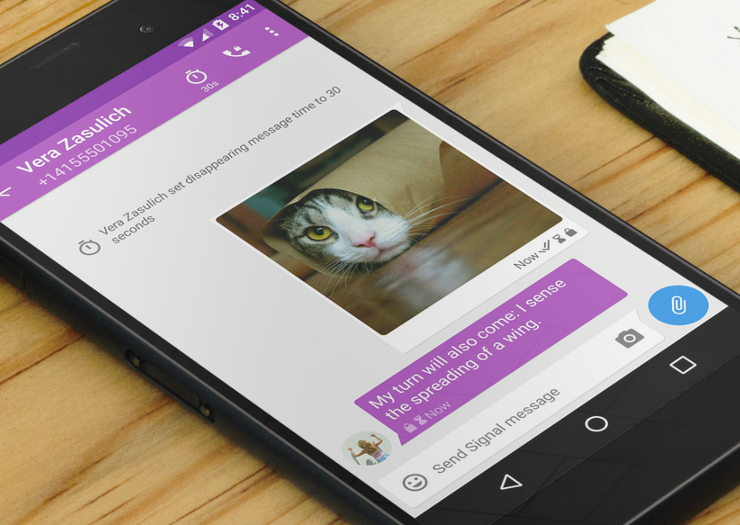
End-To-End Encrypted Signal App Now Includes Snapchat-Like 'Disappearing Messages'
Open Whisper Systems, the nonprofit behind the Signal end-to-end encrypted chat application, has announced that the app received a new, long-awaited feature: Snapchat-like "disappearing messages."
The Signal app brought us the originally-named "Axolotl" end-to-end encryption (E2EE) protocol, which was later renamed as the "Signal" protocol. It was a major upgrade from the older, but also popular, E2EE protocol called "OTR" (Off The Record).
Signal supports forward secrecy (key rotation), just like OTR. However, unlike OTR, it also supports asynchronous messages (you don’t have to be online to receive a message), and group messages are encrypted end-to-end, as well.
The protocol is generally seen as state-of-the-art by security and cryptography experts, which is why it’s already been adopted by apps such as Silent Circle's "Silent Phone," WhatsApp, Google's Allo, and Facebook Messenger (although for the latter two, it has to be enabled manually for each conversation), as well as by some presidential candidates.
E2EE Vs. Self-Destructing Messages
For a long time, chat applications with disappearing or self-destructing messages have been considered more “privacy-friendly,” certainly by many mainstream users. The idea of self-destructing messages has been made popular by various spy movies.
This has caused many to wonder whether an app like Signal with strong E2EE but no disappearing messages is more privacy-friendly than one such as Snapchat, which doesn’t use end-to-end encryption at all, but supports self-destructing messages by default.
If we had to choose only one of them, apps with E2EE should win almost every time, at least if we’re talking about sophisticated attackers trying to spy on our communications, and not about jealous girlfriends or boyfriends looking through our phones (although Signal itself can protect against that, too, with a password lock).
Get Tom's Hardware's best news and in-depth reviews, straight to your inbox.
Disappearing messages still have to arrive to the other user first, across the network, before the self-destruct sequence is automatically initiated for apps such as Snapchat. If a sophisticated attacker can intercept that message through a MITM (Man-In-The-Middle) attack, then the message will become available to them. Such attacks can also be performed at scale for millions of users, whereas end-to-end encrypted messages can be recovered only by hacking each device.
Signal’s "Disappearing Messages"
Disappearing messages do have quite a bit of real value in terms of the security and privacy they actually provide, beyond their perceived value of being “spy-movie-level-ultra-secret” messages.
Messages that are stored anywhere risk being stolen or leaked without at least nominal “data hygiene.” However, even if you always delete your own stored messages on a regular basis, the messages will still remain on the devices of the other members of the conversations. Signal’s disappearing messages feature ensures that the messages are deleted from all devices in the conversation, once any one of the parties enables a timer. The timer is deactivated by default, but it can be enabled in the app’s setting for anywhere from five seconds to one week.
After that, the messages affected by the timer will show a “full” sand glass icon that becomes increasingly emptier as the allotted time passes. When it’s fully empty, the messages will disappear from all of the parties’ devices.
Easier Security Code Verification
Signal has also been updated with a new format for cryptographic user verification. Until recently, the app used a hexadecimal numbers format, which was harder to spell out over the phone. The new change also brings support for QR codes, which makes verification easier when the users meet face-to-face. These verification features were also implemented in WhatsApp earlier this year.
Cryptographic verification is necessary for true privacy and message security, because sophisticated attackers that can do MITM attacks could still try to pretend they are the people you’re trying to contact. The messages would then remain encrypted, but they would be delivered to the wrong people.
The disappearing messages and “safety numbers” feature is now available for all Android, iOS, and desktop Signal users.
Lucian Armasu is a Contributing Writer for Tom's Hardware US. He covers software news and the issues surrounding privacy and security.
-
tom10167 Sick. But can someone explain the value of the QR scan thing? If we're in person can't I just verify by sending them a message and seeing if they got it?Reply -
adgjlsfhk Theoretically the message you send them could be intercepted and changed, whereas changing a qr code requires device access.Reply -
Lucian Armasu Reply18722182 said:Sick. But can someone explain the value of the QR scan thing? If we're in person can't I just verify by sending them a message and seeing if they got it?
You can. Or you can spell out your security code over the phone, too, and see if it matches with the one they have for you.
But you'd have to do this every time, because someone could still hack the encrypted channel connection, and then pretend it's your friend (while you'd still be seeing your friend's picture and number, and so on).
What the QR code scanning does is that after you do it, the app will warn you if you're not talking to the same person for which you verified the code (strangely enough, you have to enable this manually in WhatsApp's account settings). If another person interposes between you and your friend, they would have a different security code, so you will be warned that the person you're now talking to has a different code.
However, you may also get this warning if your friend uninstalls and then reinstalls the app, as they will get a new code. So you'll have to talk to them to make sure it's still them, and then verify the code again.
If you can't meet in person, you could take a screenshot of each other's qr codes as well, and send them over what you believe is a secure connection, such as the app itself (which should use TLS or Noise encryption, in WhatsApp/Signal's case), and then put that picture on your PC and scan it. You may try doing it over email as well, but preferably over PGP, or at least if you both have Gmail, which tends to have better TLS encryption than most other email services.
But to ensure someone else didn't hack that connection, you'd have to check with them right then if they received the qr code.
If your connection is actively monitored and the attacker is prepared, they may still be able to capture the screenshot, and verify themselves with it, while sending your friend another one. So doing it in person is still the safest. But for people that you can't meet in person anytime soon, it may still be worth giving this a shot.