Another AMD Zen 'Secure Encrypted Virtualization' Vulnerability Demonstrated by Researchers
But it's dependent on physical access to the actual platform.
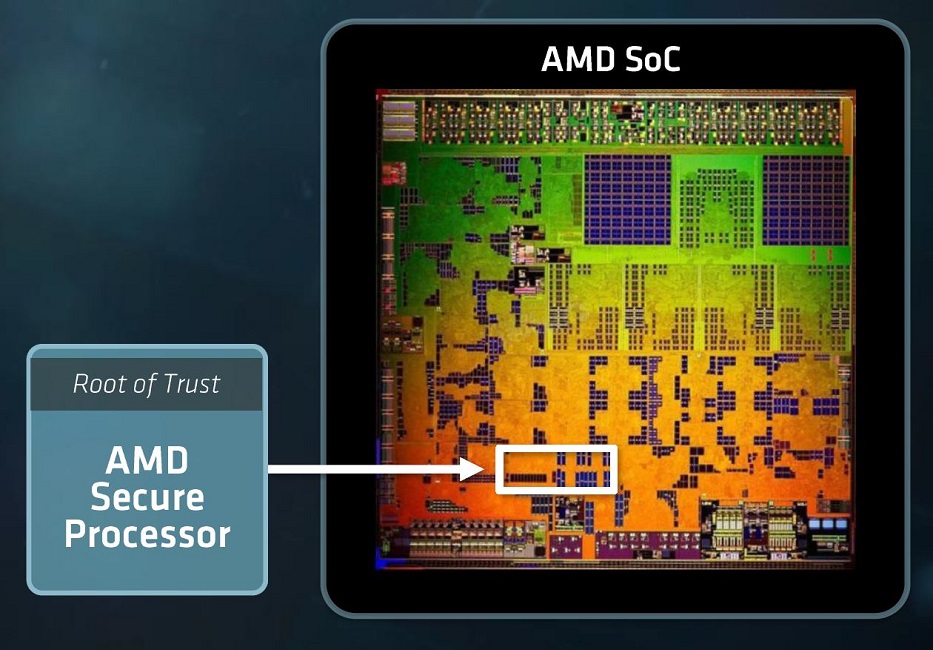
A team of security researchers with Cornell University have demonstrated a proof of concept attack on AMD's Secure Encrypted Virtualization (SEV) technology, leveraging the Zen-integrated AMD Secure Processor (AMD-SP) to achieve full system access.
The technique requires physical access to the AMD system and is based on a voltage glitching attack that allows a bad actor to actually deploy custom SEV firmware, which would, in turn, allow the decryption of all Virtual Machine (VM)-bound information. The vulnerability is executable on Zen 1 through Zen 3. Previously, part of AMD's claim to fame was that Zen 2 and Zen 3 were free from any vulnerabilities of this kind.
The team was led by Robert Buhren, a security researcher who has already demonstrated a series of AMD SEV flaws. The requirement for physical access means that this vulnerability isn't of particular concern to most mainstream users. However, the detailed technique shows yet another way for a rogue actor with physical hardware access to a company's infrastructure to execute malicious code that bypasses all of AMD's protection mechanisms for their Zen microarchitectures. This vulnerability stands on its own, in the sense that the voltage modulation attack doesn't rely on any other existing exploits.
That AMD's Secure Processor (basically an ARM-powered CPU integrated into AMD's Zen design) was the target of this exploit is blow to AMD - the AMD-SP was specifically designed to protect AMD's customers from such attacks, which could be carried out by rogue system administrators. This is of particular concern in cloud-powered environments, since it means that companies running their services on an instanced cloud provider have to trust not only the provider itself, but also their technicians (whether they're subcontracted or not). It's another small knife cut on AMD's attempts to steal server market share from Intel, though it's still a far cry from the thousand cuts one estimates might be required to render AMD's current solutions unpalatable on the basis of security concerns. If anything, Intel currently features a worse security track record when it comes to the number and severity of its product's (already public) vulnerabilities.
Get Tom's Hardware's best news and in-depth reviews, straight to your inbox.

Francisco Pires is a freelance news writer for Tom's Hardware with a soft side for quantum computing.
-
jgraham11 Not only do you need physical access you must of modified the motherboard to vary the voltage being supplied to the processor. This article is misleading in that the motherboard voltage modulation is required and brushed over and only physical access is stated which is not the same as having server covers removed and the soldering iron is out... I don't think this is much of a real threat.Reply
Not even in the same realm as Intel bugs, some can be executed just by visiting a website. Keep your systems updated! -
USAFRet Reply
And the theoretical drive by for the Intel was also vastly overrated.jgraham11 said:Not even in the same realm as Intel bugs, some can be executed just by visiting a website. Keep your systems updated!
We only see this several years after the thing became public.
https://therecord.media/first-fully-weaponized-spectre-exploit-discovered-online/ -
escksu Replyjgraham11 said:Not only do you need physical access you must of modified the motherboard to vary the voltage being supplied to the processor. This article is misleading in that the motherboard voltage modulation is required and brushed over and only physical access is stated which is not the same as having server covers removed and the soldering iron is out... I don't think this is much of a real threat.
Not even in the same realm as Intel bugs, some can be executed just by visiting a website. Keep your systems updated!
You dont need a modified motherboard to vary voltage today. All boards are able to control the clockspeed and voltage on both BIOS and OS level. Physcial access. Again, its not that difficult because administrators arent the only threats. You still need people to service your servers, racks (Eg. wiring, hardware replacement). Even server rooms (eg. lights, aircondition, ducts servicing).
