The Fifteen Greatest Hacking Exploits
Blue Box, Phreaking For The Masses
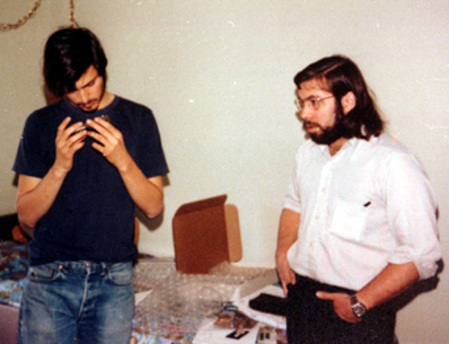
Before his arrest, John Draper had a lot of the time to tell his friends about his discovery, and one of them was a personality who is well known in the computer world today, Steve Wozniak. The co-founder of Apple, along with his good friend at the time, Steve Jobs, perfected John Draper's technique and created the Blue Box, a device capable of producing tones at the frequencies needed to fool the telephone system.
Boxes to Call for Free... in the 70s!
The two Steves successfully used their Blue Box to make all sorts of calls, and decided to start selling them. The box's ease of use and small price tag quickly made it a popular object among a group of phreaking enthusiasts.
Jobs" and Wozniak's Blue Box
The Blue Boxes were more sophisticated than the simple whistles used by John Draper. They were capable of mimicking all of the tone frequencies used by operators. The most famous story involving the Blue Box tells how Wozniak used it to telephone the Vatican posing as Henry Kissinger. Allegedly, he wanted to speak to the Pope to confess.
Get Tom's Hardware's best news and in-depth reviews, straight to your inbox.
Current page: Blue Box, Phreaking For The Masses
Prev Page Phreaking, The First Movement Next Page Hijacking Lines: Mitnick At Work-
They should have very serious consequences for hackers. I'm tired of defaced websites, viruses, trojans, etc. Although it is fun to screw around with other people's computers..especially if they've done it to you...but either way there should be some huge penalties for hacking. I say chop off a thumb on the first offence. 2nd offence: chope off the rest of the fingers on that hand. Hackers along with script kiddies would cease to exist.Reply
-
itadakimasu sounds like you have been the victim of malware and virii while doing some questionable internet browsing...Reply -
Well, 'Anonymous', I hope you're using Tor to browse the 'intarweb', you worthless plebian.Reply
Here in the USA, we aren't barbarians, and the only people who would even deserve such harsh treatment would be rapists and their ilk. Even so, we just lock em up and release them on probation a few months/years later. :P
Not perfect, but I say cutting off fingers because you're too stupid to take basic steps to protect your system? Kinda harsh.
The difference between a robber and a hacker, is that you can completely stop a hacker by unplugging your phone line from your modem.
Do that, for the sake of humanity. :P -
arkadi Well it is important info, but i don't think you can call them the best :) they got basted after all. Governments got best hackers if you ask me.Reply -
Reynod There are numerous other well documented hacks that probably deserved a mention.Reply
At least you did take the moral high ground.
You neglected to mention Electron and Phoenix ... clearly they were better than most of these mentioned here.
-
deadliest hmmm so this hacker list is not complete oh oh oh , you should have guys, it was most interesting reading about this. But i think hackers are a necessary evil without them how would i play my pirated games :DReply -
@ ArkadiReply
"Well it is important info, but i don't think you can call them the best :) they got basted after all. Governments got best hackers if you ask me. "
Lol, where do you think the Government found there hackers? They hired guys like this ^^Rofl