Hackers Can Steal Your Smartphone's PIN Via Built-In Motion Sensors
Security experts from the Newcastle University, UK, revealed that the motion sensors built into modern smartphones can make PIN locks virtually useless, as malicious hackers could guess them in up to five tries, at most.
Avoid Using PINs, If Possible
Four- and even six-digit PINs are already trivial to brute-force with GPU-powered password cracking tools. This is why both Apple and Google have limited how many times you can input a PIN to unlock your phone in a given amount of time before you can try again.
The weakness of PINs--and the protection mechanism that Apple has employed in iOS because of it--was also at the core of FBI’s fight against Apple in the San Bernardino case. The law enforcement agency wanted to force Apple to remove those protections so it could easily brute-force the PIN protecting that iPhone’s encrypted storage.
However, according to researchers, the attack they discovered could mean that even that protection mechanism may not be enough anymore. Using the new technique, a malicious actor could guess anyone’s PIN 70% of the time with a single try, or 100% of the time in up to five tries.
If Apple or Google tried to reduce the number of attempts below five, using a PIN may become too cumbersome for smartphone owners, especially if they tend to forget it often. At that point, the companies may have to simply remove the PIN option from their device authentication options and leave only the more secure options in place.
How The Sensor-Based PIN Attack Works
Modern smartphones have plenty of sensors in them such as accelerometers, gyroscopes, barometers, rotation and proximity sensors, and so on. These sensors can be used in gaming as well as fitness applications, so they are quite useful to have in a device that everyone carries with them. However, as the Newcastle University researchers learned, they can also pose security problems unless proper protections are used to prevent abuse.
One of the problems the researchers identified is that only a small number of sensors, such as the GPS and camera sensors, require user permission. The rest can be activated without any action from the user.
Get Tom's Hardware's best news and in-depth reviews, straight to your inbox.
This may be a design choice on Google and Apple’s part, because according to the Newcastle researchers, most smartphone users are only aware of the risks that may come from GPS tracking or the camera being remotely activated.
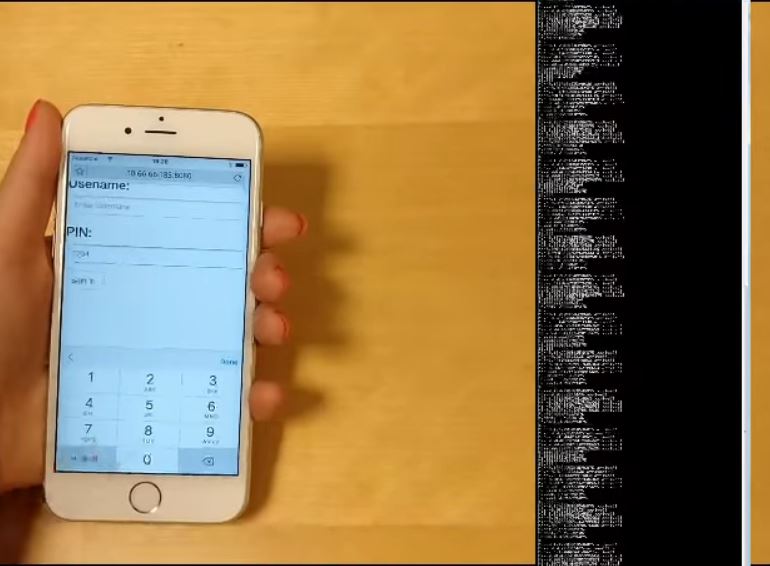
The PIN identification attack works because every touch action on a smartphone, including clicking, scrolling, holding, and tapping, creates a unique orientation and motion trace. An attacker who can gain remote access to that sort of information from the device could also create a profile for the PIN that a user enters on the device.
Alerting OS Vendors
The team of researchers from the Newcastle University alerted Google and Apple about these issues, but it doesn’t look like there will be a quick fix for this, because, as always, there’s a trade-off between security and usability. Requiring permission for every touch on the device is obviously impractical, but perhaps the two companies can find some other ways to further secure your actions from potential attackers.
Dr Maryam Mehrnezhad, who led the research on this issue, had a few tips you can follow if you decide to stick to a PIN on your smartphone:
Make sure you change PINs and passwords regularly so malicious websites can’t start to recognise a pattern.Close background apps when you are not using them and uninstall apps you no longer needKeep your phone operating system and apps up to dateOnly install applications from approved app storesAudit the permissions that apps have on your phoneScrutinise the permission requested by apps before you install them and choose alternatives with more sensible permissions if needed
If all of those suggestions seem like more trouble than they’re worth, you’re probably right. It may be best to stick to using stronger alternatives than PINs such as passwords, or fingerprint authentication, and forget about using PINs for anything.
Lucian Armasu is a Contributing Writer for Tom's Hardware US. He covers software news and the issues surrounding privacy and security.
-
SteveRNG Or make the number layout of the PIN keypad vary. It requires people to remember the numbers and not the pattern but... you're welcome.Reply
First time:
123
456
789
0
Second time:
148
029
356
7
Nth time:
503
429
716
8 -
dstarr3 Boy, hackers are so clever. I would say "If only they used their powers for good," but a lot of times, they do, like this instance. There are so many hackers out there doing their job for no other reason than exposing security exploits so they can be fixed.Reply -
bloodroses Hackers are definitely clever. Luckily most do this without malicious intent, but their methods are used by others to do just that. In many cases, these exploits help keep companies like Google and Apple on their toes to ensure that their devices are safer since the companies more often than not don't foresee the potential problems themselves.Reply
When it comes to the computer/electronics world, nothing is completely secure due to its very nature in itself. -
canadianvice Reply19549095 said:Or make the number layout of the PIN keypad vary. It requires people to remember the numbers and not the pattern but... you're welcome.
First time:
123
456
789
0
Second time:
148
029
356
7
Nth time:
503
429
716
8
My thoughts exactly. A randomizing pin layout makes this whole business moot. However, most smartphones don't operate that way without custom software in my experience, so it's still a valid attack vector.
Personally, I don't do anything on my phone I'm not willing to have compromised, because they're just too damn easy to steal and while most of them are subhuman thugs, evidently there are a lot of hacking options too for those invested enough to try. -
erendofe add the effected sensors to the permission list when installing an app. after that its up to the user really.Reply -
spdragoo http://www.techspot.com/news/68891-researchers-show-how-smartphone-motion-sensors-could-reveal.htmlReply
Just a little bit more information...they had to enter the same PIN 50 times before the system learned how you typed each digit. So you first have to get the malware onto your phone, then you have to type the PIN in enough times for it to start having a chance to recognize (i.e. 50 times before it has that 70% chance to guess).
And the ability for it to recognize the number is going to be affected by:
-- the location of the numbers (i.e. the placement of the numbers on my iPhone's lock screen <> the placement of the numbers on the "full" on-screen keyboard <> the placement of the numbers on the "number pad" on-screen keyboard)
-- how your phone is placed (i.e. sometimes I unlock my phone with the same hand that's holding it, sometimes I hold it in 1 hand while hitting the numbers with my other hand, & sometimes it's just lying on a flat surface when I hit the numbers) -
derekullo So the most secure place to use my phone is an environment with 0g?Reply
Good luck capturing my phone's orientation there.
I ask this half serious / half sarcastic lol. -
Reply19549095 said:Or make the number layout of the PIN keypad vary. It requires people to remember the numbers and not the pattern but... you're welcome.
They already have this on many door locks (like the samsung shs-h700). -
acme64 why would they need your pin when they already have access to the phone? thats like breaking in through a window to pick the lock...Reply -
mrmez Reply19549095 said:Or make the number layout of the PIN keypad vary. It requires people to remember the numbers and not the pattern but... you're welcome.
First time:
123
456
789
0
Second time:
148
029
356
7
Nth time:
503
429
716
8
That's a good short term solution that can be implemented immediately.
Exploiting this does seem like a long shot.
However, I'm still shocked to see how many people have NO lock on their phones, and a lot have these swipe patterns because.... typing is too hard. Seems people will give up security for the slightest convenience.
I still think Apple has the best solution with the fingerprint scanner. Nothing is foolproof obviously, and unlike other phones, there's no swiping your finger, just touch it. If I have any gripe, it's too fast and too accurate. I can't even wake my phone with a registered finger without unlocking it