Google’s 2-Step Verification Now Supports FIDO “Universal 2nd Factor” Open Standard
Get Tom's Hardware's best news and in-depth reviews, straight to your inbox.
You are now subscribed
Your newsletter sign-up was successful
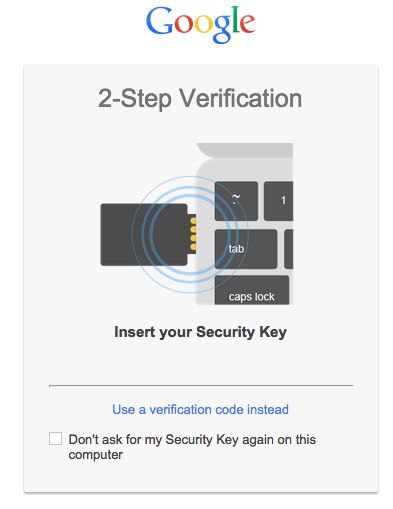
Today, Google announced that the 2-Step Verification security for its Google accounts will get even stronger thanks to new support for the Universal 2nd Factor (U2F, for short) open standard created by the FIDO Alliance.
The FIDO Alliance is a non-profit organization, founded in 2012, working on interoperable open standards protocols for secure authentication. Companies such as Google, Microsoft, Samsung, ARM, Qualcomm and others have already joined this group. The FIDO Alliance aims to make it easy to securely authenticate to devices whether it's through USB keys (such as Yubikey NEO), fingerprint or face scanning, voice recognition, or other methods.
The main advantage of using a USB "Security Key" (as Google calls it) over typing a verification code that you may have gotten from the SMS-based 2-step verification or the Google Authenticator app is that it can protect you against phishing. The USB Security Key will only work with Google's websites if it recognizes them.
Article continues belowRight now, though, Google's websites will only accept this login method within the Chrome browser (version 38 or later), but Google hopes other browsers will adopt it soon, too. Mozilla is usually on the same page with Google when it comes to security and open standards, and Microsoft has already joined the group as well, so we can probably expect support for the FIDO U2F in the next version of Internet Explorer.
Apple could be the last one to hold out on adopting any of the standards from the FIDO Alliance, considering the company now has its own protocol for fingerprint scanning. Apple has recently started allowing iPhone users to pay for online purchases by using Touch ID, and in the future it may also add Touch ID to its Macbooks.
USB keys are probably not going to become mainstream, which is why this functionality should probably be built into smartwatches, which can then connect through NFC and authenticate laptops or mobile devices. Google's Android 5.0 operating system already allows something similar, but it only works to unlock the devices, not log in to any websites. Another disadvantage of USB keys is that they can't work with mobile devices, unlike the NFC-based smartwatch solution.
Still, for people who want to be extra-secure and don't want to risk having their smartwatches compromised by malware, the USB keys are a good solution, especially if most browsers are going to adopt an interoperable standard in the near future.
Get Tom's Hardware's best news and in-depth reviews, straight to your inbox.
Follow us @tomshardware, on Facebook and on Google+.
Lucian Armasu is a Contributing Writer for Tom's Hardware US. He covers software news and the issues surrounding privacy and security.
-
ubercake When your fingerprint becomes data or your voiceprint becomes data, it can be hacked. Hacking it will simply require going after different data.Reply -
ChronosVRdS "USB keys are probably not going to become mainstream", I disagree, Yubikey NEO is USB Key and NFC enabled, kind 2-in-1 solution, it works with your pc and mobile! No battery, better protection, less bulky, and way cheaper than a smartwatch!Reply -
Solandri ReplyWhen your fingerprint becomes data or your voiceprint becomes data, it can be hacked. Hacking it will simply require going after different data.
That's why something like a USB key can work. Designed properly, it doesn't rely on data. It relies on a algorithm which can't be read over the USB connection.
You hard-code a private key into the USB stick's hardware. You design it so there is no way to access this private key over the USB connection, and trying to access it directly destroys the circuitry. Only data can be sent to and read from the USB connection - all computations are handled within the USB stick's hardware.
Google then encrypts a data packet containing a challenge using its private key and the USB stick's public key. It transmits that data packet to your computer, which sends it to the USB stick. The USB stick decrypts it using its private key and Google's public key. It is now able to read the challenge.
Your computer then generates the appropriate response (e.g. you type in your gmail password), and encrypts it with its private key and Google's public key. That encrypted data is transmitted back to Google which decrypts it using its private key and the USB stick's public key.
If the decrypted data contains the correct response to the challenge, then Google has confirmed that the actual physical USB stick they sent the challenge to was in fact the one which sent the response.