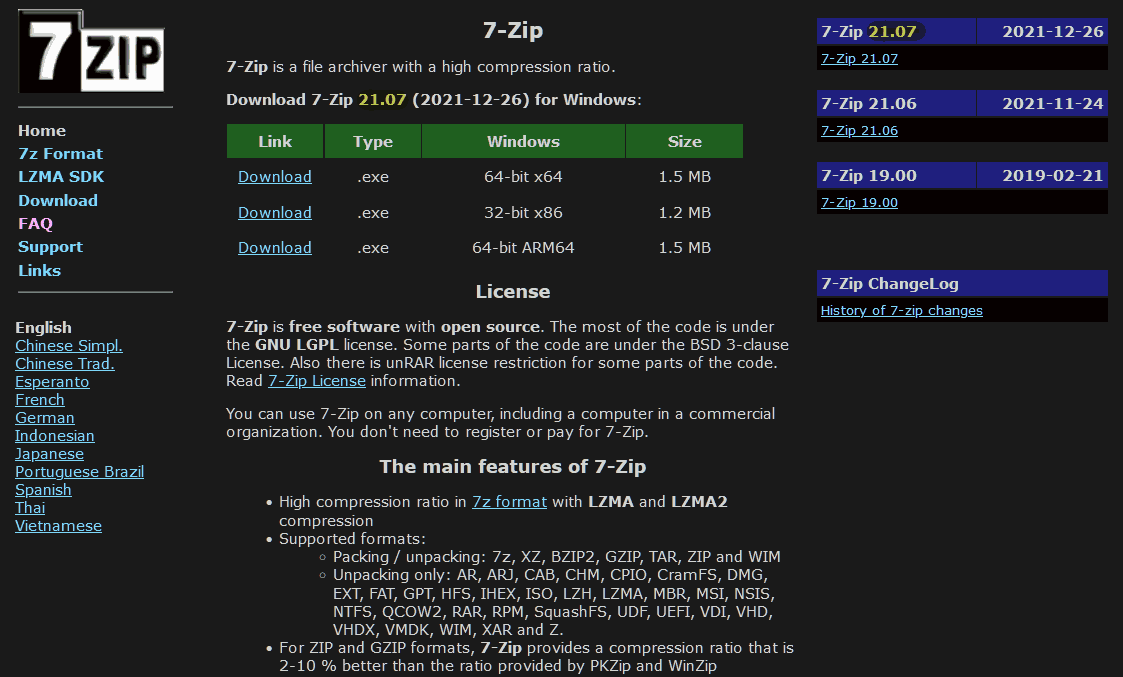
At the time of writing the current version of 7-zip for Windows, v21.07, is not patched for the vulnerability demonstrated in the video. If the vulnerability is of concern to you, with regard to your personal computer or systems you administer, please take some comfort from two easy ways to mitigate the issue:
- First method: If 7-zip does not update, deleting the 7-zip.chm file will be sufficient to close the vulnerability.
- Second method: The 7-zip program should only have read and run permissions. (For all users)
7-zip broke the hegemony of the skinflint guilt-inducing shareware compression staples WinZip and WinRAR in the noughties. After a few years of refinement, it was given a Tom's Hardware Elite Award for compression speed, ratio, and size back in 2013. As well as being totally free for personal or business use, 7-zip charms with its cross platform nature and portability.
Get Tom's Hardware's best news and in-depth reviews, straight to your inbox.

Mark Tyson is a news editor at Tom's Hardware. He enjoys covering the full breadth of PC tech; from business and semiconductor design to products approaching the edge of reason.
-
Reply
One who's working on a shared/work/school computer?digitalgriffin said:What end user would drop a .7z file on a windows help program? -
Electrichead Its not just any .7z file. Looks like an executable that is specifically designed to elevate privileges wrapped up in a 7z file.Reply -
stealth006 The mitigation steps don't quite make sense to me, because if someone really wanted to exploit this, they would just have to download the affected 7zip executable, the affected chm file, and the specifically crafted 7z file to any system, and voila. So that means there really is no mitigation to this other than, maybe, application blacklisting?Reply
Am I missing something?
Expanding on the above, that means it would be far easier for someone to create a malicious dll file that explots the inherent vulnerability in Microsoft's CHM system, and then you have an exploit that doesn't depend on 7zip at all. This means that the vulnerability isn't really with 7zip at all, but with Microsoft, and there is no type of mitigation until Microsoft patches it. -
mo_osk Replystealth006 said:Am I missing something?
Maybe the attack only works if 7fm.exe is in the program files folder? -
passivecool I've has several attack attempts recently, with 7z attachments in emails. Sometimes outlandish, sometimes almost admirably refined; I run a couple of businesses so some very strange correspondence can turn out to be legitimate. I figured it was ransomware but could have been this as well.Reply -
wujj123456 Reply
Depends on the threat model, whether you consider your end user trusted or not. This is largely true for all local privilege escalation vulnerabilities.stealth006 said:The mitigation steps don't quite make sense to me, because if someone really wanted to exploit this, they would just have to download the affected 7zip executable, the affected chm file, and the specifically crafted 7z file to any system, and voila. So that means there really is no mitigation to this other than, maybe, application blacklisting?
Am I missing something?
Expanding on the above, that means it would be far easier for someone to create a malicious dll file that explots the inherent vulnerability in Microsoft's CHM system, and then you have an exploit that doesn't depend on 7zip at all. This means that the vulnerability isn't really with 7zip at all, but with Microsoft, and there is no type of mitigation until Microsoft patches it.
If you assume the local user is malicious, then you are totally right. People can actively write exploits, let alone copying some vulnerable binary to trigger some known exploit. The fix has to be the root cause that would prevent escalation even with a vulnerable application, or generic mitigation like application blacklisting, signature detection or application sandboxing. If 7-zip doesn't have admin privilege to begin with, whatever bug it has shouldn't have allowed it to obtain the privilege. After all, it could have been an actual exploit, not a buggy application.
On the other hand, most of time the actual user may be the victim, and it's the hacker trying to trick them into triggering the vulnerability attempting to gain admin privilege. In those cases, patching the trigger is helpful and widely used applications are common attack surface. This angle just happens to be rather weak here, because who would normally drag a file to help window? Perhaps only when tricked by social engineering to do so. It's probably easier to trick someone into allowing your excel macro than dragging a suspicious file to help window. ¯\(ツ)/¯ -
rugupiruvu https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-29072ReplyNOTE: multiple third parties have reported that no privilege escalation can occur.
¯\(ツ)/¯ Fishy.