'USB Killer 2.0' Shows That Most USB-Enabled Devices Are Vulnerable To Power Surge Attacks
Last year, a Russian hacker demonstrated a “USB Killer.” Once connected, the USB device sends high-voltage negative DC through a USB port until it fries the circuitry of the host device. The device was effective, but it never became commercially available.
USB Killer 2.0
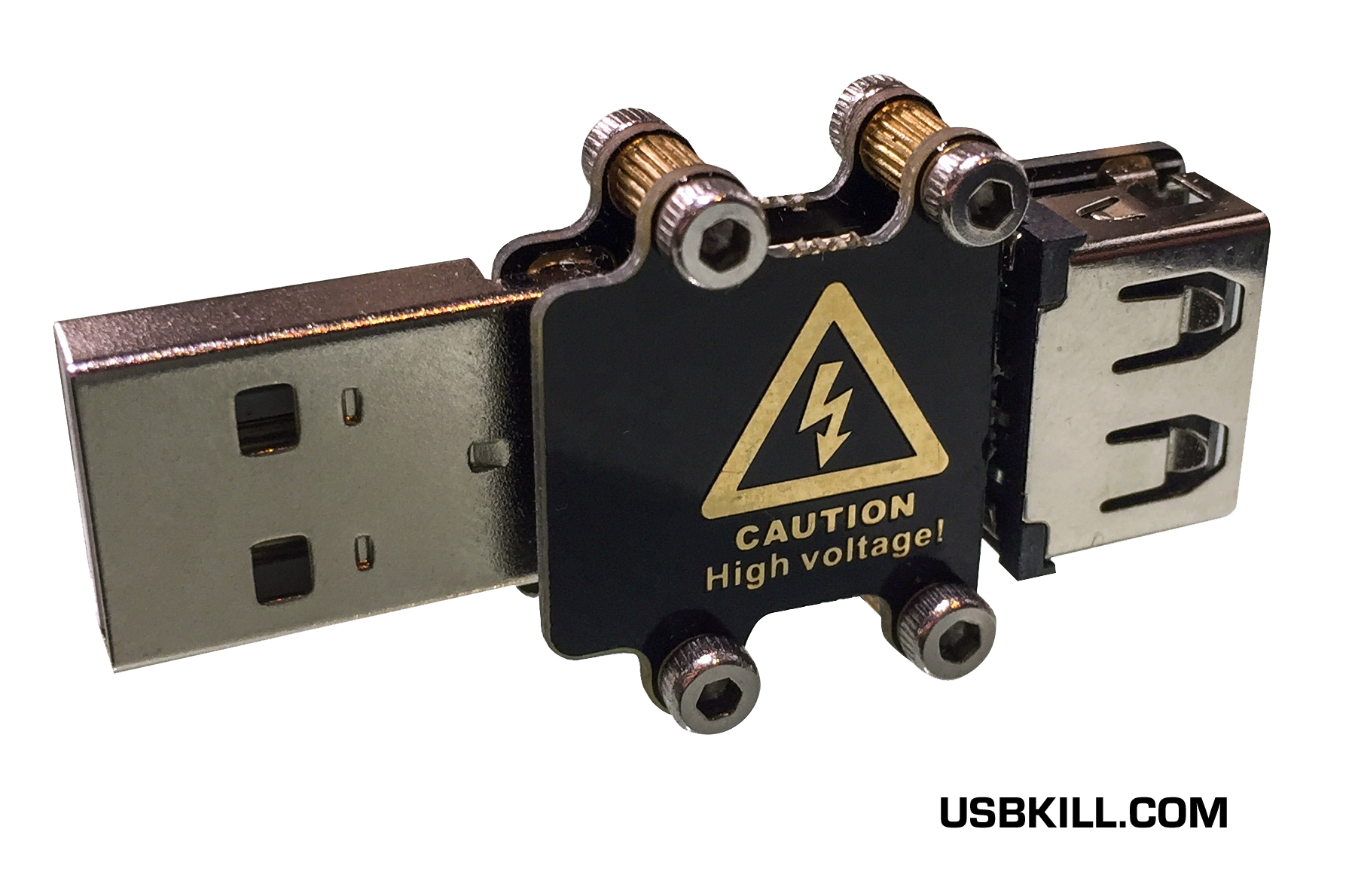
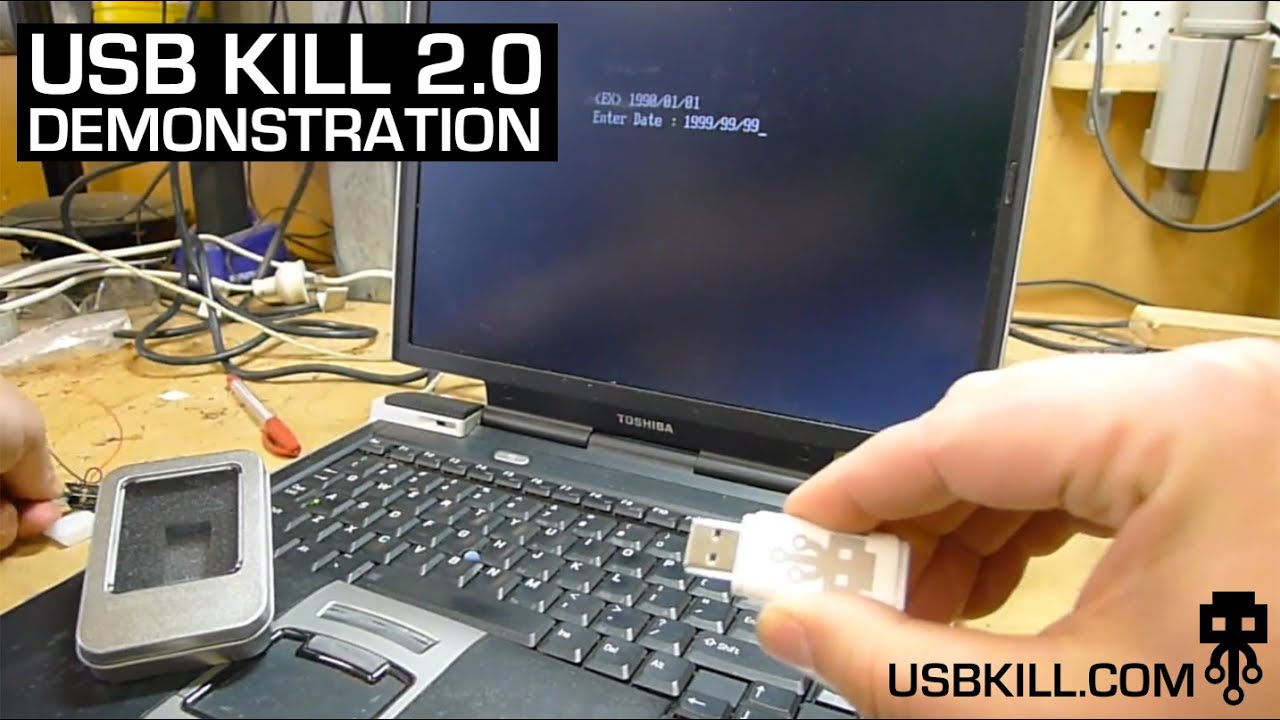
Now, a company from Hong Kong is commercializing both a similar device-frying USB stick called “USB Killer 2.0” and a “USB Killer Test Shield,” which helps to test electronic devices against this type of attack.
The company said it had built its own USB killer (version 1.0) internally about a year ago, as well. Due to popular demand, and after seeing that (with the exception of Apple) no other device maker had built-in protections against this type of attack, it decided to commercialize it.
Article continues belowThe Hong Kong company, which prefers to be referenced as USBKill.com to English speakers, also noted that other device makers had one year of warnings that such power surge attacks were possible, and that so far it has acted according to responsible disclosure best practices.
“To this day, according to our testing, the only company that releases hardware protected against a USB power-surge attack is Apple, on their Laptop and Desktop ranges. This means - despite adequate warning, and time to respond - the majority of consumer-level hardware manufacturers choose not to protect their customer's devices. We are disheartened by this lack of respect for customers,” said the Hong Kong company in a recent blog post.“As is standard in the InfoSec industry, we are releasing the USB Killer 2.0 publicly, after one year of disclosure. We hope the attention will force manufacturers to respect a customer's investment in their product, and work to resolve the issue,” added the company.
How USB Killer 2.0 Works
When plugged into a USB port, a "USB killer" device rapidly charges its capacitors from the USB power source. Then, when it’s charged, it discharges -200V DC over the data lines of the host device. The charge/discharge cycle repeats multiple times per second until you remove the device from the USB port. This technique allows the USB Killer to instantly kill any computer or electronic device that has a USB port.
Device manufacturers can buy the "USB Killer Test Shield" to test their products against this type of attack. The device mimics the output functionality of the USB Killer 2.0 device without frying the host. The USB Killer 2.0 can be purchased for $49.95 USD, while the Test Shield can be had for $13.95 USD (free shipping and 50 percent discount for the Test Shield if you buy the two together).
Get Tom's Hardware's best news and in-depth reviews, straight to your inbox.
USB Type-C Authentication
The USB Implementers Forum recently announced a new cryptographic authentication protocol for USB Type-C connectors that would stop unauthorized and uncertified devices from connecting to a computer or smartphone.
Steve Benson from USBKill.com agreed that this could solve the issue, but malicious attackers could still find vulnerabilities in the protocol to bypass it. Also, there’s a much easier solution to protect against power surge attacks:
"From my understanding, this proposal would indeed solve the problem - or at least create an additional hurdle," said Benson.“Nothing would stop a would-be attacker from duplicating a signature - and I would imagine that it would depend on the implementation. If the host device allows any type of communication via the data lines, this could be vulnerable to a power surge.The ultimate solution, and that which vendors in the enterprise field (and Apple, in the commercial field) - have implemented - is the humble opto-coupler: a plentifully available, cheap component - made exactly for this purpose,” he added.
The USB Killer attack seems reminiscent of the BadUSB exploit announced in 2014 at Black Hat. BadUSB is a firmware exploit, though, but it also left millions of computers potentially vulnerable because USB sticks don’t tend to be updated or patched against such attacks. Manufacturers could fix the USB Killer attack if they added power surge protections to their USB ports, as Benson suggested.
In the meantime, for the all of the existing computers out there that are vulnerable to USB Killer attacks, Benson suggested that users take these steps to protect themselves:
- Don't trust unknown hardware
- Use a USB condom (example)
- Physically cap USB ports, similar to covering webcams
Lucian Armasu is a Contributing Writer for Tom's Hardware US. He covers software news and the issues surrounding privacy and security.
-
ryguybuddy Wow! This might be a espionage tool someday....but I doubt it. Its more about cyber-attacks these days. Still cool though!Reply -
InvalidError Reply
You aren't going to be much 'espionage' by frying USB ports and computer chipsets.18574229 said:Wow! This might be a espionage tool someday....
Using photo-couplers to prevent surges from destroying electric transceiver and chipsets at the end of the data line could prove difficult on USB3.x and other high-speed interfaces that require much faster and more expensive devices. While putting photo-isolators everywhere may prevent the attacker from casually frying the PC, that won't stop him from frying every isolator on your PC and still rendering your PC unusable unless your motherboard has user-replaceable isolators.
The simplest and most foolproof way to completely eliminate voltage injection issues would be to have an optical USB and PCIe spec for external devices.
The same "attack" would most likely work through most other external electrical connections as well. Even those with ESD protection networks will still fail if the "attack" provides enough current to blow the protections out. -
turkey3_scratch So, if someone has to physically put this USB into the computer to fry it, just don't let that person do it. People who do malicious stuff like this like to do it over the Internet, but in person, they will fail to decimate the machine.Reply -
razor512 The goal is, you build one and place it in a normal looking USB flash drive enclosure, and then you leave it in a location where flash drives are commonly stolen.Reply -
turkey3_scratch Reply18574389 said:The goal is, you build one and place it in a normal looking USB flash drive enclosure, and then you leave it in a location where flash drives are commonly stolen.
Well, people shouldn't steal. So in a way it's almost like their punishment. -
InvalidError Reply
You find a USB drive lying on the ground or anywhere else where you are unlikely to find the owner and pick it up. Is that stealing? You end up with a dead computer or other gadget either way.18574410 said:Well, people shouldn't steal. So in a way it's almost like their punishment.
-
turkey3_scratch Reply18574568 said:
You find a USB drive lying on the ground or anywhere else where you are unlikely to find the owner and pick it up. Is that stealing? You end up with a dead computer or other gadget either way.18574410 said:Well, people shouldn't steal. So in a way it's almost like their punishment.
What dude is going to leave computer-destroying USB drives on the ground? That's just wasting money and they're not getting anything out of it. -
InvalidError Reply
If you hate your boss, your ex, your neighbor, you may be tempted to 'accidentally' drop one in an area where (s)he's likely to be the first one to find it.18574586 said:What dude is going to leave computer-destroying USB drives on the ground? That's just wasting money and they're not getting anything out of it.
Some people don't mind collateral damage and wasting money to get some satisfaction.
-
turkey3_scratch Reply18574802 said:
If you hate your boss, your ex, your neighbor, you may be tempted to 'accidentally' drop one in an area where (s)he's likely to be the first one to find it.18574586 said:What dude is going to leave computer-destroying USB drives on the ground? That's just wasting money and they're not getting anything out of it.
Some people don't mind collateral damage and wasting money to get some satisfaction.
Ehh, I don't know. I took a criminology course, and the primary thing they wanted to get into our brains is that criminals don't plan out elaborate things like that. Of course there are rare occasions where crime is planned, but I don't possibly see this USB thing becoming a relevant issue where motherboard manufacturers need to become concerned. People should be much more concerned about the dangerous PSUs out there and regulating that stuff out of the market but this little USB thing seems to get more attention.
I think of this USB thing as a bomb. You can blow up your computer, literally. Just as you can put that USB in and kill it. Sure, you might not know the USB is a bomb, but I still see this being an extremely rare scenario, extremely rare.
But the number of PSUs out there killing hardware vs the number of USB sticks killing hardware is probably in a 100,000:1 ratio. -
InvalidError Reply
Tell that to the guy who used a calendar watch as the trigger for a bomb he put in his neighbor's basement under the dining room to blow his house up several months after the fact. IIRC, he failed to kill them because the watch drifted by several minutes and missed dinner time.18574812 said:Ehh, I don't know. I took a criminology course, and the primary thing they wanted to get into our brains is that criminals don't plan out elaborate things like that.
Some criminals do come up with sophisticated schemes.