At Pwn2Own, Chrome Is First, IE Last In Browser Security (Updated)
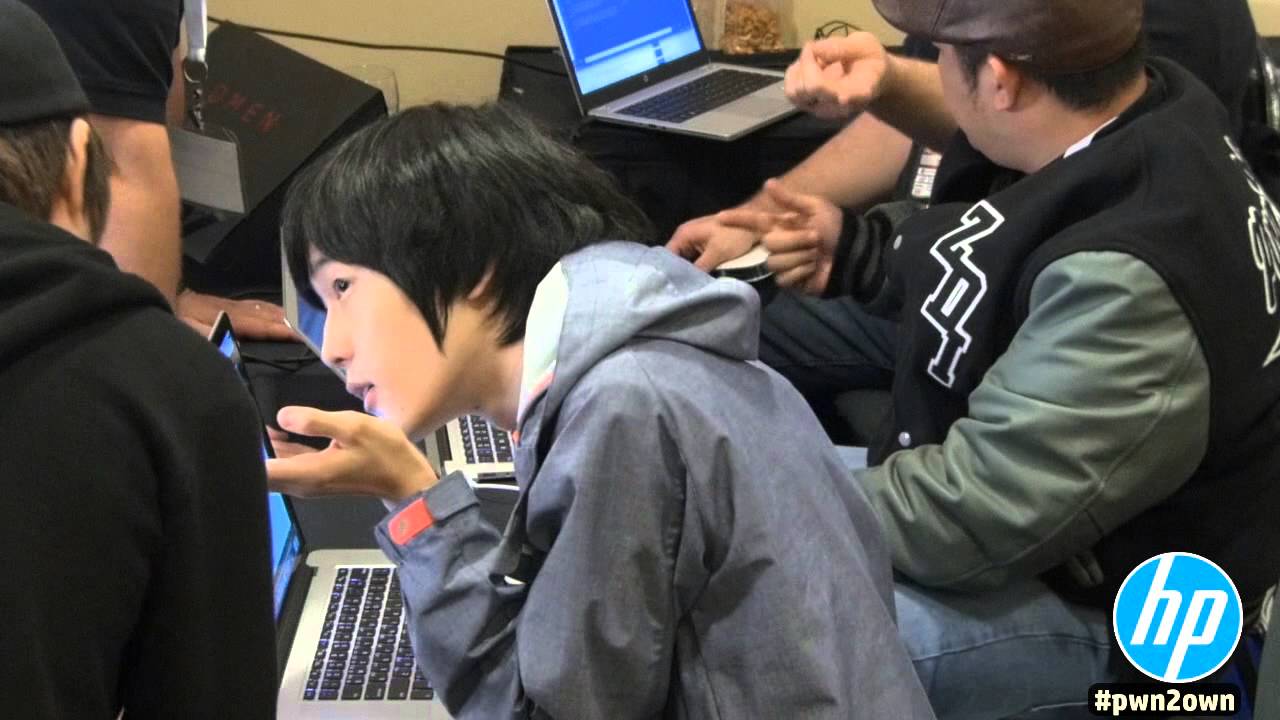
Pwn2Own is a browser security competition where security researchers who have been working on finding vulnerabilities in web browsers for the past year try to win significant monetary prizes from companies such as Google, Microsoft, Apple and Mozilla.
The flaws are usually found after months of work. At Pwn2Own they have only 30 minutes to demonstrate their hacking capability and beat the browsers' security before the others in the competition. The first to show a browser exploit in the given timeframe wins the prize. Multiple such prizes are given throughout the Pwn2Own competition.
In the second day of Pwn2Own, security researchers managed to expose multiple vulnerabilities. All of the participating web browsers were ultimately hacked. However, Chrome only had one flaw discovered, and writing the exploit for it was the hardest, according to the researcher who managed to do it.
Internet Explorer was the least secure browser of the bunch, with five vulnerabilities found. The researchers also found five vulnerabilities in the Windows operating system.
5 bugs in the Windows operating system4 bugs in Internet Explorer 113 bugs in Mozilla Firefox3 bugs in Adobe Reader3 bugs in Adobe Flash2 bugs in Apple Safari1 bug in Google Chrome
A total of $557,500 was paid out to researchers. Korean Jung Hoon Lee who wrote the 2,000 lines of code exploit for Chrome was also the one to hack into some of the other browsers, managing to take home almost half of the total payout for himself. Lee won $225,000 at the Pwn2Own competition in bounty prizes, of which $110,000 he got in just two minutes.
Over the past few years, IE and Firefox have traded off being in last place, but Chrome is usually consistently the one with the least vulnerabilities. Google created Chrome from the beginning with security in mind (the process sandbox, as well as other security features), so it's not too surprising to see it again be the most robust.
Get Tom's Hardware's best news and in-depth reviews, straight to your inbox.
IE on the other hand has too much legacy code it has to worry about, but hopefully things will change in terms of security as well if Microsoft's new browser, "Project Spartan," has a more prominent role in Windows 10.
Mozilla also intends to replace more parts of its browser with components written in the memory-safe Rust language, which can help protect against common security vulnerabilities. However, a few more years will probably pass until that happens.
Update, 3/23/15, 7:10am: Mozilla Security Lead Daniel Veditz reached out to us to note that Mozilla patched Firefox as soon as the company learned about the Pwn2own exploits. He said that Firefox version 36.0.4 took care of the same-origin violation used in the Pwn2own exploit, while the other vulnerability, which he said was not exploitable on its own, will be patched in Firefox version 37.
Follow us @tomshardware, on Facebook and on Google+.
Lucian Armasu is a Contributing Writer for Tom's Hardware US. He covers software news and the issues surrounding privacy and security.
-
dgingeri They sure show one of the major reasons I hate Adobe software on that list. Of course, that's just one reason. Copy protection software that can cause a system to fail to boot if the secret alternative data stream gets damaged is another one.Reply
I give Microsoft a pass on this, considering they're far and away much better than Adobe on anything. -
kinggremlin So, they all lost. Ranking them when they all got hacked is like having a ship sink, killing everyone on board, and ranking the people by who drowned the least.Reply -
turkey3_scratch This is why people should stay away from Internet Explorer. It is usually the non-tech-savvy consumer using IE who gets the viruses from exploits on websites.Reply -
dgingeri I've managed to convince my family to use Firefox or Chrome. Most of them use Chrome. I've done well with the family.Reply -
op8 I've been trying to get my family to move to Chrome from Firefox for ages now but it's a a hassle for them, seeing as it was me that convinced them to move away from IE to Firefox in the first place. Next step is to get them to use TOR, but I doubt that will ever happen.Reply -
ayushde Now I am not a security expert, so I can't comment on the security. But I've been using IE11 for quite some time now. And all I can say is that in terms of day to day user experience it is not one bit behind other browsers like chrome. I've tried moving to chrome, but I find the two finger scrolling (I use a laptop) on chrome to be extremely janky as compared to the buttery smoothness of IE.Reply -
dusty13 tiny nitpick ... according to the list it was 4 bugs in IE, according to the text 5 ... what was it? (i will be interested to see how spartan will do next year.)Reply
and another thing: chrome only is the most secure browser if you do not install any addons at all.
chrome does not suffer from many bugs on its own but you have to fit it with a ton of addons to make it useful ... at which point it is about as secure as a blast door made of swiss cheese, because sadly they seem to fail at controlling addon security. yes addons are not part of the code google provides but they become their problem the second they actually impede their browsers security.
taking this into account safari probably would take away the win if this was a real-life test scenario. -
silverblue Firefox seems to crash far too much nowadays which puts me off more than its performance in hacking tests. As for IE, there are too many websites that only work properly with IE, some going as far as to suggest your browser is outdated (!).Reply -
Cryio ReplyFirefox seems to crash far too much nowadays which puts me off more than its performance in hacking tests. As for IE, there are too many websites that only work properly with IE, some going as far as to suggest your browser is outdated (!).
Well, until Firefox doesn't gets their stuff together and implement multithreading rendering already, it will be a pain in the ass until 2016. By their schedule, multithreading is scheduled to be the 1st or 2nd Firefox version to be released in 2016.