Another Exploit Hits WD My Book Live Owners
Data Loss and root privilege woes for WD My Book Live owners
Get Tom's Hardware's best news and in-depth reviews, straight to your inbox.
You are now subscribed
Your newsletter sign-up was successful
While it will come as no comfort to those who had their Western Digital My Book Live NAS drives wiped last week, it seems they were attacked by a combination of two exploits, and possibly caught in the fallout of a rivalry between two different teams of hackers.
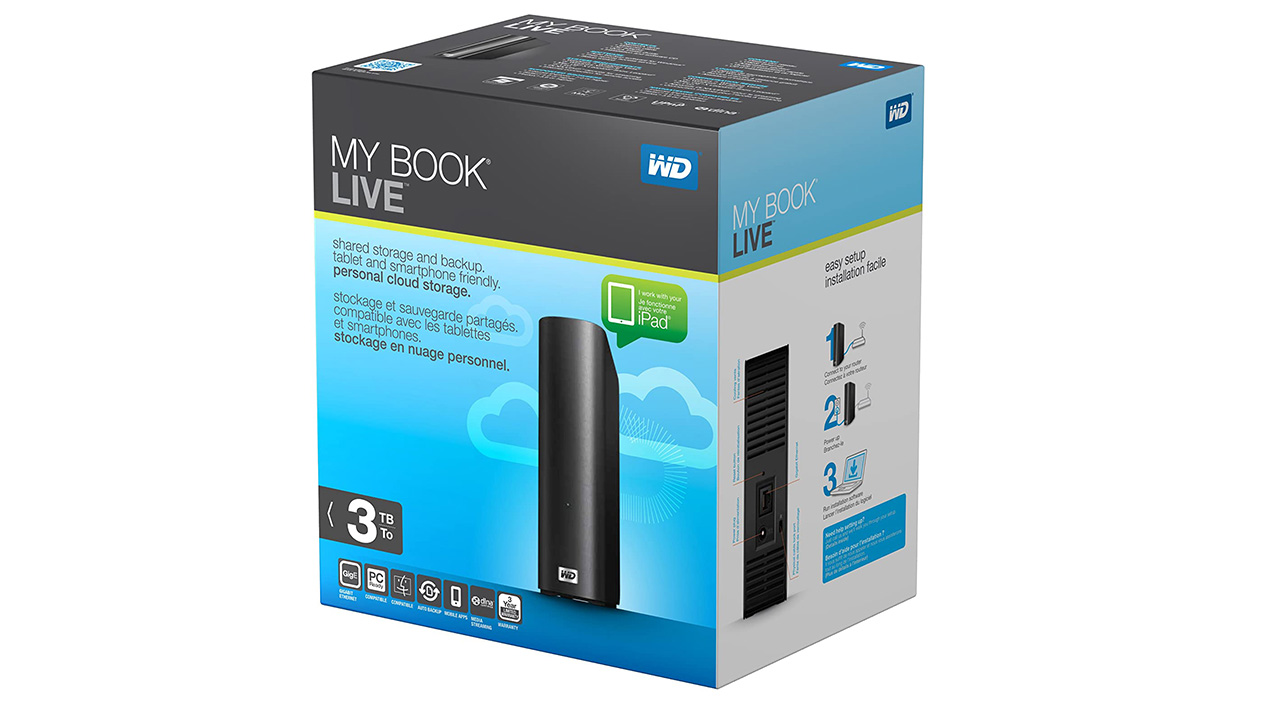
Initially, after the news broke on Friday, it was thought a known exploit from 2018 was to blame, allowing attackers to gain root access to the devices. However, it now seems that a previously unknown exploit was also triggered, allowing hackers to remotely perform a factory reset without a password and to install a malicious binary file.
A statement from Western Digital, updated today, reads: “My Book Live and My Book Live Duo devices are under attack by exploitation of multiple vulnerabilities present in the device ... The My Book Live firmware is vulnerable to a remotely exploitable command injection vulnerability when the device has remote access enabled. This vulnerability may be exploited to run arbitrary commands with root privileges. Additionally, the My Book Live is vulnerable to an unauthenticated factory reset operation which allows an attacker to factory reset the device without authentication. The unauthenticated factory reset vulnerability [has] been assigned CVE-2021-35941.”
Analysis of WD’s firmware suggests code meant to prevent the issue had been commented out, preventing it from running, by WD itself, and an authentication type was not added to component_config.php which results in the drives not asking for authentication before performing the factory reset.
The question then arises of why one hacker would use two different exploits, particularly an undocumented authentication bypass when they already had root access through the command injection vulnerability, with venerable tech site Ars Technica speculating that more than one group could be at work here, with one bunch of bad guys trying to take over, or sabotage, another’s botnet.
Western Digital has responded admirably, offering data recovery services beginning in July, and a trade-in program to switch the obsolete My Book Live drives for more modern My Cloud devices.
If you own one of the affected devices, do not connect it to the Internet and contact Western Digital for support.
Get Tom's Hardware's best news and in-depth reviews, straight to your inbox.

Ian Evenden is a UK-based news writer for Tom’s Hardware US. He’ll write about anything, but stories about Raspberry Pi and DIY robots seem to find their way to him.
-
tomnewb Does anyone know if this also affects the WD My Cloud devices? or is just the My Book Live?Reply -
hotaru251 Reply
no.dehjomz said:Would the windows 11 TPM requirement have prevented this ?? I doubt it.
many modern mb have it built in or optino to add one on.
If TPM could stop this they'd basically always be used (as it would be a selling point they would brag about) -
spongiemaster Reply
Just the old My Book Live. WD is offering My Cloud devices as a replacement, so one would certainly hope they aren't affected as well.tomnewb said:Does anyone know if this also affects the WD My Cloud devices? or is just the My Book Live? -
mikewinddale Replydehjomz said:Would the windows 11 TPM requirement have prevented this ?? I doubt it.
A TPM basically secures a password. But WD commented out the code that requires a password. So even if WD had secured the password in a TPM, it wouldn't help.
(Not to mention the fact that Windows Hello uses a TPM to secure Windows-related passwords and credentials. WD uses its own software to administer the drive, so Windows Hello and other Windows-related security procedures wouldn't have even come into play.)
Microsoft never claimed that a TPM is a magical device that solves all security issues whatsoever. It's simply one way of making certain things more secure than they otherwise would be.
You might as well say that nobody should wear a seatbelt because it won't save you if you crash at 120 mph. Sure, but what if you crash at 60 mph?
Just because a security or safety device is not 100% effective in all imaginable circumstances doesn't mean it isn't valuable.