FireEye Warns Of Weak Fingerprint Authentication Systems On Mobile Devices
According to a team of researchers from security company FireEye (Yulong Zhang, Zhaofeng Chen, Hui Xue and Tao Wei), HTC has been leaving users' fingerprints "world-readable" in plaintext, which means any skilled attacker could've stolen them and used them for malicious purposes. The company also uncovered other dangerous vulnerabilities that affect many other fingerprint authentication systems.
Unsecure Fingerprint Data Storage
Fingerprints make authentication radically easier than passwords, which is why so many smartphone OEMs have been in a hurry to adopt fingerprint readers into their phones. However, some don't seem to have put too much effort into making sure the fingerprint is as secure as it can be, to the point where even if the device gets hacked, the fingerprint can't be stolen and re-used by the attackers.
According to the FireEye researchers, the tested HTC One Max device kept the fingerprint data in a plaintext "dbgraw.bmp" image file inside the "word readable" /data/ folder. The team claimed that any unprivileged app could steal the users' fingerprints by reading that file.
Although it wasn't quite this bad, the Galaxy S5 was also found vulnerable to a "fingerprint sensor spying" attack. However, in this case, the attacker would need the device in his possession, and then he could root and install a custom ROM on it that could take advantage of this vulnerability in order to steal the fingerprint data.
HTC was found to be vulnerable to the same attack. Both companies were notified by FireEye, and the company believes more Android OEMs could be vulnerable to the same type of attack due to the type of authentication frameworks they are using.
Confused Authorization Attack
The researchers uncovered a few other potential issues with fingerprint authentication on Android. One of them is called the "confused authorization attack," where the user is tricked by another malware-infected app to give it the fingerprint data. For instance, the user could see a fake lockscreen on the phone that requires a fingerprint scan to unlock the phone, which can then steal that fingerprint data.
Backdoor Of Pre-embedding Fingerprints
Another potential problem is the risk of pre-installed backdoors in units before they are sold to consumers. This could either happen as a matter of government policy in originating countries where the devices are made, or they could be intercepted by the local intelligence agencies as they get imported into the country or shipped to certain users.
Get Tom's Hardware's best news and in-depth reviews, straight to your inbox.
The main problem here is that an attacker could embed prefabricated fingerprints into the device without the user knowing about it. The device could show N number of stored fingerprints but in fact have more than N. Those extra fingerprints can then be used to bypass the user authentication with the fake fingerprints.
Solution: More Isolation From User Space
Most of these issues come from the fact that either TrustZone isn't used at all (as in HTC's case), or it's not used as it should be to completely isolate the fingerprint data as well as the fingerprint UI inside TrustZone's "secure world." TrustZone comes with most ARM chips these days, so it's mainly a matter of OEMs or fingerprint system vendors deciding to take advantage of it in a proper way.
FireEye also recommended that vendors of fingerprint authentication systems improve the security design of the authentication framework and allow professional security auditors to vet the systems before they are commercialized.
The company also suggested that mobile users should only buy devices from OEMs that provide timely patches and upgrades to the latest version of Android, should only install apps from reliable sources, and should not root their devices, as that exposes them to too many risks.
Android M Could Boost Fingerprint Security
Google recently announced that Android M will come with its own mechanism for dealing with fingerprint authentication, and knowing that Google is usually rather proficient at security, it should be a good one. That should standardize a strong fingerprint authentication framework across all Android devices in the future (when they get to Android M), unless some OEMs continue to use custom solutions.
Follow us @tomshardware, on Facebook and on Google+.
Lucian Armasu is a Contributing Writer for Tom's Hardware US. He covers software news and the issues surrounding privacy and security.
-
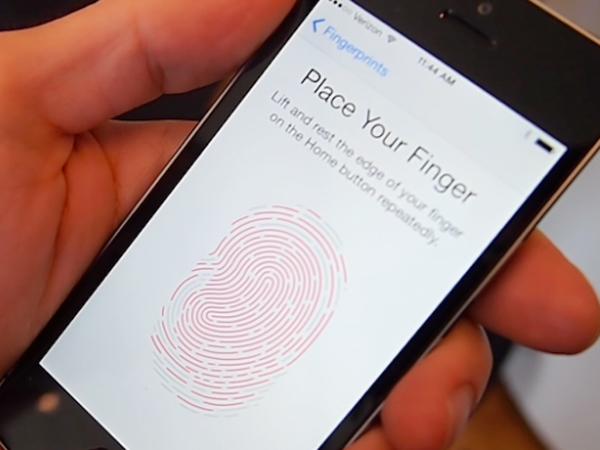
dark_knight33 So, if the article is about an HTC device, and mentions a Samsung device, but the words Apple & iPhone don't appear anywhere in the article, why is the picture of an iPhone 5?Reply
Couldn't find an HTC sample?
http://cdn1.tnwcdn.com/wp-content/blogs.dir/1/files/2013/10/One_max_fingerprint.jpg