End-To-End Encryption Could’ve Protected Yahoo Mail Users From 2014 Data Breach And NSA Spying
Get Tom's Hardware's best news and in-depth reviews, straight to your inbox.
You are now subscribed
Your newsletter sign-up was successful
Over the past few weeks, it’s been uncovered that half a billion Yahoo Mail accounts were exposed in a record-breaking data breach and that Yahoo may have scanned its users' emails on behalf of the U.S. government, too. In both situations, end-to-end encryption would’ve protected users’ information.
Protection Against Data Breaches
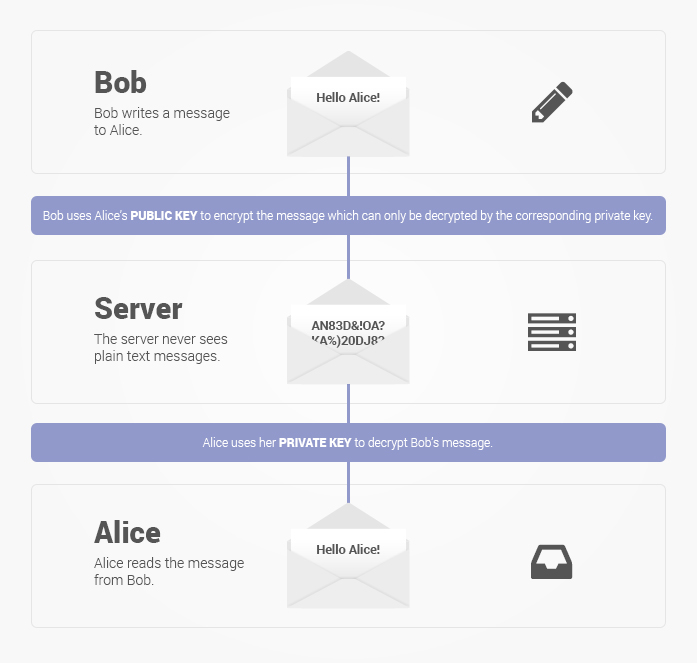
End-to-end encryption (E2EE) encrypts the data locally on the device before it's sent over the network, so it usually doesn’t matter whether the communications channel has strong encryption, weak encryption, or no encryption at all. Without cryptographic signature verification, an attacker could still pretend he’s the person that you’re trying to reach, but even then, there could be other ways to protect against it.
An email service such as Yahoo Mail can’t expose user communications in a data breach if the data has end-to-end encryption, because even the company itself can’t access the data. The pro, as well as the con, to E2EE (done over OpenPGP in the case of email) is that the user is responsible for email encryption.
Article continues belowOn one hand, that means nobody else should be able to access the data, but on the other hand, the user also needs to keep the private encryption key safe (ideally on a physical USB security key that has support for OpenPGP). If someone steals the key, they can decrypt the communications.
Protection Against Spying
Not surprisingly, many of the same reasons why E2EE protects against data breaches also apply when trying to protect against spying, with or without the service provider’s involvement. A spying tool can’t decrypt the E2EE email going through Yahoo’s servers for the same reason the company can’t decrypt email for data mining purposes.
The reason many governments oppose end-to-end encryption is because they can’t treat companies with millions or hundreds of millions of users as a one-stop spy shop anymore. If the governments want the data, they would have to go to the owners of the data, not the third-party companies that handle the communications.
When the data does not have end-to-end encryption, governments can issue warrants to legally request the individuals' data from third-party service providers. They can also use the same tactic that the U.S. government allegedly used with Yahoo: Install malware that provides almost total access to any data contained on the infected servers while also ordering the company to hand over information using more legitimate systems.
Get Tom's Hardware's best news and in-depth reviews, straight to your inbox.
The latter may, at the very least, be in a legal gray area, but it may violate constitutional and international privacy rights due to the “indiscriminate” and “non-proportional” aspect of this type of surveillance.
End-To-End Encrypted Email
Google announced its “End-To-End” browser extension, which aimed to make OpenPGP encryption more mainstream by making it easier to find your friends’ public keys so you can send emails over OpenPGP. Alex Stamos, who ran Yahoo security (and now works at Facebook), quickly jumped on board and said the company would also support the extension.
A year later, Yahoo even demoed a preview version of the extension ahead of Google. However, we haven't heard much on the topic from the company since then. However, we do know from a recent report that Yahoo’s CEO, Marissa Mayer, allegedly clashed with the security team often and didn’t give it the necessary budget to secure the company’s infrastructure.
Google doesn’t appear to have contributed to its End-To-End public project over the past six months, and it hasn't made any other public announcements since 2014. During our talks with the company, Google said that it’s still interested in developing end-to-end encryption for Gmail, but refused to go into further details about the implications.
For users who want end-to-end encrypted email, it may be time to stop waiting around for Google or Yahoo to deliver it and start using services or tools that offer it by default. If you’re a Yahoo user, and you feel like Yahoo betrayed your trust both by how it handled the data breach and by the reports that it has been allowing the U.S. government to search through everyone’s emails, now may be a great time to switch from Yahoo to a service that supports end-to-end encryption.
ProtonMail
ProtonMail, developed by a group of former CERN scientists and engineers based in Switzerland, is perhaps is the best-known end-to-end encrypted email service to appear in the post-Snowden era.
The company says it uses OpenPGP to encrypt users’ emails end-to-end. ProtonMail aims to make it easier to use OpenPGP, which means the company manages the users’ public and (encrypted) private keys.
The service encrypts the emails in the browser, but you still have to trust that the email you send is paired with the contact you send it to. You also have to trust that ProtonMail’s servers won’t be hacked, or that the Swiss government won’t try to impose a backdoor inside the company.
However, Swiss privacy laws are among the strongest in Europe, and the company has said that even the recent surveillance law passed by the government won’t affect the privacy of its users, as it doesn’t target encrypted communications that the providers can’t decrypt. Because you still encrypt the email in the browser with OpenPGP, that means ProtonMail can’t read them.
As an additional protection, the email inbox (mailbox) is also AES-encrypted with a user-assigned password. Therefore, even if an attacker hacks ProtonMail’s servers and somehow gets your private key, they would still need your second password to decrypt your mailbox data.
Because OpenPGP is required for end-to-end encrypted email, and because ProtonMail has a custom system for handling OpenPGP emails, that means you can use E2EE emails only with other ProtonMail users. When you send emails to users of other email services, you can also encrypt the emails with a password (different from the mailbox one) and then share that password through another secure channel with your contact so they can decrypt the email on their end.
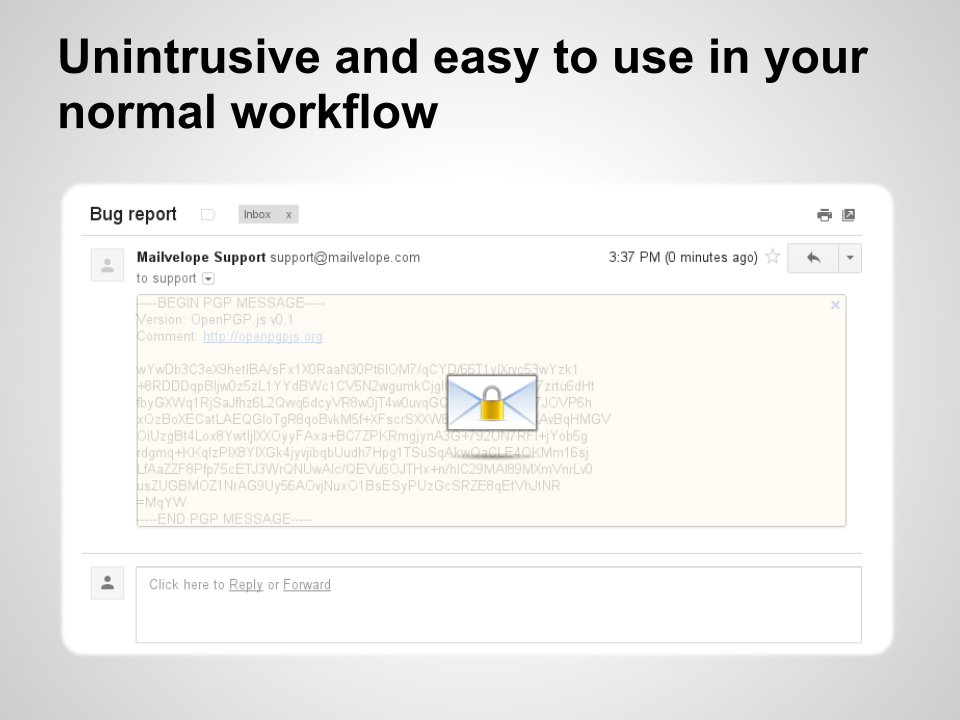
Mailvelope
Mailvelope is a Chrome and Firefox browser extension that can encrypt emails with OpenPGP and is compatible with Gmail, Outlook, GMX, Yahoo Mail, and many other email services. The extension encrypts the emails in the browser, and users are responsible for taking care of their private keys.
That means that if you format your computer without saving the private keyword, you will lose it, and you would need to create a new private and public key that you need to share with others all over again.
It also means that you need to get all of your contacts’ OpenPGP public keys one by one. There are some ways to make the process easier, such as encouraging all of your friends to use a keyserver such as Keybase. This service ties identities to OpenPGP public keys. Mailvelope also announced its own key server recently, which means that it should be easier to find your friends’ public keys straight from Mailvelope.
One recommendation would be to always write messages in the external windows Mailvelope presents when you want to send a new message, because services such as Gmail and Yahoo can save copies of the emails as you write them. When that happens, the message is already “leaked” before you even get a chance to press the Mailvelope encrypt button.
Mailvelope uses standard OpenPGP encryption, so the messages could also be decrypted in other OpenPGP email clients, as long as you import the private key in them. The same is true in reverse: Mailvelope can also decrypt messages encrypted by other OpenPGP clients.
Other Options
There are multiple other OpenPGP-based email services out there, but for most users, ProtonMail is probably one of the more modern-looking, as well as the easiest to use, given that the company manages public keys automatically and syncs your (encrypted) private keys across devices. The company is based in Switzerland, where privacy laws are stronger and more respected than in most other countries, which may also help you feel more trusting of the service.
ProtonMail supports all modern browsers as well as Android and iOS. For users looking to leave Yahoo Mail, ProtonMail would be a good alternative, as it works just like any other modern email service, but it also gives users the option to encrypt their emails end-to-end.
For those who still can’t switch away from their favorite email service (whether it’s Gmail, Outlook, or even Yahoo Mail), Mailvelope is a sound and easy way to communicate privately with friends. It’s not quite as easy to use as ProtonMail because you still have to manage public and private keys, but after the initial setup, things should go much more smoothly. It’s also still significantly easier to use than most traditional PGP applications.
Lucian Armasu is a Contributing Writer for Tom's Hardware US. He covers software news and the issues surrounding privacy and security.
-
el_encryptor The combination of Mozilla Thunderbird and Enigmail is also an excellent choiceReply
https://emailselfdefense.fsf.org/en/ -
clonazepam I'm pretty sure I recall when this all went down. I wasn't able to log into Yahoo Mail anymore because they basically forced a password to be entered, as well as I believe rolling out new features including authentication.Reply
It's not primary and I typically only use it for notifications. -
Tanyac So what's a e2ee mail service that is free and plugs into Thunderbird so I don't have to use a browser to read my email. I can just run Thunderbird for all my accounts?Reply -
Glen_9 Topmail (www.topmail.com) is also a great new alternative to Proton Mail. I use it and have had no issue with privacy since switching, it also has OpenPGP encryption and is easy to use.Reply -
Eric33 If you use Outlook, the best option for Email encryption is the gpg4o plugin. There is a free version out now.Reply -
Wild_1 We need an alternative, and that's for sure - but to say protonmail is the only viable option, is not correct. There are tons of services out there which are fighting against mass surveillance and are giving users more rich and better features (for e.g., https://www.mailfence.com/, https://www.tutanota.com/, ...)Reply