The Fifteen Greatest Hacking Exploits
The Appearance Of Scrambled Communications
In 1987, Kevin Mitnick left his illegal activities behind. He was under probation following his last sentence, so he could not afford any transgressions. However, he would soon use his skills again for shady activities.
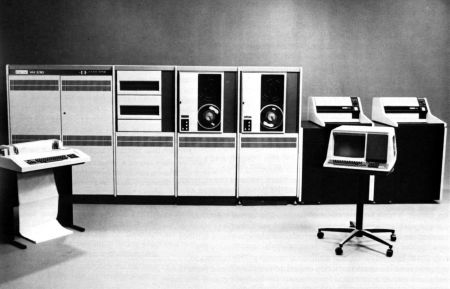
One evening, along with his fiend Lenny DiCicco, Mitnick gained access to the internal network of the research laboratory at Digital Equipment Corporation (DEC). This intrusion was not complicated for Mitnick, because DiCicco was an employee of the laboratory in question and served as an accomplice. EasyNet, DEC's internal network, did not withstand the hacker's attacks for long, and he quickly gained access to the whole system.
An Attack Carried Out with an Accomplice
As in his previous attacks, the intrusion was quickly discovered, but this time Mitnick had anticipated it. He scrambled the origin of the calls, rendering all attempts to trace him useless. And this time he was not infiltrating the network because of simple curiosity or as a challenge: he had a definite goal. He wanted to seize the source code of the VMS operating system, used by DEC on its VAX computers.
Our hacker had taken all precautions, but neglected one: his own friend. Mitnick loves games and practical jokes, so one day he called Lenny DiCicco's employer posing as a government agent. He said an employee (DiCicco) was in trouble with the IRS. This joke was not appreciated by DiCicco, who decided to get revenge in his own way.
DiCicco's Betrayal
DiCicco betrayed Mitnick, informing his employer about the latter's activities in the company network. He then contacted the FBI, telling them he could deliver the hacker that was regularly infiltrating the laboratory network. It was during a rendezvous that Mitnick fell for the trap set up by his friend, who was accompanied by two FBI agents for the arrest.
Get Tom's Hardware's best news and in-depth reviews, straight to your inbox.
The case proceeded quickly, with DEC accusing the hacker of data theft and having cost the company upwards of $200,000 in security measures. He was sentenced to a year in prison, and had to enter a six-month program to treat his computer dependency.
Current page: The Appearance Of Scrambled Communications
Prev Page Kevin Mitnick Enters The Pentagon Next Page The Creation Of The First Worm-
They should have very serious consequences for hackers. I'm tired of defaced websites, viruses, trojans, etc. Although it is fun to screw around with other people's computers..especially if they've done it to you...but either way there should be some huge penalties for hacking. I say chop off a thumb on the first offence. 2nd offence: chope off the rest of the fingers on that hand. Hackers along with script kiddies would cease to exist.Reply
-
itadakimasu sounds like you have been the victim of malware and virii while doing some questionable internet browsing...Reply -
Well, 'Anonymous', I hope you're using Tor to browse the 'intarweb', you worthless plebian.Reply
Here in the USA, we aren't barbarians, and the only people who would even deserve such harsh treatment would be rapists and their ilk. Even so, we just lock em up and release them on probation a few months/years later. :P
Not perfect, but I say cutting off fingers because you're too stupid to take basic steps to protect your system? Kinda harsh.
The difference between a robber and a hacker, is that you can completely stop a hacker by unplugging your phone line from your modem.
Do that, for the sake of humanity. :P -
arkadi Well it is important info, but i don't think you can call them the best :) they got basted after all. Governments got best hackers if you ask me.Reply -
Reynod There are numerous other well documented hacks that probably deserved a mention.Reply
At least you did take the moral high ground.
You neglected to mention Electron and Phoenix ... clearly they were better than most of these mentioned here.
-
deadliest hmmm so this hacker list is not complete oh oh oh , you should have guys, it was most interesting reading about this. But i think hackers are a necessary evil without them how would i play my pirated games :DReply -
@ ArkadiReply
"Well it is important info, but i don't think you can call them the best :) they got basted after all. Governments got best hackers if you ask me. "
Lol, where do you think the Government found there hackers? They hired guys like this ^^Rofl