Taping over your webcam might not be enough to stop hackers from spying on you — they can now use a device's ambient light sensor
Time to install another privacy shutter (or piece of tape).
That tape over your webcam may not be enough. Researchers at the Massachusetts Institute of Technology (MIT) have highlighted imaging privacy threats enabled by ambient light sensors, in a paper recently published in Science Advances. Device users concerned with security and privacy may be comforted by hardware solutions (shutters) and software permissions restricting webcam use. However, researchers have shown visual information can be gathered via one of the common ambient light sensors installed in many devices. These small sensors usually aren’t shuttered or disabled by users and are typically permission-free on a device level.
Ambient light sensors are categorized as low-risk by device makers and can often be accessed directly by software (or malware) without any permissions or privileges. Nevertheless, previous studies have shown such a rudimentary sensor can provide enough information to infer keystrokes on a virtual keyboard and steal a device PIN, about 80% of the time. The new research shows what an ambient light sensor can do when combined with an active light source component – namely the device' screen.
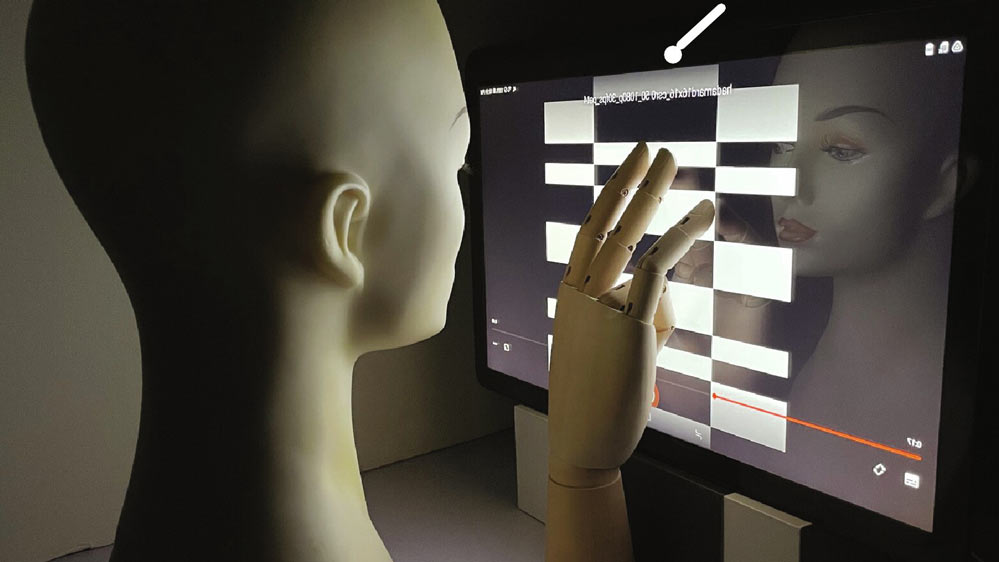
For their experiments, the MIT researchers used a Samsung Galaxy View 2. This rather old and large (17.3-inch) consumer tablet has its ambient light sensor next to the front-facing (selfie) camera, which is still a very common configuration.
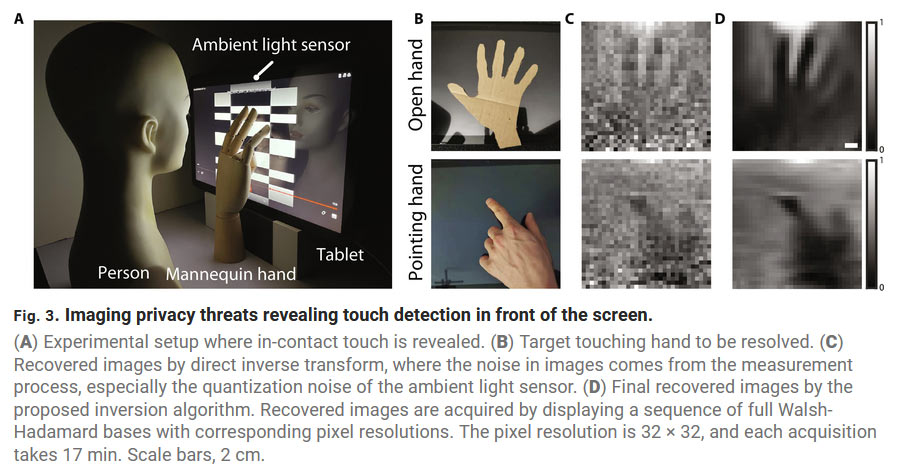
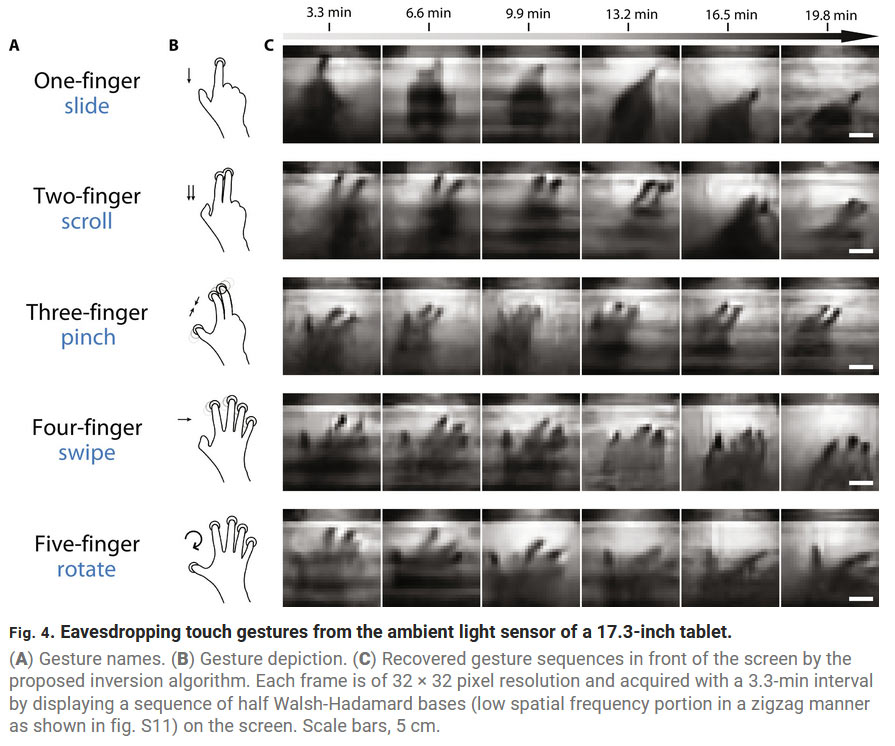
In brief, the researchers found that the position and shape of a user's hand could be determined using their technology. Also, hand gestures could be revealed, as could the number of fingers used and gesture directions. Lastly, it was possible to detect other shapes, like the presence of a human face, for example.
The scientists explained that the ambient light sensor reads the light emitted by the screen shining on a person’s face and being partially blocked by the hand / screen interaction. A whole lot of complicated math, aided by AI and image processing technology, was used by the researchers to deliver their results.
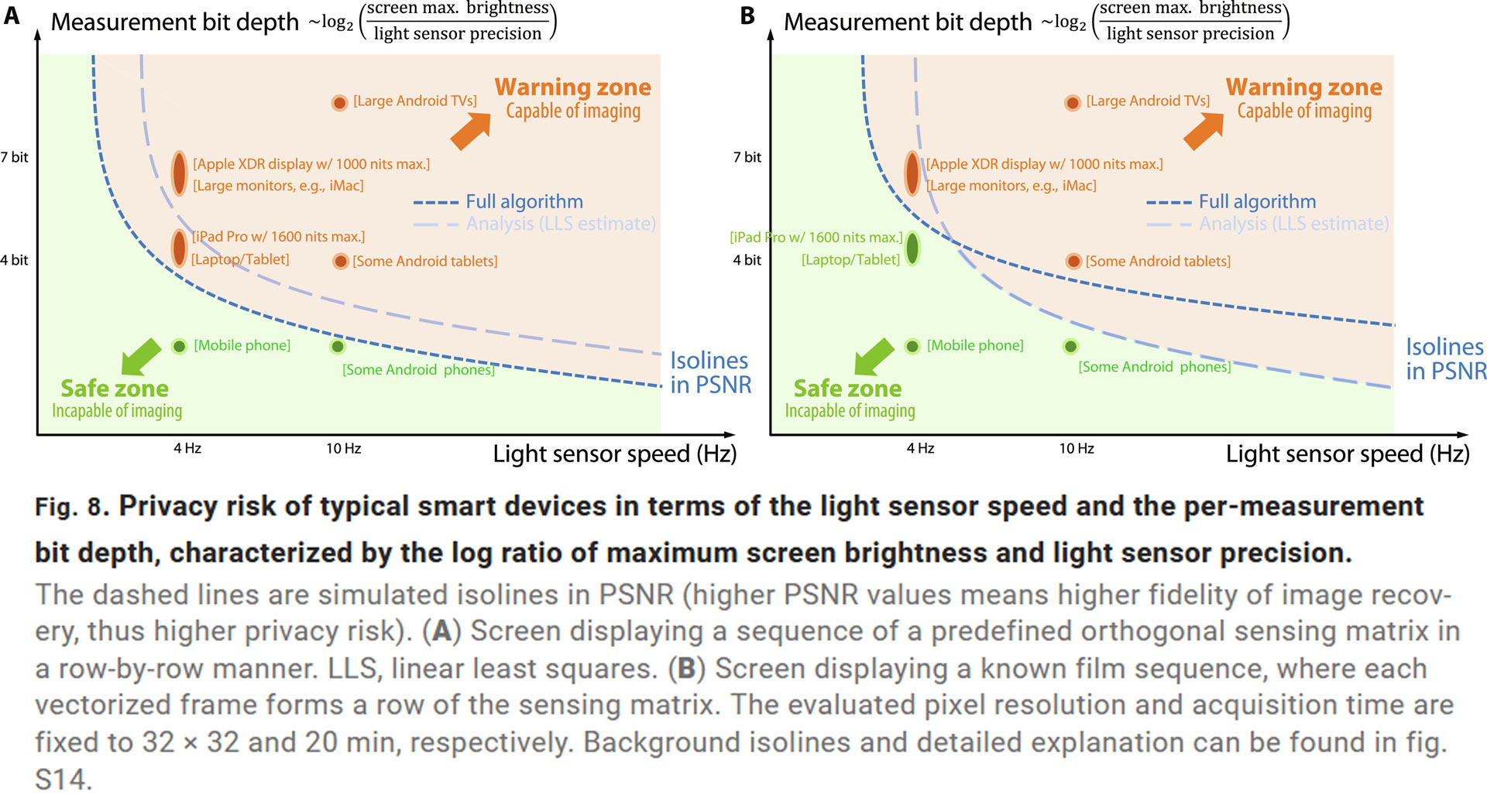
Every device offers a variation in light sensor speed and measurement bit depth, screen brightness, and light sensor precision so some devices will be more vulnerable to this ambient light sensor spy technique than others (see figure above). In the source article figures you will see some of the image captures took several minutes on the tablet device used. However, ambient light sensor imaging snooping tech is demonstrably real and could be refined and optimized.
As ambient light sensors are quite useful, we don’t want devices to get rid of them due to security concerns. Instead, the MIT researchers propose the following adjustments to their implementation:
- Rethink ambient light sensor device permissions
- Reduce sensor speed
- Reposition the sensor so it doesn’t face the user
The above security-conscious changes could easily be implemented by device manufacturers without any obvious drawbacks, so we hope to see them adopted going forward.
Get Tom's Hardware's best news and in-depth reviews, straight to your inbox.

Mark Tyson is a news editor at Tom's Hardware. He enjoys covering the full breadth of PC tech; from business and semiconductor design to products approaching the edge of reason.
-
Neilbob I just felt a legitimate shudder run down my spine when I read the words 'front-facing (selfie) camera'.Reply
Luckily, this is one situation in which I can classify myself as 100% secure, as there's no webcam anywhere near me and my phone is almost old enough to be used as a paving stone.
On a similar note, I witnessed someone walking into a lamp post the other day while overly absorbed in their phone. That cheered me up immensely for the remainder of the week. -
Geef The other options:Reply
Don't buy a monitor with a webcam.
If you use separate webcam, plug it into the front of your machine so you remember to unplug it when your done using it. -
paladinnz Holy over-sensationalized headlines Batman! It's an interesting idea, but not even a remotely viable method to "spy" on someone at the moment as it involves showing a known pattern full screen and capturing sensor data over several minutes. Who is going to take nearly 20 minutes to make a gesture on a device?Reply -
Alvar "Miles" Udell Good for proof of concept, but gaining access to a specific device, capturing a security PIN with the ambient light sensor, then actually gaining the device itself to take advantage of it presents about as much security risk as having your RAM stolen, deep frozen, and scraped for information.Reply
But I can see where this could present a problem on static devices, such as touch screen access panels. -
Blitz Hacker If someone has gone to this much trouble to see you in a webcam, I'm going to guess you have bigger problems on your hands.Reply -
caj If people really are concerned or.worried about security there a simple option in device manager called DISABLE device for the webcam.Reply
Been telling people to do.this for ages
Dont think there any option without UAC popping up and a hacker attempting to enable it to spy on u -
edzieba Lots of people talking about webcams who clearly did not read the article, the source, or even the headline.Reply -
ivan_vy Reply
webcameras with shutters, and if they have mics just unplug them, especially when doing banking or any other sensible operations.Geef said:The other options:
Don't buy a monitor with a webcam.
If you use separate webcam, plug it into the front of your machine so you remember to unplug it when your done using it. -
ivan_vy Reply
overstretching to what they can do with that data, itoh you can pinpoint someone to a place and time like the hunt of high interest people, add mics eavesdropping and the crossed data might be really useful.paladinnz said:Holy over-sensationalized headlines Batman! It's an interesting idea, but not even a remotely viable method to "spy" on someone at the moment as it involves showing a known pattern full screen and capturing sensor data over several minutes. Who is going to take nearly 20 minutes to make a gesture on a device?