Intel Core i5-661: Clarkdale Rings The Death Knell Of Core 2
Accelerating Encryption: AES-NI
If you’re an average desktop user, encryption probably isn’t very important to you today. After all, password-protecting everything just creates one extra layer of complexity when you want to actually use your machine, right? But for those with something to hide (and I think that includes all of us to some degree, thank you very much Eric Schmidt), there’s value in being able to protect that information.
All of Intel’s 32nm Westmere-based processors, starting with the dual-core Clarkdale desktop CPUs, include six new SIMD instructions that Intel calls AES-NI (Advanced Encryption Standard New Instructions), which are designed to help consolidate the mathematical operations used in the block cipher algorithm. In conjunction with applications optimized for AES-NI, the new instructions help maintain the security of AES by protecting against side-channel attacks, while alleviating the performance overhead of encrypting and decrypting in software.
Intel sees five different areas where its AES instructions apply: whole disk encryption (via apps like BitLocker, PGP, and TruCrypt), file storage encryption (7-Zip and WinZip are two favorites), conditional access of HD content (pay-to-play; yuck), Internet security, and VoIP communications. We have coverage upcoming putting AES-NI to the test with whole disk encryption, but wanted to at least run the new instructions through their paces in file storage encryption—something we all use in one form or another.
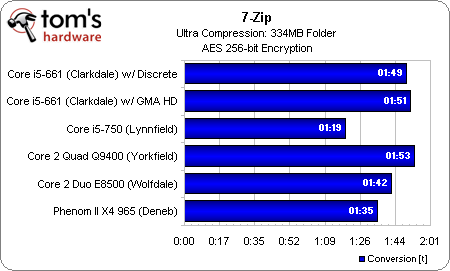
Our first round of tests pit the dual-core Core i5-661 against a number of quad-core models, along with Intel’s Core 2 Duo E8500, in the 9.10 beta of 7-Zip, which is optimized for AES-NI. Surprisingly, the Core 2 Duo actually finished our 334MB Ultra compression routine in less time than the Clarkdale chip.
Of course, we didn’t really have any reference point to compare against, so it was hard to say whether the performance delta was caused by the Core 2 architecture or some shortcoming inherent to Westmere. We nevertheless approached Intel with our findings, and the company let us know that 7-Zip’s compress/decompress algorithm operates in such a way as to cover up any benefit that’d otherwise be realized by AES-NI.
Such a "heavy" algorithm doesn’t help us much here, so we swapped to WinZip 14. Although we recently removed WinZip from our benchmark suite due to its single-threaded nature (and thus, generally slower performance than apps like WinRAR), this is another title optimized for AES-NI.
| WinZip 14 | Processor Family | Compress 334MB | Decompress 334MB |
|---|---|---|---|
| 256-bit AES | Clarkdale (i5-661) | 2:17 | :09 |
| Lynnfield (i5-750) | 2:01 | :16 | |
| No Encryption | Clarkdale (i5-661) | 2:12 | :09 |
| Lynnfield (i5-750) | 1:52 | :10 |
Without the use of encryption, both our Lynnfield- and Clarkdale- CPUs are on even footing and we’re able to assess each CPU’s base performance in WinZip 14. The Core i5-750 is clearly faster in our compression test, finishing 20 seconds before the Core i5-661. However, Turbo Boost kicks in on the decompression, and the Clarkdale chip finishes the task a second quicker.
Get Tom's Hardware's best news and in-depth reviews, straight to your inbox.
Enabling 256-bit AES tells the story we’re looking for, though. The gap in compression narrows to 16 seconds. And while the Lynnfield chip, which lacks AES-NI, incurs a six second penalty attributable to encryption, the Clarkdale processor suffers no such slow-down.
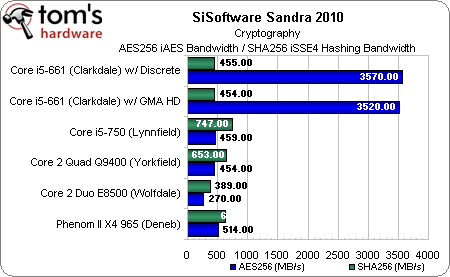
With all of that said, it's easy to fire up SiSoftware's Sandra 2010, run the Cryptography test, and witness the massive jump in iAES bandwidth attributable to Intel's new instructions. As you can see, the NSA's SHA-2 hash functions aren't accelerated, and consequently don't enjoy the speed-up seen by AES.
At least for now, the benefits of AES-NI are subtle at best. But, as is the case with any hardware capability reliant on software support, this will likely become a feature that has more of an impact as time goes on—and especially as Intel prepares to launch its Nehalem-EX processors in a couple of months. The tenets of security and encryption are most deeply rooted in the enterprise space, after all.
Current page: Accelerating Encryption: AES-NI
Prev Page Clarkdale: Engineering Smarts Behind Marketing’s Mess Next Page Intel HD Graphics: Clarkdale’s On-Package GPU-
Zoonie Well... I think that takes care of the dreaded "But can it play Crysis?" question regarding its GMA :D :P :PReply -
eklipz330 can i ask why you teased us at the end with the 4.5ghz OC but didn't include them in the benchmarks? =Reply -
cangelini xc0mmiexVideo on page 1 not working ... "This is a private video..."Reply
Fixed! Had to keep it private pre-launch :) -
I really like the improvements Larrabee brought about....not! I do like the fact they are making progress but they really need to skip ahead a few generations or buy out some other company to design a GPU for themselves.Reply
-
gkay09 ^ Many more reasons to buy AMD Phenoms II X4 in the mid-range segment...Reply
Only drawback with the AMD CPUs is the power consumption, that I feel can be brought down with slight undervolting... -
dtemple I'm looking to upgrade from my Athlon X2 @ 2.7GHz because I do more with the computer now than I did before - sometimes I'll play a game while my TV tuner is recording from my cable signal, and having more cores would help these multiple tasks run more smoothly.Reply
I was waiting until the Clarkdale-based i5 launched, thinking it would be a quad-core that was more competitively priced against the Phenom II X4, but it looks like a Phenom II X4 is my only option to get more cores for less money.
The only good news coming out of this launch is that LGA1156 is not changing for the Clarkdale chips, so it looks to be the most future-proof platform to upgrade to, if one was so inclined. I'm personally going with a Phenom II since I can get one without changing motherboards. This is one of the more disappointing launches in the last year or so. -
cangelini eklipz330can i ask why you teased us at the end with the 4.5ghz OC but didn't include them in the benchmarks? =Reply
We have another overclocking piece planned--I wanted to get a Core i3, at least, to include :) -
I would love to see what GTA IV would do do the dual cores in gaming! I do know that its a bear of a game on the CPU and it would truly show off if hyperthreading could actually make a major difference.Reply
-
maximus20895 Great video once again! Thanks for this and the review itself. Very informative. I really liked the graph on the first page too :)Reply