System Encryption: BitLocker And TrueCrypt Compared
Now that Intel offers hardware-based AES acceleration in a number of its mainstream processors, it's time to take a look at two of the most popular system encryption tools, BitLocker and TruCrypt, both of which are able to harness the hardware feature.
TrueCrypt 6.3a On Windows 7 Ultimate x64
TrueCrypt's site claims the software has been downloaded more than 13 million times. This has to be put into perspective. Compression tools like WinZip are mainstream and universal. They get massive download rates because everybody uses them. Encryption is still in the outer orbit of mainstream awareness. Relatively few people use encryption. It's one of those things that most folks don't seriously consider until they've been burnt by not employing it. So, 13 million TrueCrypt downloads is really a telling sign of this software's popularity.
TrueCrypt is much more flexible than BitLocker. For example, you can create encrypted containers. These containers have to be set to a fixed size, and they can be mounted as individual drives to your system. The system isn't confined to Vista or Windows 7, as with BitLocker. Windows XP, Mac OS X, and Linux are also supported. TrueCrypt actually originated on these non-Windows platforms, so be sure to use version 6 if you want to add encryption to an existing Windows installation.
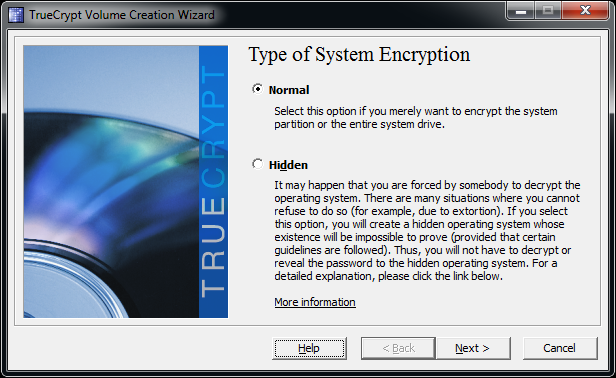
There are a few things to consider before deploying TrueCrypt. First, TrueCrypt doesn't offer any way to recover your encrypted partition if you lose your passphrase. The only option would be a brute force or side channel attack, but if all the governments of the world can't crack AES-256, your odds are pretty slim. TrueCrypt also allows for the creation of hidden partitions and even denying their existance. You could create two encrypted system partitons and hide one of them. The visible one works as a decoy, which you could use regularly to give off the impression that it's your active system. Whether you boot the hidden system or the decoy is decided by the passphrase you type at startup. TrueCrypt offers comprehensive information on running hidden operating systems.
Select whether you want to create a normally encrypted system or an hidden installation.
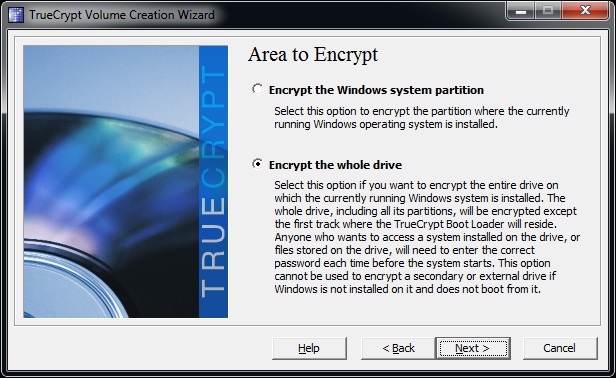
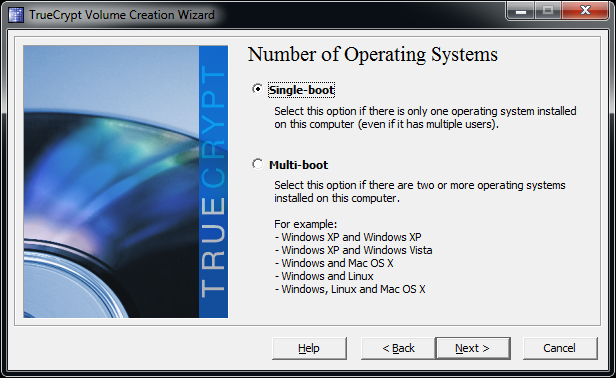
TrueCrypt can also handle multi-boot environments with multiple operating systems installed in parallel.
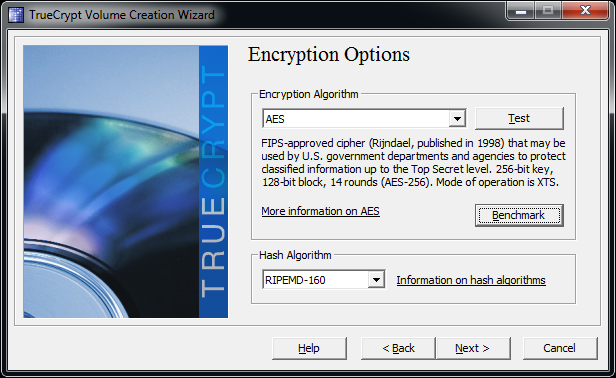
You can choose between several encryption algorithms and hash algorithms.
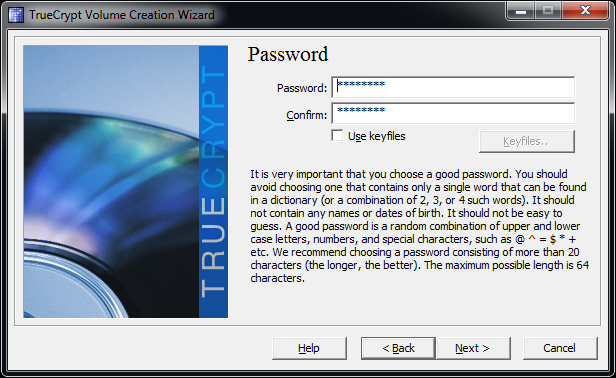
This section is really important, as there is no backdoor to recover forgotten passwords!
Get Tom's Hardware's best news and in-depth reviews, straight to your inbox.
Current page: TrueCrypt 6.3a On Windows 7 Ultimate x64
Prev Page BitLocker On Windows 7 Ultimate x64 Next Page TrueCrypt, Continued