The Fifteen Greatest Hacking Exploits
Famous Hackers
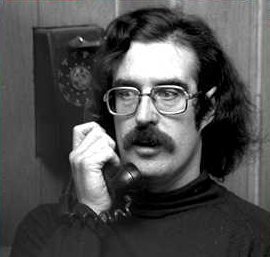
Adrian Lamo, Kevin Mitnick and Kevin Poulsen
Kevin Mitnick
The most famous, and undoubtedly most gifted hacker in history, made a name for himself in 1981 at the tender age of 17 by getting into a phone exchange, which allowed him to redirect subscriber calls in any way he wanted. In 1983, he achieved his first major coup - and also his first arrest - when he accessed a Pentagon computer. It was his repeated offenses that made him a target of the FBI. He was sentenced to five years in prison in the 1990s, but today he is a security consultant and owns his own company: Mitnick Security.
Kevin Poulsen
The current editor-in-chief of Wired was formerly known for rather different activities. In 1983, when he too was only 17 years old, he made his first intrusions into different networks, resulting in a few run-ins with the US legal system. He continued with his illegal activities until his arrest by the FBI in April 1991. In 1994 he was sentenced to four years in prison.
Adrian Lamo
Lamo has certainly driven the highest number of network administrators insane. From Microsoft to Yahoo!, going through Sun Microsystems, MacDonald's, Cingular, AOL or even the New York Times, he is credited with all types of intrusions and corporate security system violations. He has bypassed protections with disconcerting simplicity: during a broadcast of the NBC Nightly News, the host asked him to prove his talents in front of the camera, and he responded by gaining access to the company's internal network in less than five minutes. Today he is an expert in security and enjoys full freedom of movement, after being under the surveillance of US authorities for many years.
Get Tom's Hardware's best news and in-depth reviews, straight to your inbox.
John Draper
Better known as "Cap'n Crunch", Draper was one of the first hackers in history. This moniker comes from the cereal of the same name, inside of which he once discovered a toy whistle (provided as a gift to entice children to ask parents for the cereal). He discovered that he could use the whistle to hack a telephone line and get free phone calls - all that was necessary was to produce a precise tone in the receiver for the method to work. He was arrested in 1976 and sentenced to two months in prison.
-
They should have very serious consequences for hackers. I'm tired of defaced websites, viruses, trojans, etc. Although it is fun to screw around with other people's computers..especially if they've done it to you...but either way there should be some huge penalties for hacking. I say chop off a thumb on the first offence. 2nd offence: chope off the rest of the fingers on that hand. Hackers along with script kiddies would cease to exist.Reply
-
itadakimasu sounds like you have been the victim of malware and virii while doing some questionable internet browsing...Reply -
Well, 'Anonymous', I hope you're using Tor to browse the 'intarweb', you worthless plebian.Reply
Here in the USA, we aren't barbarians, and the only people who would even deserve such harsh treatment would be rapists and their ilk. Even so, we just lock em up and release them on probation a few months/years later. :P
Not perfect, but I say cutting off fingers because you're too stupid to take basic steps to protect your system? Kinda harsh.
The difference between a robber and a hacker, is that you can completely stop a hacker by unplugging your phone line from your modem.
Do that, for the sake of humanity. :P -
arkadi Well it is important info, but i don't think you can call them the best :) they got basted after all. Governments got best hackers if you ask me.Reply -
Reynod There are numerous other well documented hacks that probably deserved a mention.Reply
At least you did take the moral high ground.
You neglected to mention Electron and Phoenix ... clearly they were better than most of these mentioned here.
-
deadliest hmmm so this hacker list is not complete oh oh oh , you should have guys, it was most interesting reading about this. But i think hackers are a necessary evil without them how would i play my pirated games :DReply -
@ ArkadiReply
"Well it is important info, but i don't think you can call them the best :) they got basted after all. Governments got best hackers if you ask me. "
Lol, where do you think the Government found there hackers? They hired guys like this ^^Rofl