New Load Value Injection Vulnerability Found In Intel Chips
Another day, another vulnerability
Get Tom's Hardware's best news and in-depth reviews, straight to your inbox.
You are now subscribed
Your newsletter sign-up was successful
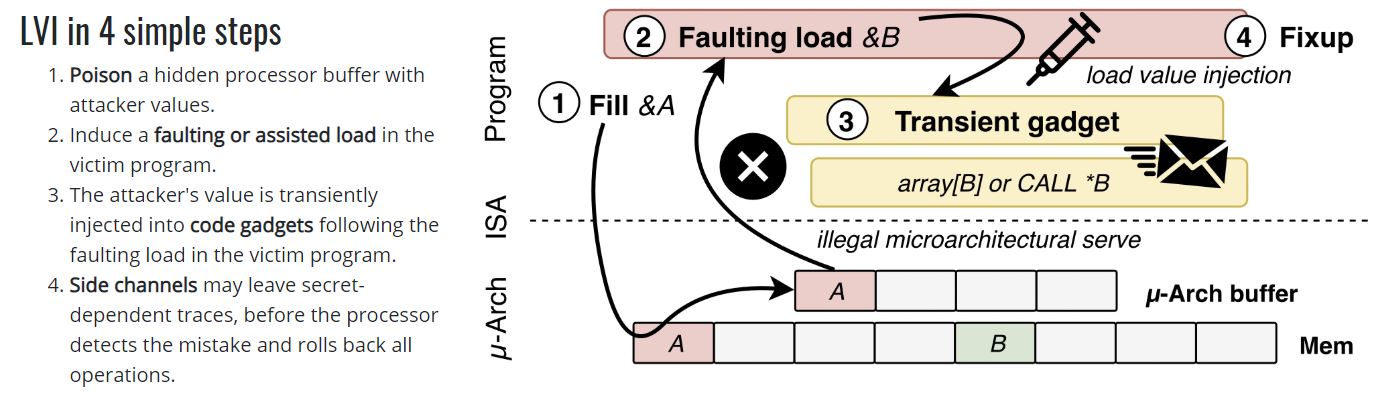
Intel's chips have faced an onslaught of new vulnerabilities discovered by crafty researchers, and today finds the company facing yet another new flaw, Load Value Injection (LVI), that a press release from Bitdefender describes as "particularly devastating" for servers in the data center. LVI impacts all Core families spanning from the third-generation Ivy Bridge chips to the 10th-generation Comet Lake processors.
According to statements from the researchers to ZDNet, the attack builds upon the Meltdown vulnerabilities that Intel already patched in software, but the LVI still works on systems with the requisite software fixes. As such, Intel will reportedly need to employ hardware fixes to fully block the LVI attack vector.
According to experimental fixes employed by the researchers, performance reductions from potential mitigations could vary from 2x to 19x based upon workload, but that could be offset with hardware-based fixes in new silicon.
Here is a quick breakdown (video):
Notably, the vulnerability (CVE-2020-0551) is said to "allow attackers to inject rogue values into certain microarchitectural structures, which are then used by the victim, which may lead to revealing secrets." This allows for data theft, but can purportedly reveal encryption or passwords kept in memory, which could then allow an attacker to assume control of the target machine.
The researchers contend the attack, which requires slipping data into the SGX Enclave, could theoretically be executed via JavaScript. That means physical access to the machine isn't required, but the researchers haven't tested that attack vector yet. For multi-tenant environments, like those found in cloud-based instances, the attack could allow eavesdropping on neighboring instances. However, the researchers also note that the vulnerability is extremely hard to exploit, meaning it isn't an imminent threat to the majority of users.
Intel has published a full analysis of the LVI flaw, stating that "Due to the numerous, complex requirements that must be satisfied to implement the LVI method successfully, LVI is not a practical exploit in real-world environments where the OS and VMM are trusted[..] Accordingly, system administrators and application developers should carefully consider the particular threat model applicable to their systems when deciding whether and where to mitigate LVI."
Get Tom's Hardware's best news and in-depth reviews, straight to your inbox.
The flaw was discovered by Bitdefender and verified by a team of researchers that have exposed major flaws in Intel, AMD, ARM, and IBM architectures in the past. Bitdefender then created a synthetic proof of concept that it posted to GitHub. The researchers were funded by Intel, AMD, and ARM.
Bitdefender claims it shared the attack with Intel on Feb 10, 2020. The company also claims that existing mitigations for Meltdown, Spectre, and MDS are insufficient for mitigating the new flaw and that a full fix currently requires disabling hyper-threading or purchasing new hardware with in-silicon fixes. For now, that consists of the Ice Lake family and Atom processors that don't fall into the Silvermont and Airmont families.
Intel provided us with the following statements regarding the LV1 vulnerabilities:
Load Value Injection Statement: “Researchers have identified a new mechanism referred to as Load Value Injection (LVI). Due to the numerous complex requirements that must be satisfied to successfully carry out, Intel does not believe LVI is a practical method in real world environments where the OS and VMM are trusted. New mitigation guidance and tools for LVI are available now and work in conjunction with previously released mitigations to substantively reduce the overall attack surface. We thank the researchers who worked with us, and our industry partners for their contributions on the coordinated disclosure of this issue.”
Statement Specific to SGX: “To mitigate the potential exploits of Load Value Injection (LVI) on platforms and applications utilizing Intel SGX, Intel is releasing updates to the SGX Platform Software and SDK starting today. The Intel SGX SDK includes guidance on how to mitigate LVI for Intel SGX application developers. Intel has likewise worked with our industry partners to make application compiler options available and will conduct an SGX TCB Recovery. Refer to the Intel SGX Attestation Technical Details for more information.”

Paul Alcorn is the Editor-in-Chief for Tom's Hardware US. He also writes news and reviews on CPUs, storage, and enterprise hardware.
-
st379 You put Intel name after the longest headline i have ever seen that no one will notice and also it is on the bottom of the news.Reply
Who is sponsoring tomshardware? You should tell your readers if you are getting money from Intel/Amd/Nvidia.
Be fair... I am not saying don't reveal any problem but you make it very clear that this site or publishers getting money from some companies, you should say which.
Oh and Paul no follow up on this one? On Amd you follow very closely. -
Paul Alcorn Replyst379 said:You put Intel name after the longest headline i have ever seen that no one will notice and also it is on the bottom of the news.
Who is sponsoring tomshardware? You should tell your readers if you are getting money from Intel/Amd/Nvidia.
Be fair... I am not saying don't reveal any problem but you make it very clear that this site or publishers getting money from some companies, you should say which.
Oh and Paul no follow up on this one? On Amd you follow very closely.
Intel's comments on the matter are on the page. in two different places. There are also links to their advisory and Intel's 31-page breakdown of the issue and how to fix it. And a link to the impacted processors. They have more material than a one-para statement, by far. AMD had zero information on its website until 24 hours after the paper posted, and didn't respond to further queries until another 24 hours after that (granted, it was a weekend)
Intel had an encyclopedia of data at the very time the vulnerability was announced, so I'm don't think it needs further follow up. In either case, their responses are already in the article several times.
57The article is also pinned to the top 5 articles, so it appears in the main part of the page even though it has slipped down the queue in the news feed. As you can see, it is listed twice.
I have no idea which advertisers have contracts, we aren't involved in that. I do know that, contrary to popular belief, it is rare for Intel, AMD or Nvidia to advertise on any website. -
st379 I have 200 Intel vulnerabilities that are not patched on 2 of my pcs.Reply
I am not too worried because I know how to avoid problems.
The Amd article was in the headline for a long period of time.
You raised many concerns about Amd and i doubt Intel will patch my cpu from 3 years ago on my notebook.
So yes... the corona virus mass panic on the Amd article was not necessary.
It is just how you treated both articles and the things you wrote.
It was so close when they both published so it was easy to compare and it is just feel a bit off.
When Amd said it was all good and there is nothing to worry about you did another follow up.
Like I said, most of Intel cpu are not patched and never will.
Edit:
I did not say advertise I asked if you or tomshardware are being sponsored by Nvidia/Intel/Amd. -
Paul Alcorn Replyst379 said:I have 200 Intel vulnerabilities that are not patched on 2 of my pcs.
I am not too worried because I know how to avoid problems.
The Amd article was in the headline for a long period of time.
You raised many concerns about Amd and i doubt Intel will patch my cpu from 3 years ago on my notebook.
So yes... the corona virus mass panic on the Amd article was not necessary.
It is just how you treated both articles and the things you wrote.
It was so close when they both published so it was easy to compare and it is just feel a bit off.
When Amd said it was all good and there is nothing to worry about you did another follow up.
Like I said, most of Intel cpu are not patched and never will.
Edit:
I did not say advertise I asked if you or tomshardware are being sponsored by Nvidia/Intel/Amd.
No, to my knowledge we are not sponsored by Intel, AMD or Nvidia.
Yes, we have covered Intel vulnerabilities ad nauseum, to the point that it is like elevator music. I know that some don't bother to read all of these articles, so here is a summation of Intel vs. AMD security:
https://www.tomshardware.com/features/intel-amd-most-secure-processors
Read the conclusion, and look at the table at the end. If one actually takes the time to read the content that we produce, it's silly to claim that we are downplaying Intel's vulnerabilities. The reality is quite the opposite.
In regards to the AMD situation, AMD says its chips are safe from the vulnerabilities, the researchers claim they are not. Intel acknowledges the issues, so there isn't really much more to say than cover the issue and send readers to the resources provided by both Intel and the researchers. -
st379 I remember this article.... I follow only this news site because i used to it and some youtubers for reviews.Reply
This is the only site I get my news from.
I remember your vcore, "Intel claims", about Amd. This article looks really bad.
The athlon 200ge i was a bit suprised. The youtubers with his claims on Amd boost and many other on Amd boost.
I have other articles that looks a bit weird but you did not write them so i am not going to mention them.
All I am saying that there is a feeling this site favours Nvidia and Intel.
Not that it is important but i recently helped my cousin to choose a gpu and I recommended to him Nvidia gtx 1660ti because of Amd drivers issues. I am not a fanboy of any company.
I will choose what is best within my budget. -
Jim90 @PaulAlcorn we're not talking about Intel/Nvidia or AMD literally advertising on the tomshardware website - instead, we're talking about that white elephant increasingly present in large social media gatherings - anti competitive tactics. Guess who has publicly stated last year that they have set aside $3 billion strictly for use in anti competitive practices? - Intel, as anyone following tech will instantly know (e.g. your readership). We all know that it is virtually without doubt that Intel has a very significant presence in large forums with paid shills and competition disruptors. When I see some of the tactics used I try to try to highlight this - just as I did very recently here - very large font sizes used permanently by someone very clearly attacking AMD with every post (in current light you shouldn't allow this for obvious reasons of implication, plus, it's anti-social). Now, are we to be so naive that Nvidia isn't doing the same? - shouldn't we be at least 'vigilant'? Don't worry though, we'll be on the look out for AMD if they try the same!! - since...Reply
Ultimately, it all boils down to this - is competition beneficial for the consumer? does it keep prices kept in check? does it stimulate real innovation accelerated?