Intel and AMD Hertzbleed CPU Vulnerability Uses Boost Speed to Steal Crypto Keys
Boost frequencies reveal timings, and thus secret keys
Intel and researchers from UT Austin, UIUC, and UW published papers today outlining the 'Hertzbleed' chip vulnerability that allows side-channel attacks that can steal secret AES cryptographic keys by observing the CPU's boost frequency/power mechanisms. According to external researchers, both Intel and AMD CPUs are impacted, but AMD hasn't issued an advisory yet. The vulnerability doesn't impact all cryptographic code, but some mitigation techniques for impacted systems come with as-yet-undefined performance penalties. Intel says it had found this vulnerability via internal security investigations, but external research teams later disclosed their findings to the company. Today's coordinated disclosure brings the issue into the public eye, but it is likely that CPUs from other vendors are also impacted.
Like all side-channel attacks, a Hertzbleed-based attack steals data by observing or exploiting a secondary effect of an operation on a system. In this case, by observing the power signature of any given cryptographic workload. As with most workloads, the power signature of a cryptographic workload varies due to the CPU's dynamic boost clock frequency adjustments during the workload. An attacker can convert that power information to timing data, allowing them to steal cryptographic keys. Cryptographic implementations that are already hardened against power side-channel attacks aren't susceptible to the Hertzbleed vulnerability.
The vulnerability impacts all Intel processors and AMD Zen 2 and Zen 3, but it isn't clear if it will impact the upcoming Zen 4 Ryzen 7000.
Hertzbleed can be exploited remotely — it doesn't require physical access. It has only been proven on Intel and AMD silicon. However, it should theoretically apply to almost all modern CPUs because it works by observing the power algorithms behind the Dynamic Voltage Frequency Scaling (DVFS) technique, a staple of modern processors. As such, this isn't a microarchitecture-specific attack — any processor with dynamic power and thermal management is potentially impacted. Intel says this has prompted it to share its findings with other chipmakers so they can assess any potential impact.
Intel says that it doesn't think this attack is practical outside of a lab environment, partially because it takes "hours to days" to steal a cryptographic key. Additionally, an exploit based on this attack would require sophisticated high-resolution power monitoring capabilities.
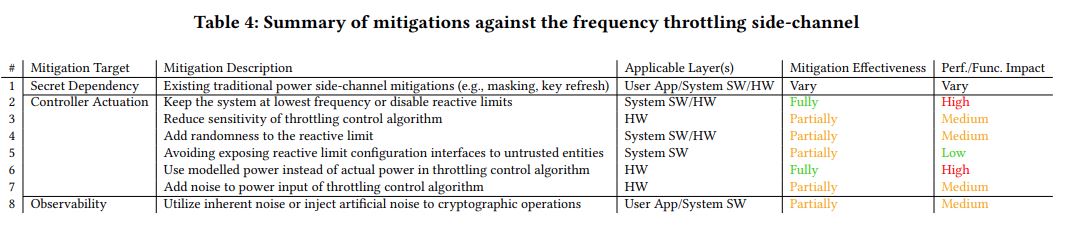
Intel's mitigation includes software fixes for any code that is susceptible to enabling a power side-channel attack — the company is not deploying firmware fixes. AMD is also not issuing a microcode patch. However, as you can see in the table above, some of the mitigation techniques do have a 'high' impact on performance. This varies by technique and whether or not it can be accomplished in hardware or software, or a combination of both.
In some cases, the attack can be thwarted by disabling Turbo Boost (Intel) or Precision Boost (AMD) entirely, but that has a tremendous performance impact. However, this doesn't protect against all attacks. We're working on getting a more precise definition of any performance impacts for the other techniques. Hertzbleed has been assigned the Intel-SA-00698 ID and CVE-2022-24436 ID for Intel, and CVE-2022-23823 for AMD.
We're boiling down the Hertzbleed vulnerability to the essence of how it works, there are many more details to be found in both the original papers and Intel's guidance on the matter — head here for a deeper description.
The Hertzbleed report comes amid a broader Intel release today that includes three security advisories that cover six vulnerabilities, all of which intel found through its own internal research. Intel has revamped its internal security investigation apparatus in the wake of the Spectre and Meltdown vulnerabilities, bolstering its efforts to find vulnerabilities in its own chips before the security weaknesses are discovered in the wild.
Today's advisory includes the MMIO Stale Data Advisory vulnerability that's listed as Intel-SA-00615. This vulnerability requires both firmware and operating system/hypervisor updates to fully rectify the hardware vulnerability. Intel has published a brief overview and a technical deep dive. Finally, the MMIO Undefined Access Advisory covers a hypervisor vulnerability (Intel-SA-00645). Intel has posted guidance for mitigating this vulnerability here.
Get Tom's Hardware's best news and in-depth reviews, straight to your inbox.

Paul Alcorn is the Editor-in-Chief for Tom's Hardware US. He also writes news and reviews on CPUs, storage, and enterprise hardware.
-
mavroxur This seems like such a niche vulnerability. It would require extreme precision current monitoring of the CPU itself at a very, very high sampling rate. I mean, if someone comes to my door with lab equipment wanting me to hook it up to my system, I'd personally be a little suspect.....Reply -
Alvar "Miles" Udell ReplyNaturally, the most direct method of stopping the attack is to disable Turbo Boost (Intel) or Precision Boost (AMD) entirely, but that has a tremendous performance impact.
Which is false. Manual overclocking has positive multicore performance improvements while carrying a minimal to zero single thread performance penalty, and I can say this from experience with the Ryzen 1800X and 3700X, both on a Crosshair VI Hero WiFi, and my current 5950X on an X570S Aorus Master. None of those CPUs ever came close to the all core boost I obtained by overclocking, and none of them ever hit their advertised boost speed under a single core load despite removed limits and liquid cooling. -
HyperMatrix ReplyAdmin said:Intel and groups of researchers divulged the 'Hertzbleed' chip vulnerability that allows stealing cryptographic keys by observing the CPU's boost frequency mechanism.
Intel and AMD Hertzbleed CPU Vulnerability Uses Boost Speed to Steal Crypto Keys : Read more
You can also avoid this without a performance loss by disabling speed shift and turbo stepping. I currently have my CPU running at max clocks without any boosting. So maintains max clocks even at idle. I didn’t do it because of this vulnerability, but rather due to overclock stability (V/F curve instability with higher clocks/manual voltage). -
JWNoctis So it's a rehash of the old timing attack.Reply
Really don't need another Heartbleed right now. -
rluker5 My 12700k's mild 24/7 oc has 4 cores that go to 5.1, 1 to 5.0, 3 to 4.9 and 4 more to 3.9. Which also varies on temp (TVB+2) and # of cores loaded.Reply
How precise does this information have to be? I imagine my derived timings would be pretty hazy. -
setx Just disabling Turbo or setting all cores to the fixed multiplier won't make it run at constant speed. Remember that you have other power-related technologies like C-states and power/thermal throttling and you definitely don't want to turn them off in a realistic system (and is it even possible on modern CPUs?)Reply -
shady28 Seriously, I think a lot of these "security researchers" publish this stuff to try to look like they're doing something useful.Reply
I mean, no kidding if someone can install software to and get direct physical access to your computer to hook up monitoring and data collection tools, they can 'hack' it.
Virtually no computer crimes are committed this way, it's almost always social engineering be that a phone call, text message, or email. -
HyperMatrix Replysetx said:Just disabling Turbo or setting all cores to the fixed multiplier won't make it run at constant speed. Remember that you have other power-related technologies like C-states and power/thermal throttling and you definitely don't want to turn them off in a realistic system (and is it even possible on modern CPUs?)
Power and thermal throttling only happens if you exceed those limits. I have my 12900k locked at 5.3GHz all core. These are 24/7 clocks. No issues whatsoever. And no drops according to cpu-z even under 320W AVX loads. -
rluker5 Reply
I bet with this vulnerability, to get it to work well enough to get results on a non idle pc, you still need admin privileges and likely physical access to get around things like UAC control. I also thought browsers already were patched with low precision timing right when stuff like this came out with meltdown and the first spectre.shady28 said:Seriously, I think a lot of these "security researchers" publish this stuff to try to look like they're doing something useful.
I mean, no kidding if someone can install software to and get direct physical access to your computer to hook up monitoring and data collection tools, they can 'hack' it.
Virtually no computer crimes are committed this way, it's almost always social engineering be that a phone call, text message, or email.
Apparently some people do want to disable c-states. They forgot to add your choice in the mitigation summary table with full mitigation effectiveness and positive performance impact :pHyperMatrix said:Power and thermal throttling only happens if you exceed those limits. I have my 12900k locked at 5.3GHz all core. These are 24/7 clocks. No issues whatsoever. And no drops according to cpu-z even under 320W AVX loads. -
setx Why people think what they do at home is relevant to the real world of server & corporate hardware? Those vulnerabilities are mainly headache for them as they have to provide the guarantees.Reply