Breaking Down The New Security Flaws In AMD's Ryzen, EPYC Chips
Get Tom's Hardware's best news and in-depth reviews, straight to your inbox.
You are now subscribed
Your newsletter sign-up was successful
Update, 3/13/18, 11:10pm PT: We have our original coverage of this vulnerability, and the suspicious circumstances surrounding the release of the information, in our original Report Claims AMD Ryzen, EPYC CPUs Contain 13 Security Flaws (Update) article. This companion article serves as a primer for the individual alleged vulnerabilities.
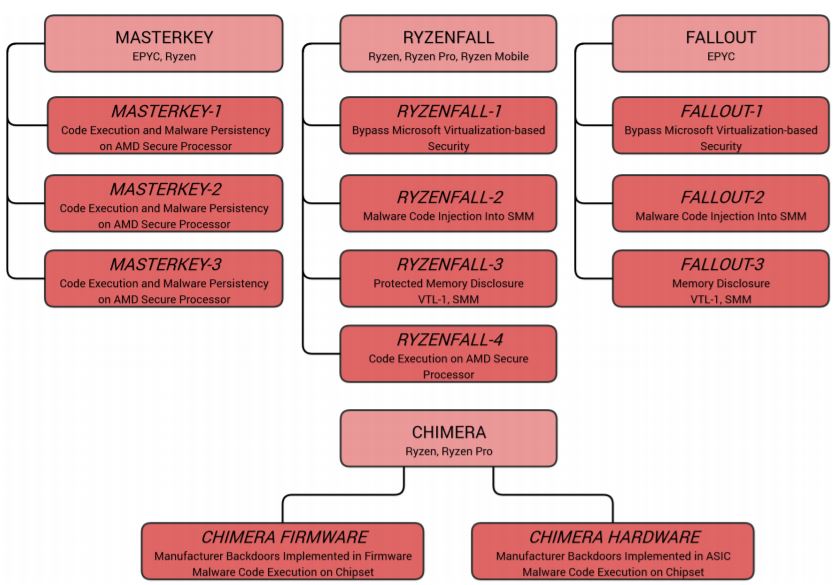
CTS-Labs, a new "research organization" from Israel that seems to have formed last year, claimed to have discovered four categories of bugs affecting AMD’s Ryzen processors, called Masterkey, Ryzenfall, Fallout, and Chimera. (This is a developing story, and we've reached out to both CTS Labs and AMD about these reported vulnerabilities. We'll share more information as we receive it.)
AMD PSP
AMD started incorporating the Platform Security Processor (PSP) into its chips back in 2013 as a “trusted execution environment,” somewhat similar to Intel’s much criticized Management Engine (ME).
Article continues belowIn theory, the chip is there to create a secure environment that’s isolated from operating system malware. However, critics have said that, just like Intel’s ME, it could be used as a backdoor without the user knowing any better. If the PSP somehow became malicious, it could bypass any OS protection because it exists at a lower level underneath the OS.
Last year, AMD customers and privacy activists created a petition pleading to AMD to release the source code to its PSP. However, AMD said that it has no plans (minute 35) to open-source its PSP firmware anytime soon.
The company also added that it has already completed multiple audits performed by other third-party security companies that AMD hired to check the PSP for vulnerabilities, and that some of its enterprise customers are doing their own audits of the co-processor.
A PSP security flaw was disclosed in the beginning of this year, but everyone’s attention quickly moved to Meltdown and Spectre after that.
Get Tom's Hardware's best news and in-depth reviews, straight to your inbox.
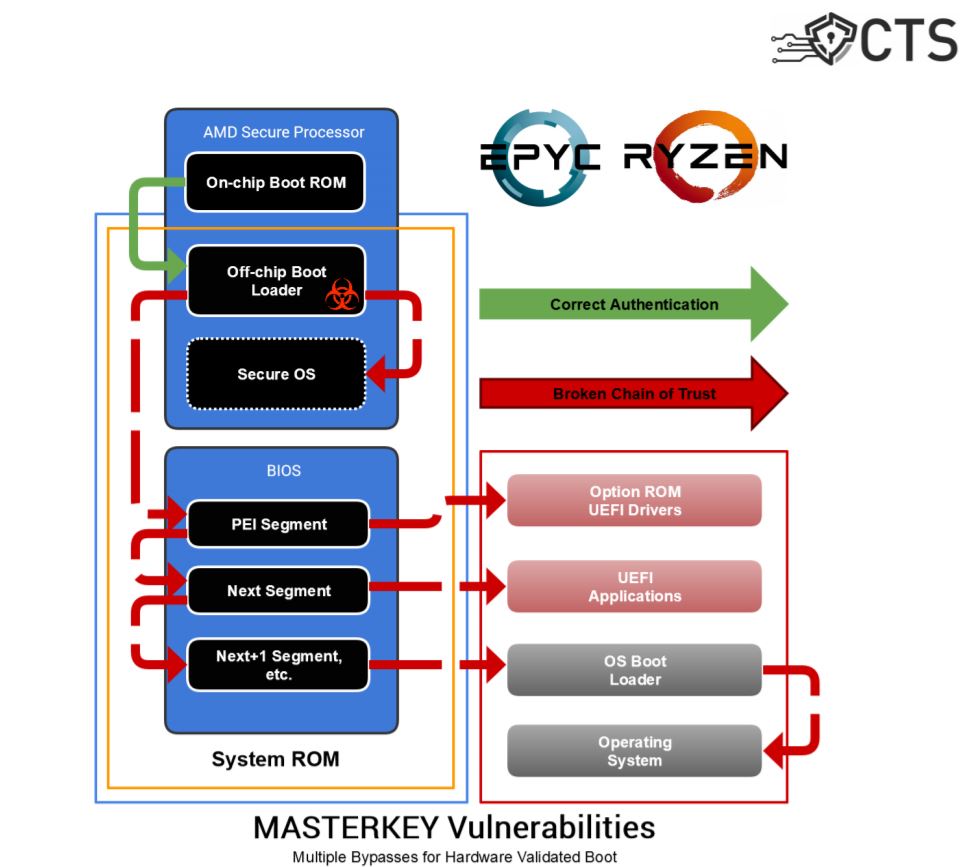
Masterkey Vulnerabilities
CTS said that the Masterkey class of vulnerabilities allows attackers to bypass AMD's Hardware Validated Boot feature and exploit the PSP co-processor that comes with AMD’s Ryzen and EPYC chip line-ups. Ryzen Pro and Ryzen Mobile chips may also be affected, but the researchers didn't test those chips.
The flaws supposedly enable code execution and malware persistence on AMD’s PSP that would run in kernel-mode with the highest permissions and stay hidden from virtually all security solutions on the market.
According to CTS-Labs' report, the Masterkey flaws also allow tampering with AMD’s firmware-based security features such as Secure Encrypted Virtualization (SEV) and Firmware Trusted Platform Module (fTPM). The Windows Credential Guard protection could also be bypassed, allowing for credential theft. Attackers could even use the Masterkey flaws to install ransomware or brick the hardware.
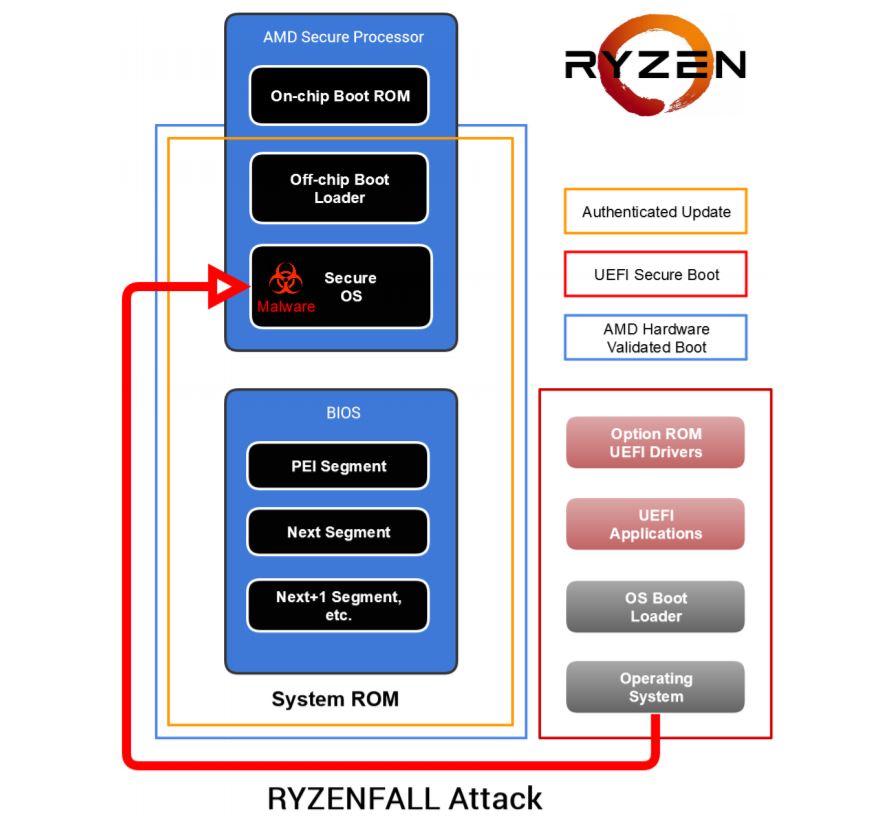
Ryzenfall Design And Implementation Flaws
The Ryzenfall bugs represent a set of design and implementation flaws in AMD's "Secure OS" that runs on the PSP. CTS-Labs said that these flaws allows attackers to take full control of the PSP in the Ryzen, Ryzen Pro, and Ryzen Mobile processors. The PSP could be leveraged to read and write protected memory areas, such as SMRAM, and the Windows Credential Guard isolated memory.
The attackers could steal network credentials using these flaws and then they could gain access even to highly secure corporate networks, according to the CTS researchers. The malicious actors could use Ryzenfall in conjunction with Masterkey to install persistent malware for long-term espionage purposes.
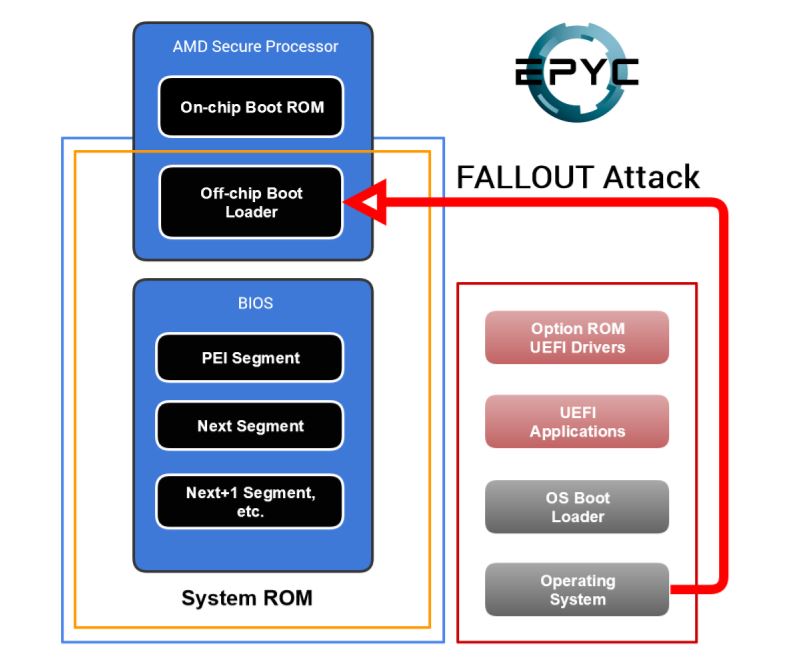
Fallout Design Flaws
The Fallout set of vulnerabilities resides in the boot loader component of EPYC’s PSP processor. The boot loader is responsible for the Hardware Validated Boot on the EPYC server chips, as well as launching the PSP module for Secure Encrypted Virtualization, a new security feature of the EPYC chips.
The flaws could allow attackers to read from and write to protected memory such as System Management RAM (SMRAM) and Windows Credential Guard isolated memory (VTL-1). Attackers could also bypass BIOS flashing protections that are implemented in the System Management Mode (SMM), used for low-level hardware control.
Chimera Backdoors
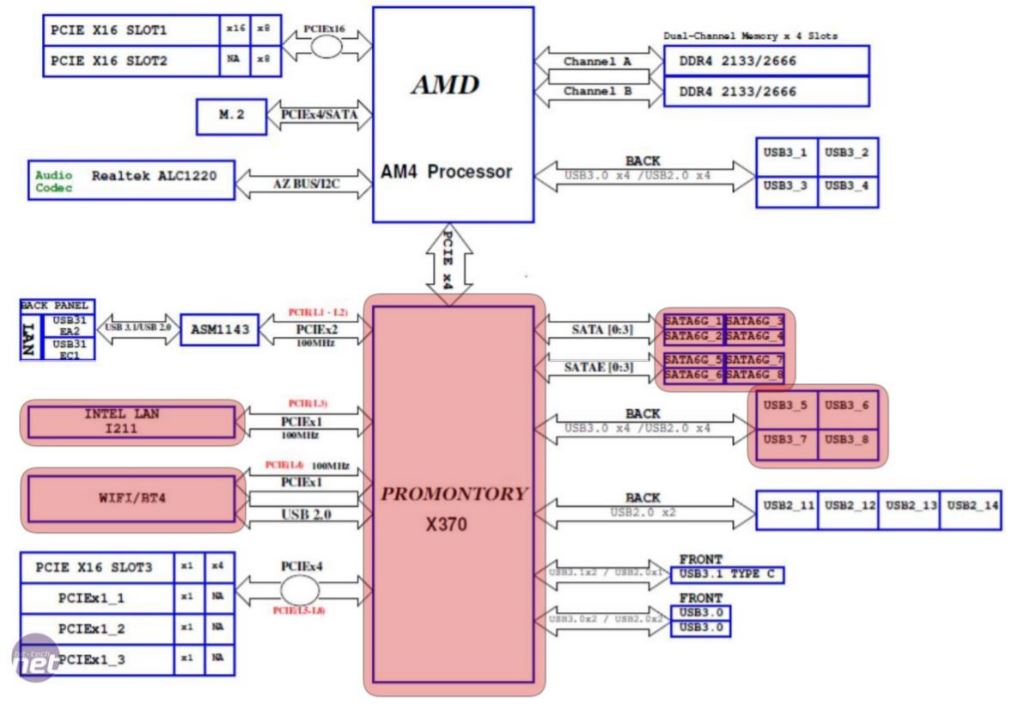
Perhaps the worst of the bugs may not even be regular software vulnerabilities or design flaws, but actual firmware and hardware backdoors, found in ASMedia’s chipsets, which AMD’s Ryzen uses under AMD's own "Promontory” brand name. Asus is the parent organization behind ASMedia.
The Chimera manufacturer backdoors allow attackers to inject malicious code into the Ryzen chipset. The chipset connects the CPU to USB, SATA, and PCIe devices. An attacker could potentially leverage the middleman position of the chipset to launch an attack on the CPU.
CTS said that chipset-based malware would be able to evade any endpoint anti-malware solutions on the market. The malware running on the chipset could leverage the Direct Memory Access (DMA) engine to attack the operating system. The researchers don’t believe that AMD could mitigate these backdoors, considering one of them is hardware-based, without a recall of the chips.
CTS-Labs hasn’t given too many details about how the flaws work, as a precaution so that malicious actors don’t start exploiting them before AMD has a chance to fix these flaws. At the same time, the company only gave AMD 24 hours notice before publishing its materials.
The security researchers said they don’t know if any of the vulnerabilities are already being exploited in the wild, but they are concerned about the Chimera firmware and hardware backdoors found in the ASMedia chipsets. They conclude the report saying that the existence of these major flaws in AMD’s processors is due to AMD’s disregard for fundamental security principles.
Lucian Armasu is a Contributing Writer for Tom's Hardware US. He covers software news and the issues surrounding privacy and security.
-
Clamyboy74 Making articles on a flaw that has little to no credibilty... wowReply
Also: "AMD’s disregard for fundamental security principles." @Intel meltdown??? -
Clamyboy74 Oh, and digging more onto their web page and youtube, especially youtube:Reply
https://i.imgur.com/OkWlIxA.jpg -
Willyfisch Actual news story:Reply
CTS partnered with Viceroy to make some whitepapers to short AMD. -
Giroro Who paid CTS-Labs to write this report?Reply
I don't think the report is even worth acknowledging until they either prove how they are funded, or until the flaws are validated by a 3rd party.
They clearly weren't trying to claim any kind of bug bounty, as they went public without giving AMD a chance to fix it. -
Willyfisch Reply20790349 said:Who paid CTS-Labs to write this report?
I don't think the report is even worth acknowledging until they either prove how they are funded, or until the flaws are validated by a 3rd party.
They clearly weren't trying to claim any kind of bug bounty, as they went public without giving AMD a chance to fix it.
Viceroy Research. They are a very shady short seller company (I don't even know who's behind them, might be just 1 person).
Look at their other shorts, like the -75% on Pro Sieben.
They are suggesting AMD's fair value to be at $0 in their very professionally made research paper (irony).
https://viceroyresearch.files.wordpress.com/2018/03/amd-the-obituary-13-mar-2018.pdf -
akamateau What is amazing is how every online media outlet is reporting on a piece from ONE source that has been in business for 7 months. The research company started up just before the Spectre and Meltdown flaws were released and now we have 13 AMD ONLY flaws and no mention at all about ANY possible Intel or ARM exploits either.Reply
Tom's Hardware has ZERO Journalistic Integrity.
https://imgur.com/OkWlIxA
I am ABSOLUTELY CERTAIN this entire piece is Securities Fraud and Tom's Hardware is a very willing participant. TH did not vet the source nor did they CHECK ANY FACTS. -
HEXiT Somehow I doubt this is fake news as some are suggesting here, as AMD would wring them out to their last cent if this report were a fabrication;Reply
as it will affect their share price, their reputation and consumer confidence in their products.