AMD, Google Partner in Unprecedented, EPYC Cybersecurity Effort
Looking for flaws that could topple the globe.
AMD and Google have announced an intricate, deep-level collaboration on cybersecurity research for AMD's server-class EPYC CPUs — one that's now been running for five years. According to Wired, the partnership leveraged two Google Cloud Security research teams alongside Google's Project Zero (a cybersecurity research arm within the company), and AMD's firmware group.
The aim was to put AMD's hardware and secure processors through their paces via seemingly unprecedented access to AMD's source code and security mechanisms. In the post-mortem report on the (ongoing) collaboration, the partnership announced the discovery and mitigation deployment for 19 security vulnerabilities in total. That's 19 less vectors of attack on one of the world's most successful server architectures.
The researchers mainly focused their efforts on AMD's Secure Processor (ASP) as implemented in AMD's third-gen EPYC, Milan. Google engineers were given access to source code for the ASP, alongside production samples to test hardware attacks. Of particular interest for Google was AMD's next-gen implementation of Secure Nested Paging (SEV-SNP), a capability that enables Virtual Machines (VMs) to remain confidential against the hypervisor itself. The engineering teams reviewed the design and source code implementation of SEV, wrote custom test code, and ran hardware security tests, attempting to identify any potential vulnerabilities that surfaced.
Article continues below 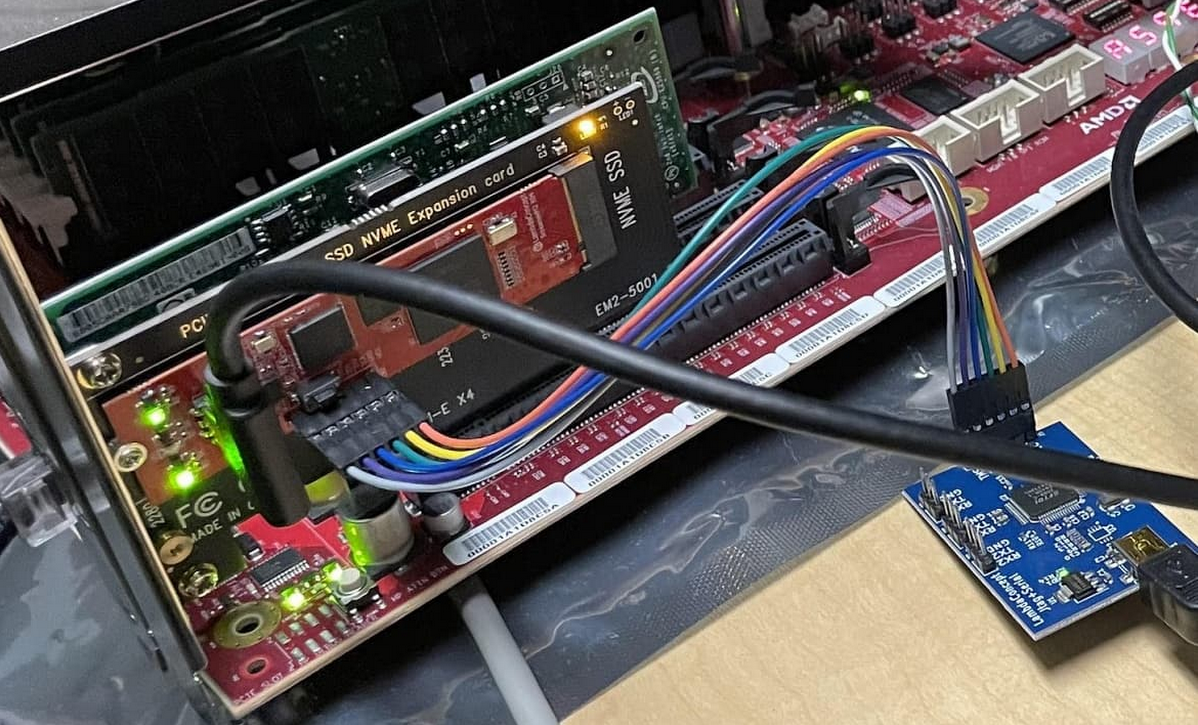
Brent Hollingsworth, AMD's director of the EPYC software ecosystem, pointed out that the partnership pooled AMD and Google's best and brightest, opening up the space to previously unknown attack vectors, and pushing creativity on attack layers - whether software- or hardware-based.
As the "chip-within-the-chip" that's responsible for cryptographic encryption of data, AMD's ASP is a generic processor "core" whose features can be built upon by AMD and its hardware and firmware design teams. But with each additional layer of security comes the chance of added attack vectors against this centralized security mechanism - a potentially severe point of failure that can throw the entire system's security out the proverbial window (with the invisibility of root access) should it be compromised.
It's at this impact level that the AMD-Google partnership was formed; according to Nelly Porter, group product manager with Google Cloud, the aim isn't to point fingers or call AMD's vulnerabilities — it's a combined, collaborative effort for the companies to shore up their defenses against increasingly creative and technically-skilled attackers. Cybersecurity has always been thought of as being on the backstep against those that would crack it; both AMD and Google want to be at the forefront of efforts to reverse the game.
The partnership was mostly motivated by Google's offering of its Confidential Computing services, which aim to keep customer's data encrypted at all times - whether at rest, in transit, or during processing. Following the increasing dependency on cloud computing services (ranging from classic workload offloads to the cloud, cloud gaming, or even cloud-based operating systems such as Microsoft's Windows 365 Cloud), the risk posed by potential vulnerabilities in the security infrastructure could originate billions of dollars of losses. Considering AMD's part on the research effort, the company is well aware of the benefits to be gleaned from both company's expertise in improving its products.
Get Tom's Hardware's best news and in-depth reviews, straight to your inbox.
The audit may well showcase a needed shift from the "vaulted secrets" approach companies are known to take regarding their products and intellectual property security. As cybersecurity-related incidents have been exploding in recent years, in both numbers, impact and complexity, the impact of successful attacks tends to only increase. The news also comes at a time when ransomware groups are showing increasing activity — cybersecurity company Secureworks has recently called the world's attention to the apparent resurgence of hacking group REvil.
Cybersecurity is one of the world's most important endeavors, following the almost complete digitization of services, money (whether in traditional FIAT-based bank accounts or the currently bleeding, crimson roads of crypto and DeFi), and global infrastructure. Flipping a binary one toward a zero can potentially upend globalization and economics around the world. And that's something no company or individual wants to live through.

Francisco Pires is a freelance news writer for Tom's Hardware with a soft side for quantum computing.